BGP Port 179 Exploit Metasploit
In the world of computer networking, Border Gateway Protocol (BGP) plays a crucial role in facilitating the exchange of routing information between different autonomous systems (ASes). At the heart of BGP lies port 179, which serves as the communication channel for BGP peers. In this blog post, we will dive into the significance of BGP port 179, exploring its functionality, its role in establishing BGP connections, and its importance in global routing.
Port 179, also known as the Border Gateway Protocol (BGP) port, serves as a communication channel for routers to exchange routing information. It facilitates the establishment of connections between autonomous systems, enabling the efficient flow of data packets across the interconnected network.
Border Gateway Protocol (BGP) is a gateway protocol that enables the Internet to exchange routing information between autonomous systems (AS). This is accomplished through peering, and BGP uses TCP port 179 to communicate with other routers, known as BGP peers. Without it, networks would not be able to send and receive information with each other.
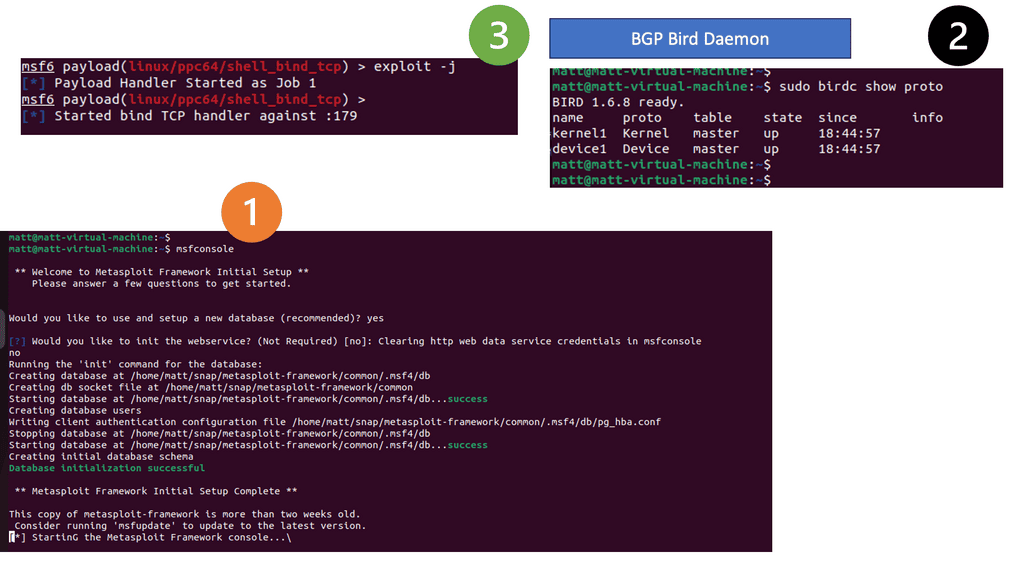
However, peering requires open ports to send and receive BGP updates that can be exploited. BGP port 179 exploit can be used with Metasploit, often referred to as port 179 BGP exploit Metasploit. Metasploit is a tool that can probe BGP to determine if there is a port 179 BGP exploit.
Matt Conran
Highlights: BGP Port 179 Exploit Metasploit
BGP Port 179
BGP is often described as the backbone of the internet. It’s a routing protocol that facilitates the exchange of routing information between autonomous systems (AS), which are large networks or groups of networks under a common administration. Think of it as a sophisticated GPS for data packets, directing them through the most efficient paths across the global network.
### How BGP Works
At its core, BGP operates by maintaining a table of IP networks or ‘prefixes’ which designate network reachability among autonomous systems. When a data packet needs to traverse the internet, BGP determines the best path based on various factors such as path length, policies, and rules set by network administrators. This dynamic routing mechanism ensures resilience and efficiency, adapting to network changes and congestion to maintain effective communication.
Introducing BGP & TCP Port 179:
The Border Gateway Protocol (BGP) is a standardized routing protocol that provides scalability, flexibility, and network stability. IPv4 inter-organization connectivity was a primary design consideration in public and private networks. BGP is the only protocol used to exchange networks on the Internet, which has more than 940,000 IPv4 and 180,000 IPv6 addresses.
Because of the large size of its tables, BGP does not advertise incremental updates or refresh network advertisements like OSPF and IS-IS. Due to a link flap, BGP prefers network stability. Along with several BGP features, BGP also operates over TCP ports and gains the advantage of using TCP as its transport for stability.
**The Importance of TCP Port 179 in BGP**
TCP port 179 is not just any port; it’s the lifeline for BGP operations. This port is used to initiate and maintain BGP sessions between routers. When routers need to exchange routing information, they establish a TCP connection via port 179. This connection is critical for the stability and reliability of the internet, as it ensures that data packets are routed efficiently. Without the proper functioning of TCP port 179, BGP would be unable to perform its essential role, leading to disruptions in internet service and connectivity issues.
**Security Considerations for TCP Port 179**
Given its crucial role in internet operations, TCP port 179 is often a target for malicious activities. Unauthorized access to this port can lead to serious security breaches, including the hijacking of data routes or denial of service attacks. It is vital for network administrators to implement robust security measures to protect this port. This includes using firewalls, intrusion detection systems, and regular monitoring of network traffic to detect and respond to any suspicious activities promptly.
**BGP neighbor relationships**
– BGP uses TCP port 179 to communicate with other routers. TCP handles fragmentation, sequencing, and reliability (acknowledgment and retransmission). A recent implementation of BGP uses the do-not-fragment (DF) bit to prevent fragmentation.
– Because IGPs form sessions with hellos that cannot cross network boundaries (single hop only), they follow the physical topology. The BGP protocol uses TCP, which can cross network boundaries (i.e., multi-hop). Besides neighbor adjacencies that are directly connected, BGP can also form adjacencies that are multiple hops apart.
– An adjacency between two BGP routers is referred to as a BGP session. To establish the TCP session with the remote endpoint, the router must use an underlying route installed in the RIB (static or from any routing protocol).
EBGP vs IBGP
eBGP – Bridging Networks: eBGP, or external BGP, is primarily used for communication between different autonomous systems (AS). Autonomous systems are networks managed and controlled by a single organization. eBGP allows these autonomous systems to exchange routing information, enabling them to communicate and share data across different networks.
iBGP – Enhancing Internal Routing: Unlike eBGP, iBGP, or internal BGP, is used within a single autonomous system. It facilitates communication between routers within the same AS, ensuring efficient routing of data packets. iBGP enables the exchange of routing information between routers, allowing them to make informed decisions on the best path for data transmission.
While eBGP and iBGP serve the purpose of routing data, there are significant differences between the two protocols. The primary distinction lies in their scope: eBGP operates between different autonomous systems, whereas iBGP operates within a single AS. EBGP typically uses external IP addresses for neighbor relationships, while iBGP utilizes internal IP addresses.
Significance of TCP port 179
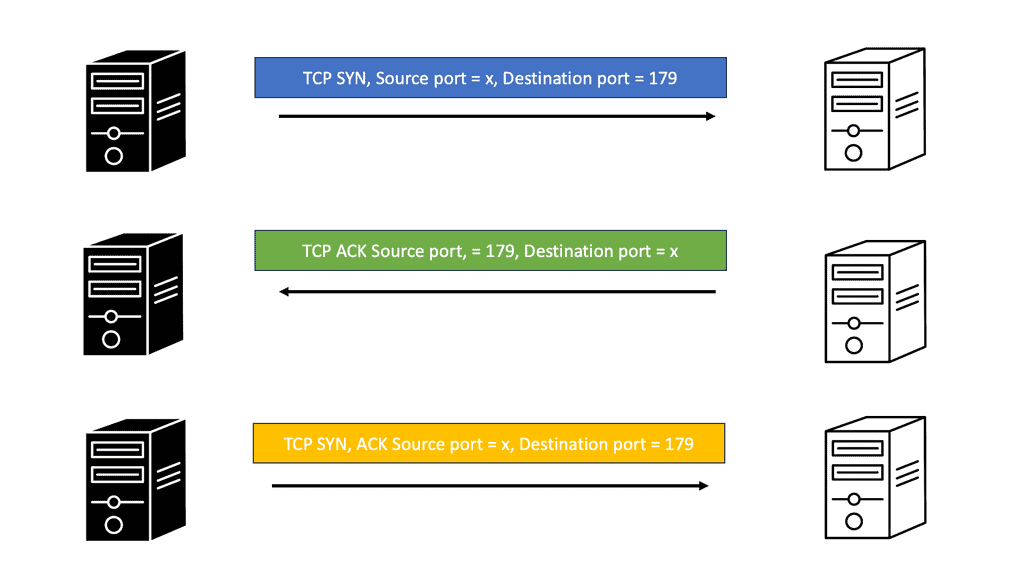
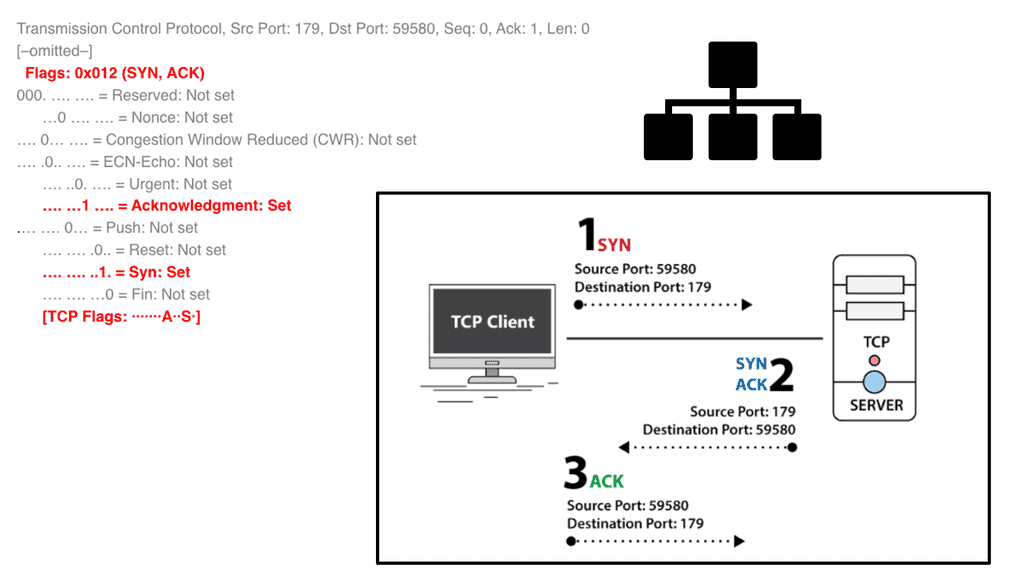
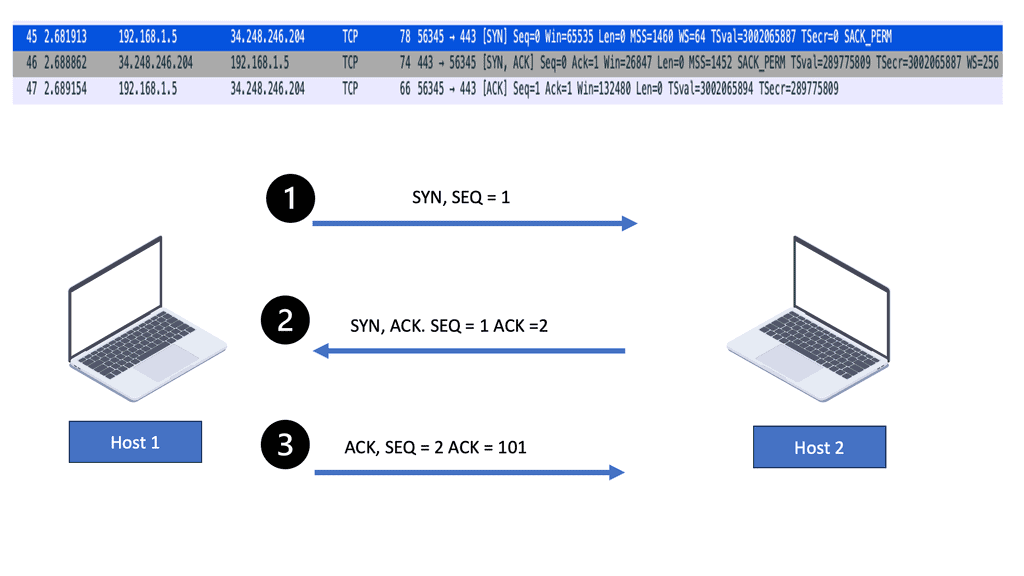
According to who originates the session, BGP uses different sources and destinations other than 179. Essentially, BGP is a client-server protocol based on TCP. To establish a connection with a TCP server, a TCP client first sends a TCP SYN packet with the destination port as the well-known port. A SYN request is essentially a request to open a session.
When the server permits the session, it will respond with a TCP SYN ACK stating that it acknowledges the request to open the session and wants to open it. The server uses the well-known port as the source port and a randomly negotiated destination port in this SYN-ACK response. The client acknowledges the server’s response with a TCP ACK in the last step of the three-way handshake.
From a BGP perspective, TCP clients and servers are routers. The “client” router initiates the BGP session by sending a request to the server with a destination port of 179 and a random source port X. Server responds with source port 179 and destination port X. Therefore, all client-server traffic uses destination 179, while server-client traffic uses source 179.
Port 179 and Security
BGP port 179 plays a significant role in securing BGP sessions. BGP routers implement various mechanisms to ensure the authenticity and integrity of the exchanged information. One such mechanism is TCP MD5 signatures, which provide a simple yet effective way to authenticate BGP peers. By enabling TCP MD5 signatures, routers can verify the source of BGP messages and prevent unauthorized entities from injecting false routing information into the network.
Knowledge Check: TCP MD5 Signatures
### The Need for TCP MD5 Signatures
As the internet grew, so did the complexity and number of threats targeting its infrastructure. One major concern is the integrity and authenticity of BGP sessions. Without protection, malicious actors can hijack BGP sessions, leading to traffic misdirection and data interception. TCP MD5 signatures help mitigate this risk by adding a layer of security. They provide a mechanism for authenticating BGP messages, ensuring that the data received is indeed from a trusted source.
### How TCP MD5 Signatures Work
TCP MD5 signatures operate by hashing the TCP segment, including the BGP message, using the MD5 algorithm. Both the sender and receiver share a secret key, which is used in the hashing process. When a BGP message is received, the receiver computes the MD5 hash using the same secret key. If the computed hash matches the one sent with the message, the message is considered authentic. This method effectively prevents unauthorized entities from injecting malicious traffic into BGP sessions.
Advanced BGP TopicS
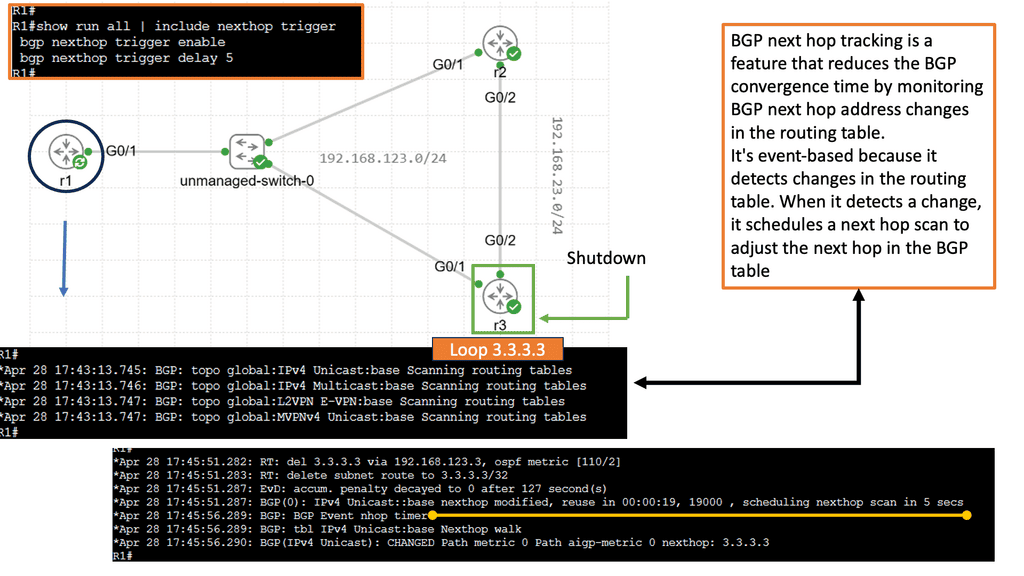
Understanding BGP Next Hop Tracking:
BGP Next Hop Tracking is a mechanism that enables routers to track the reachability of the next hop IP address. When a route is learned via BGP, the router verifies the reachability of the next hop and updates its routing table accordingly. This information is crucial for making accurate routing decisions and preventing traffic blackholing or suboptimal routing paths.
By utilizing BGP Next Hop Tracking, network operators can enjoy several benefits. First, it enhances routing stability by ensuring that only reachable next hops are used for forwarding traffic. This helps avoid routing loops and suboptimal paths.
Second, it provides faster convergence during network failures by quickly detecting and updating routing tables based on the reachability of next hops. Lastly, BGP Next Hop Tracking enables better troubleshooting capabilities by identifying faulty or unreachable next hops, allowing network administrators to take appropriate actions.
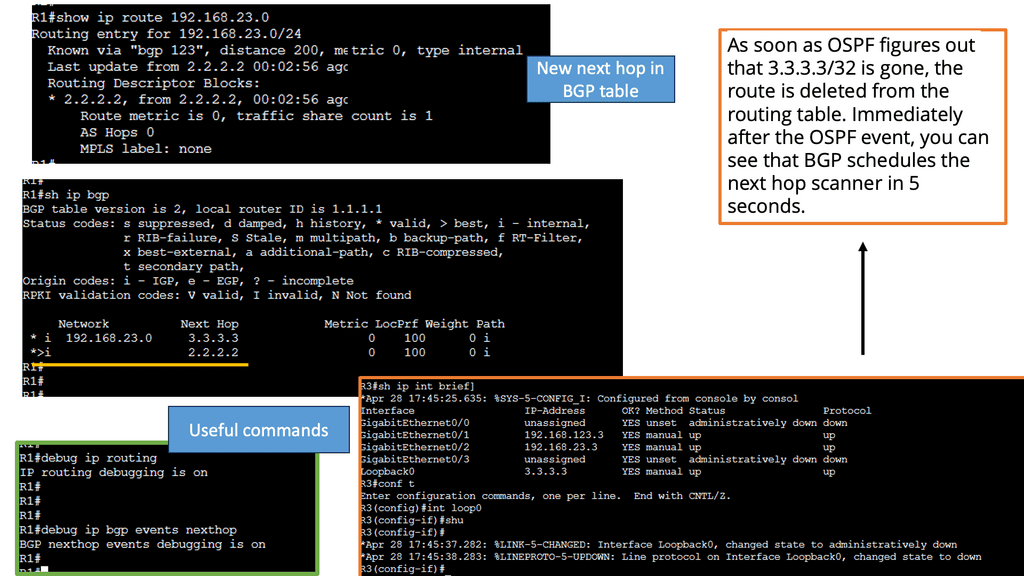
Once those 5 seconds have expired, the next hop address will be changed to 2.2.2.2 (R2) and added to the routing table. This process is much faster than the BGP scanner, which runs every 60 seconds.
Here’s what the BGP table now looks like:
Each route in the BGP table must have a reachable next hop. Otherwise, the route cannot be used. Every 60 seconds, BGP checks all routes in the BGP table. The BGP scanner calculates the best path, checks the next hop addresses, and determines if the next hops can be reached. For performance reasons, 60 seconds is long. When something goes wrong with a next hop during the 60 seconds between two scans, we have to wait until the next scan begins to resolve the issue. In the meantime, we may have black holes and/or routing loops.
The next hop tracking feature in BGP reduces convergence times by monitoring changes in the next hop address in the routing table.
The next hop scan is delayed by 5 seconds after detecting a change. Notice the 5-second timer in the images above. The next hop tracking system also supports dampening penalties. Next-hop scans that keep changing in the routing table are delayed.
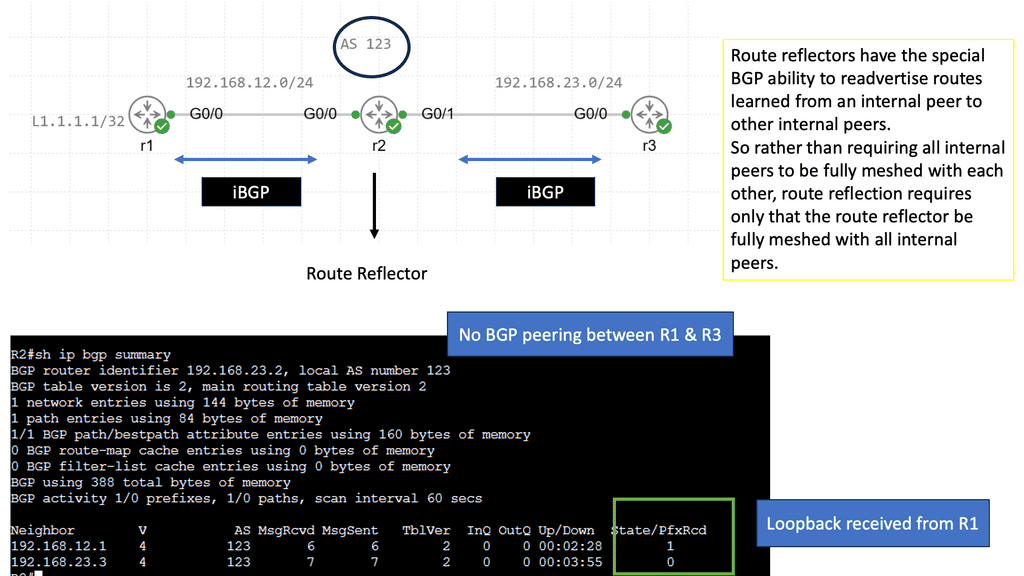
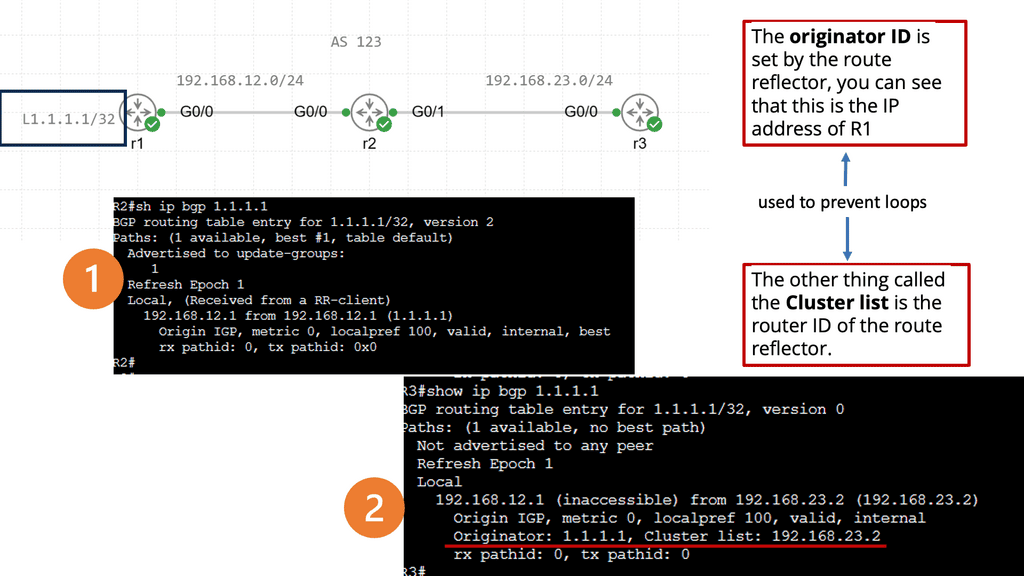
Understanding BGP Route Reflection:
BGP route reflection is a technique used in BGP networks to address the scalability issues that arise when multiple routers are involved in the routing process. It allows for the efficient distribution of routing information without overwhelming the network with unnecessary updates. Network administrators can optimize their network’s performance and stability by understanding the basic principles of BGP route reflection.
Enhanced Scalability: BGP route reflection provides a scalable solution for large networks by reducing the number of BGP peering relationships required. This leads to simplified network management and improved performance.
Reduced Resource Consumption: BGP route reflection eliminates the need for full mesh connectivity between routers. This reduces resource consumption, such as memory and processing power, resulting in cost savings for network operators.
Improved Convergence Time: BGP route reflection improves overall network convergence time by reducing the propagation delay of routing updates. This is achieved by eliminating the need for full route propagation across the entire network, resulting in faster convergence and improved network responsiveness.
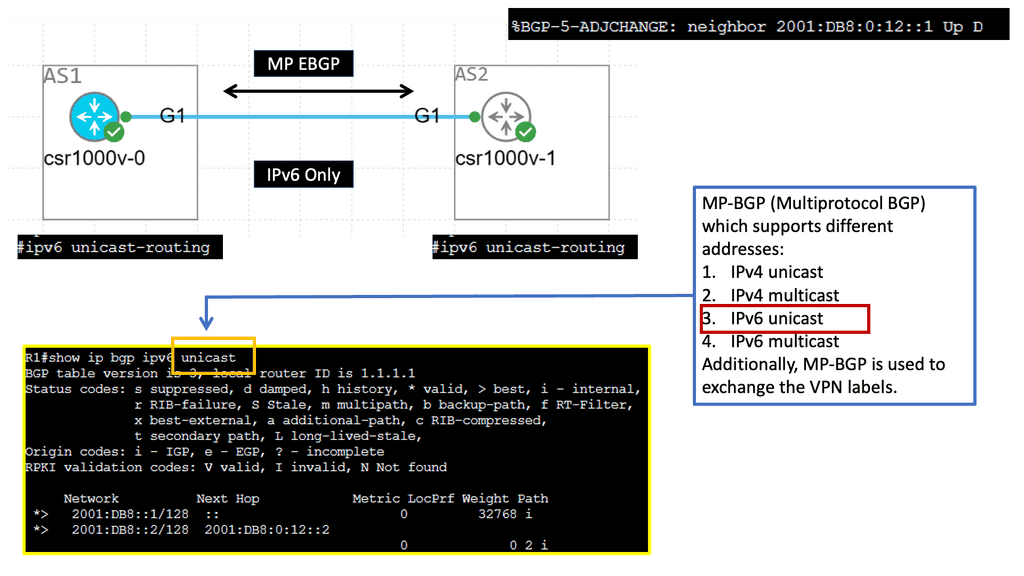
Example: MP-BGP with IPv6
Understanding MP-BGP
MP-BGP, short for Multiprotocol Border Gateway Protocol, is an extension of the traditional BGP protocol. It enables the simultaneous routing and exchange of multiple network layer protocols. MP-BGP facilitates smooth transition and interoperability between these protocols by supporting the coexistence of IPv4 and IPv6 addresses within the same network infrastructure.
IPv6, the successor to IPv4, offers a vast address space, improved security features, and enhanced mobility support. Its 128-bit address format allows for an astronomical number of unique addresses, ensuring the internet’s future scalability. With MP-BGP, organizations can harness the full potential of IPv6 by seamlessly integrating it into their existing network infrastructure.
To establish MP-BGP with IPv6 adjacency, several steps need to be followed. First, ensure that your network devices support MP-BGP and IPv6 routing capabilities. Next, configure the appropriate MP-BGP address families and attributes. Establish IPv6 peering sessions between BGP neighbors and enable the exchange of IPv6 routing information. Finally, verify the connectivity and convergence of the MP-BGP with IPv6 adjacency setup.
Related: Before you proceed, you may find the following posts helpful:
- IP Forwarding
- BGP SDN
- Redundant Links
- IPv6 Host Exposure
- Forwarding Routing Protocols
- Cisco DMVPN
- Dead Peer Detection
BGP Port 179 Exploit Metasploit
BGP Port 179: The Communication Channel
Port 179 is the well-known port for BGP communication, acting as the gateway for BGP messages to flow between BGP routers. BGP, a complex protocol, requires a reliable and dedicated port to establish connections and exchange routing information. By utilizing port 179, BGP ensures its communication is secure and efficient, enabling routers to establish and maintain BGP sessions effectively.
Establishing BGP Connections
When two BGP routers wish to connect, they initiate a TCP connection on port 179. This connection allows the routers to exchange BGP update messages containing routing information such as network prefixes, path attributes, and policies. Routers build a comprehensive view of the network’s topology by exchanging these updates and making informed decisions on route traffic.
**Section 1: The Basics of BGP Neighbors**
At its core, BGP neighbors—often called peers—are routers that have been configured to exchange BGP routing information. This exchange is essential for maintaining a coherent and functioning network topology. Establishing these neighbor relationships is the first step in building a robust BGP infrastructure. The process involves configuring specific IP addresses and using unique Autonomous System Numbers (ASN) to identify each participating network.
**Section 2: Configuration Steps for Establishing BGP Neighbors**
To establish a BGP neighbor relationship, network administrators must follow a series of configuration steps. First, ensure that both routers can reach each other over the network. This often involves configuring static routes or using an internal routing protocol. Next, initiate the BGP process by specifying the ASN for each router. Finally, declare the IP address of the neighboring router and confirm the configuration. This setup allows the routers to begin the exchange of routing information.
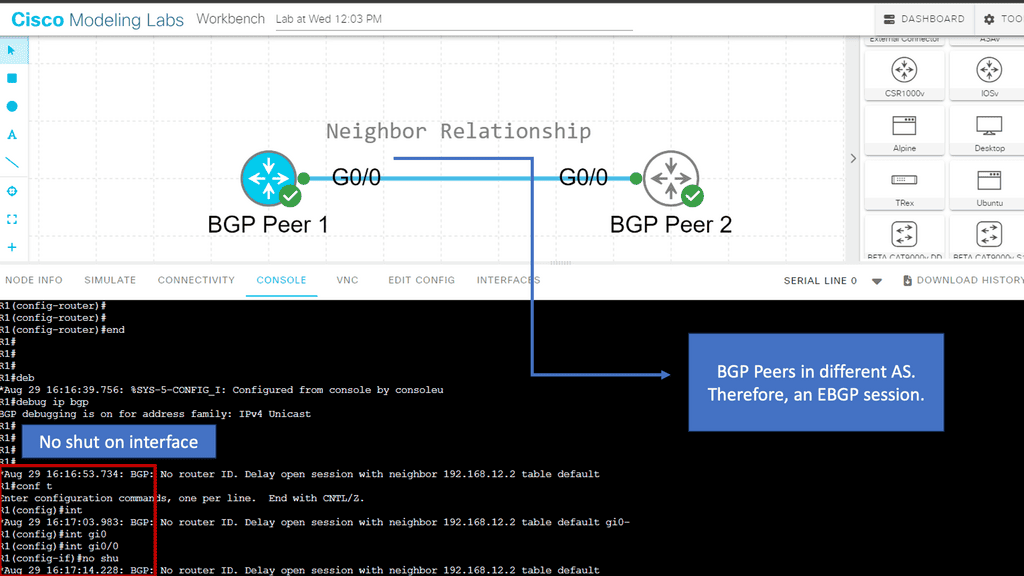
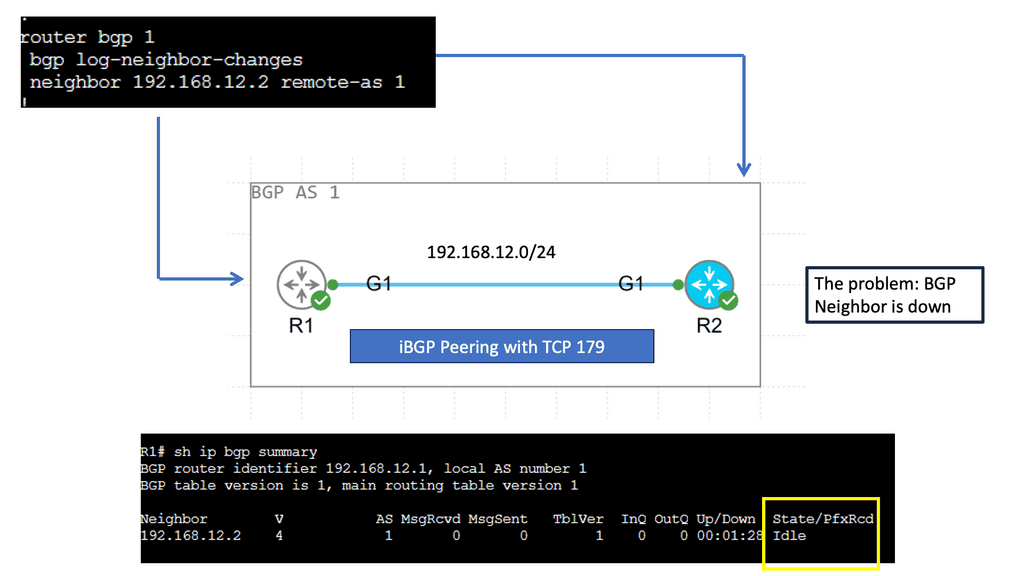
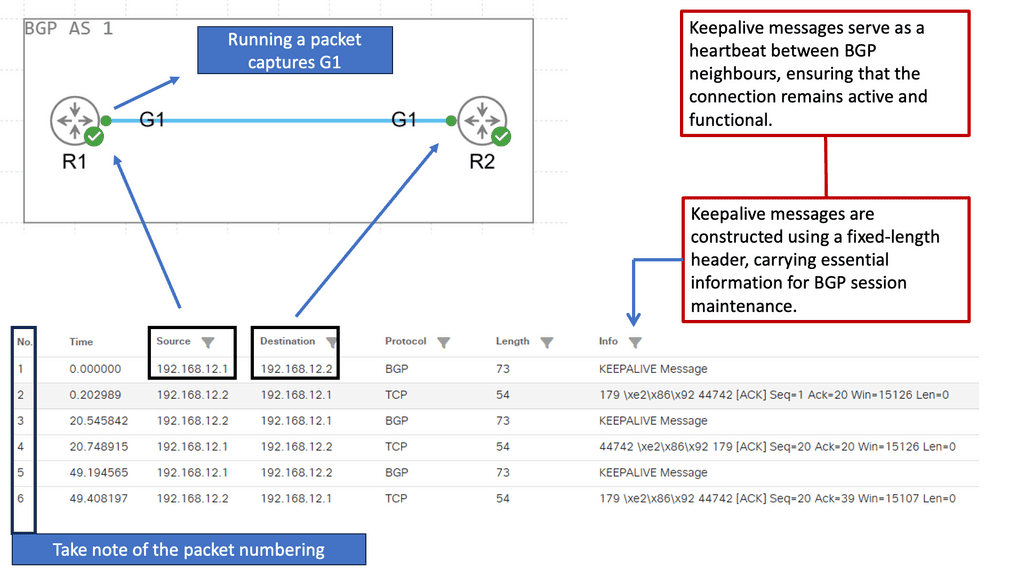
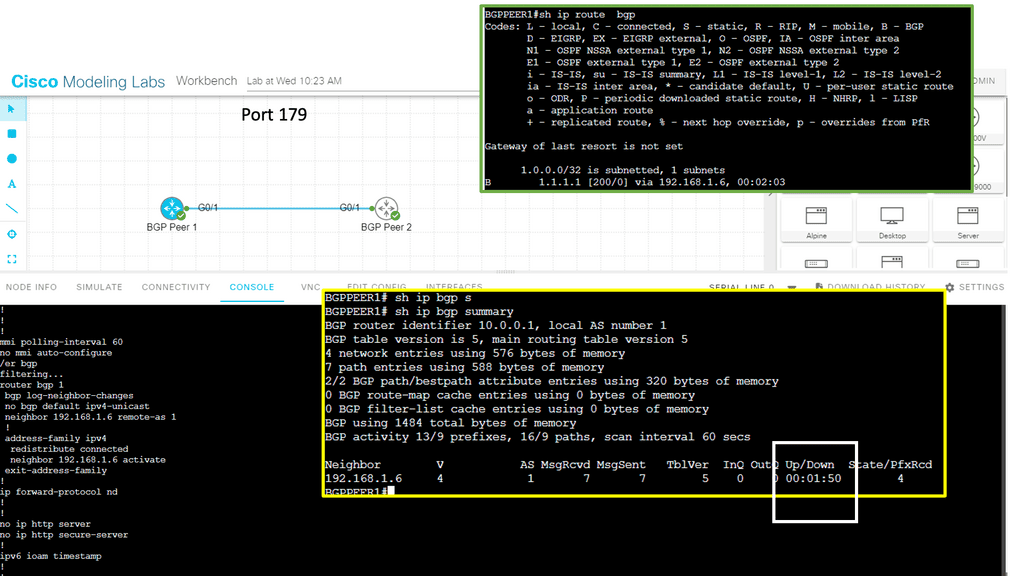
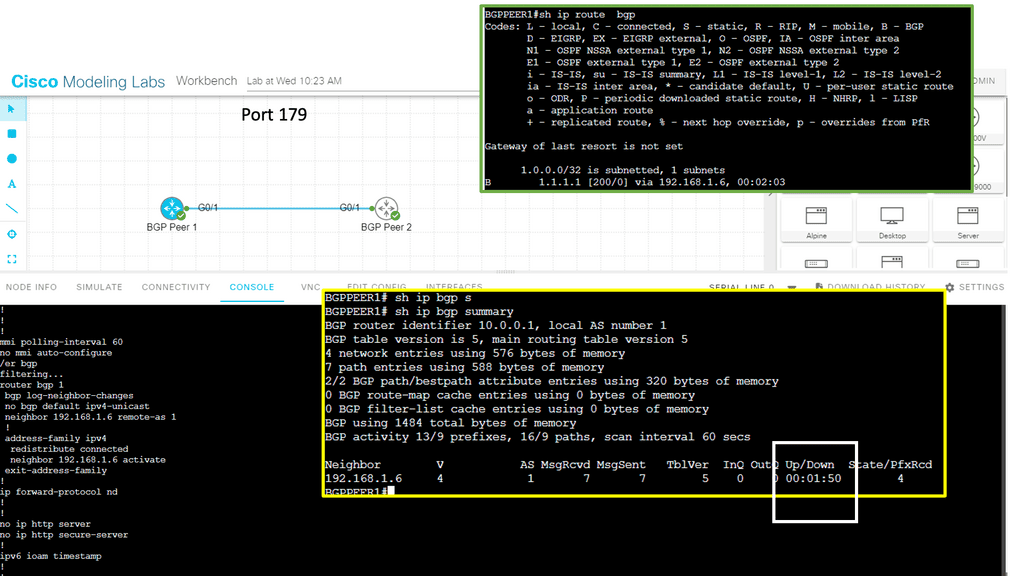
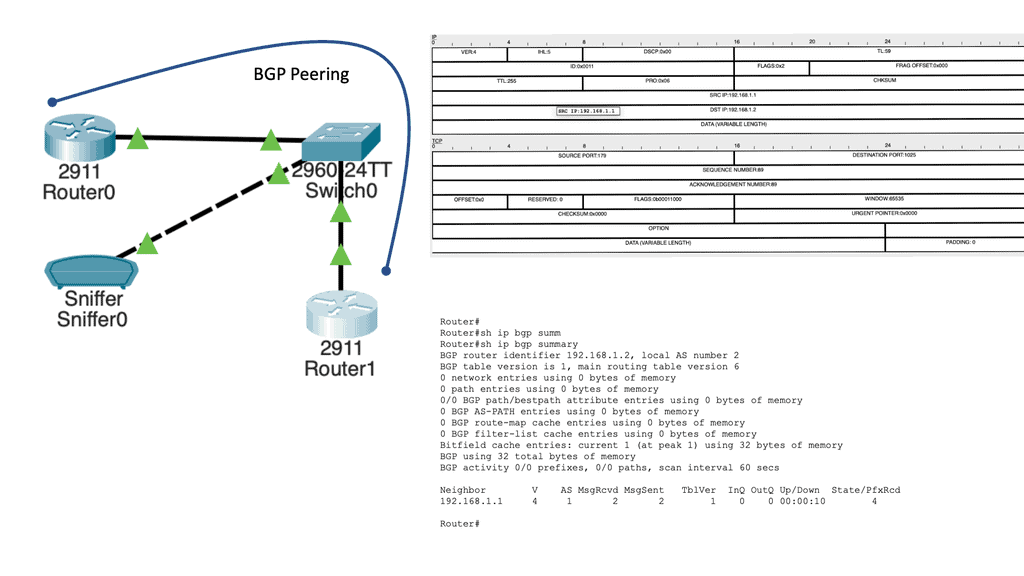
Guide: BGP Port 179
In the following lab guide on port 179, we have two BGP peers labeled BGP Peer 1 and BGP Peer 2. These BGP peers have one Gigabit Ethernet link between them. I have created an iBGP peering between the two peers, where the AS numbering is the same for both peers.
Note:
Remember that a full mesh iBGP peering is required within an AS because iBGP routers do not re-advertise routes learned via iBGP to other iBGP peers. This is called the split horizon rule and is a routing-loop-prevention mechanism. Since we have two iBGP peers, this is fine. The BGP peerings are over TCP port 179, and I have redistributed connected so we have a route in the BGP table.
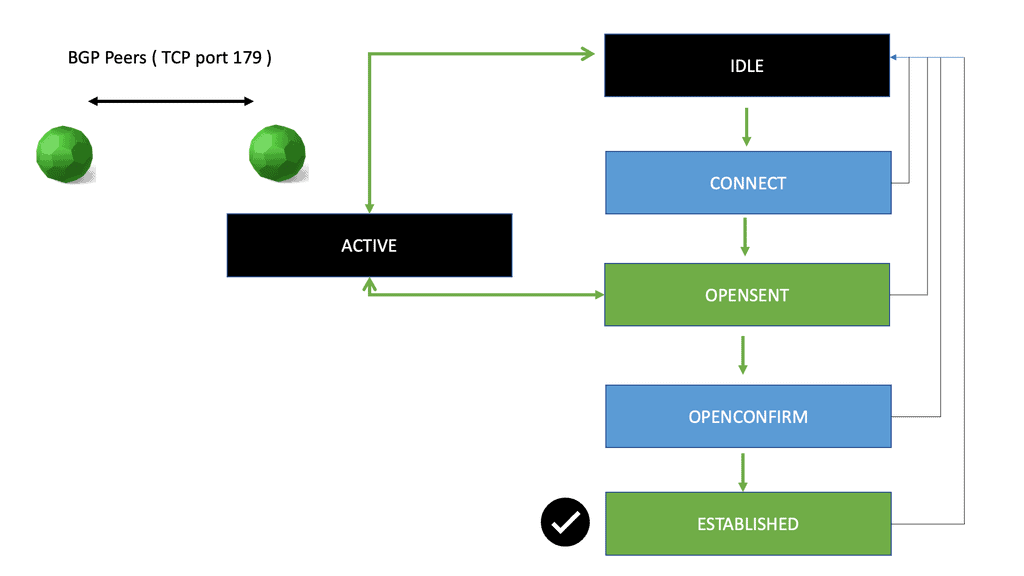
BGP Neighbor States
Unlike IGPs such as EIGRP and OSPF, BGP establishes sessions differently. In IGPs, neighbors are dynamically discovered as they bootstrap themselves to the topology. To peer with another BGP speaker, BGP speakers must explicitly be configured to do so. Furthermore, BGP must wait for a reliable connection to be established before proceeding. To overcome some issues with its predecessor, EGP, BGP was enhanced to address this requirement.
For two routers to establish this connection, both sides must have an interface configured for BGP and matching BGP settings, such as an Autonomous System number. Once the two routers have established a BGP neighbor relationship, they exchange routing information and can communicate with each other as needed.
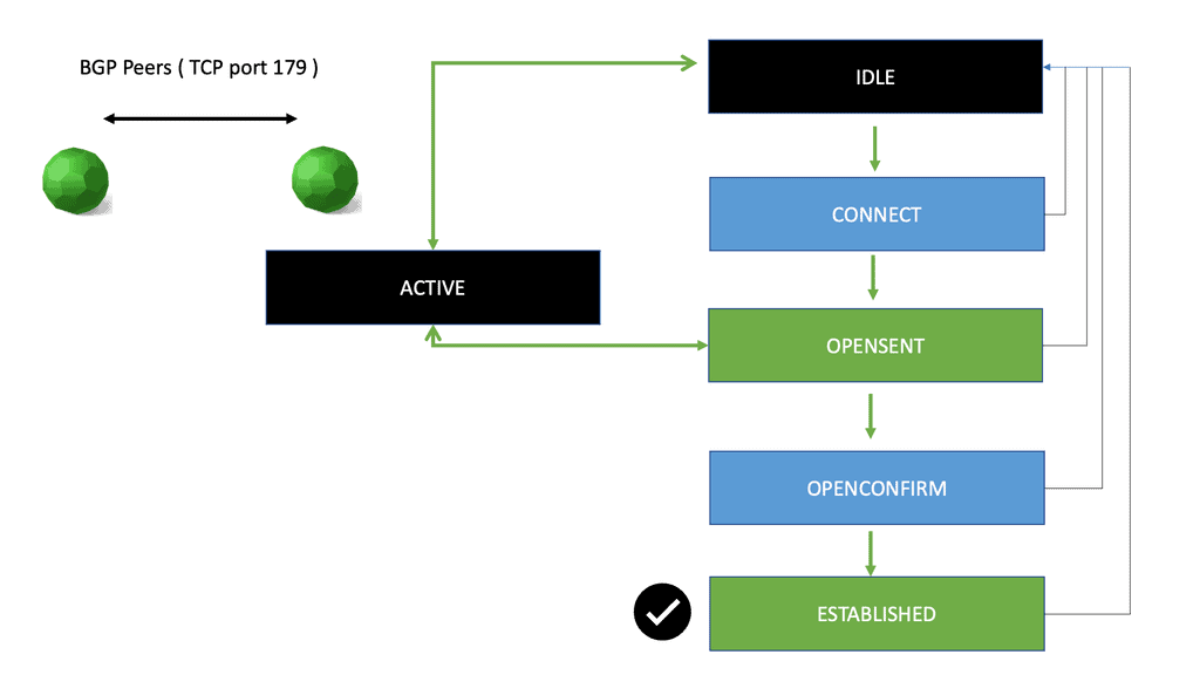
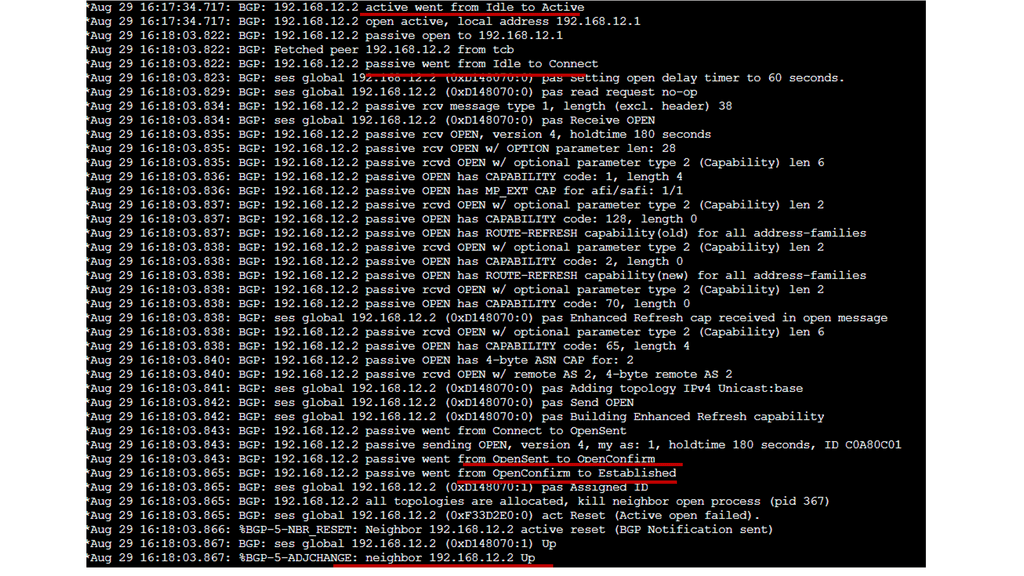
BGP neighbor states represent the different stages of the relationship between BGP routers. These states are crucial in establishing and maintaining connections for exchanging routing information. Idle, Connect, OpenSent, and Established are the four neighbor states. Each state signifies a specific phase in the BGP session establishment process.
- Idle State:
The first state in the BGP neighborship is the Idle state. In this state, a BGP router does not know any neighboring routers. It is waiting to establish a connection with a potential BGP peer. When a router is in the Idle state, it periodically sends out keepalive messages to potential peers, hoping to initiate the neighborship process.
- Connect State:
Once a router receives a keepalive message from a potential BGP neighbor, it transitions to the Connect state. The router attempts to establish a TCP connection with the neighboring router in this state. The Connect state lasts until the TCP connection setup is successful, after which the router moves to the OpenSent state.
- OpenSent State:
In the OpenSent state, the BGP router sends a neighboring router an Open message containing information about its capabilities and parameters. The router waits for a response from the neighbor. If the received Open message is acceptable, the router moves to the OpenConfirm state.
- OpenConfirm State:
In the OpenConfirm state, BGP routers exchange Keepalive messages to confirm that the TCP connection works correctly. The routers also negotiate various BGP parameters during this state. Once both routers have confirmed the connection, they move to the Established state.
- Established State:
The Established state is the desired state for BGP neighborship. The routers have successfully established a BGP peering relationship in this state and are actively exchanging routing information. They exchange updates, keepalives, and notifications, enabling them to make informed routing decisions. This state is crucial for the stability and integrity of the overall BGP routing infrastructure.
Below, the BGP state moves from Idle to Active and OpenSent. Some Open messages are sent and received; the BGP routers exchange some of their capabilities. From there, we move to the OpenConfirm and Established state. Finally, you see the BGP neighbor as up. The output of these debug messages is friendly and easy to read. If, for some reason, your neighbor’s adjacency doesn’t appear, these debugs can be helpful to solve the problem.
Port Numbers
Let’s go back to the basics for just a moment. First, we have port numbers, which represent communication endpoints. Port numbers are assigned 16-bit integers (see below) that identify a specific process or network service running on your network. These are not assigned randomly, and IANA is responsible for internet protocol resources, including registering used port numbers for well-known internet services.
- Well Known Ports: 0 through 1023.
- Registered Ports: 1024 through 49151.
- Dynamic/Private: 49152 through 65535.
So, we have TCP port numbers and UDP port numbers. We know TCP enables hosts to establish a connection and exchange data streams reliably. Depending on the application, TCP Port 179 may use a defined protocol to communicate. For example, BGP is an application that uses TCP Port 179.
BGP chose this port for a good reason. TCP guarantees data delivery compared to UDP, and packets will be delivered on port 179 in the same order they were sent. So, we have guaranteed communication on TCP port 179, compared to UDP port 179. UDP port 179 would not have guaranteed communication in the same way as TCP.
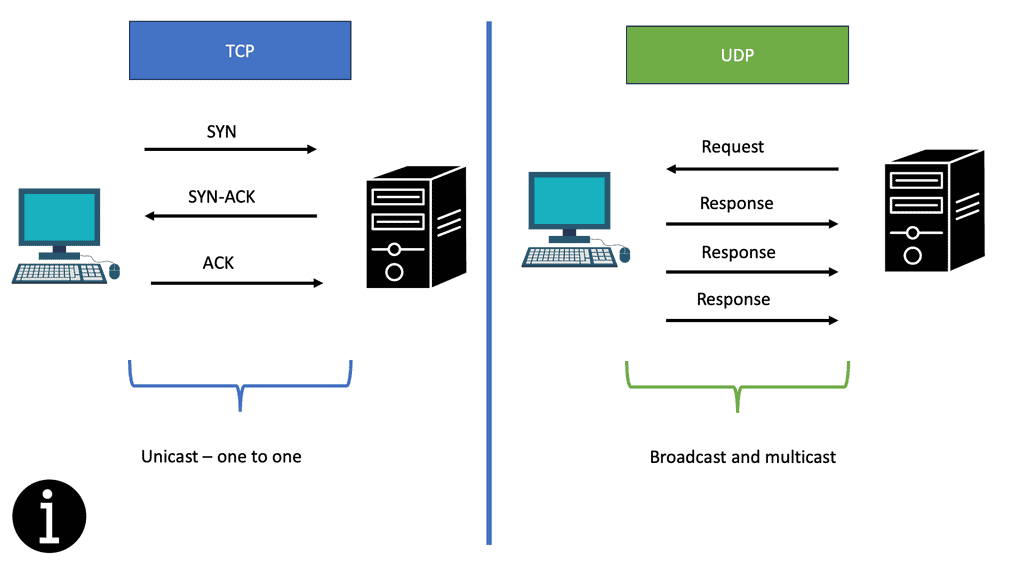
UDP vs. TCP
UDP and TCP are internet protocols but have different features and applications. UDP, or User Datagram Protocol, is a lightweight and fast protocol used for applications that do not require reliable data transmission. UDP is a connectionless protocol that does not establish a dedicated end-to-end connection before sending data. Instead, UDP packets are sent directly to the recipient without any acknowledgment or error checking.
Knowledge Check: TCP vs UDP
UDP, often referred to as a “connectionless” protocol, operates at the transport layer of the Internet Protocol Suite. Unlike TCP, UDP does not establish a formal connection between the sender and receiver before transmitting data. Instead, it focuses on quickly sending smaller packets, known as datagrams, without error-checking or retransmission mechanisms. This makes UDP a lightweight and efficient protocol ideal for applications where speed and minimal overhead are crucial.
**The Reliability of TCP**
In contrast to UDP, TCP is a “connection-oriented” protocol that guarantees reliable data delivery. By employing error-checking, acknowledgment, and flow control, TCP ensures that data is transmitted accurately and in the correct order. This reliability comes at the cost of increased overhead and potential latency, making TCP more suitable for applications that prioritize data integrity and completeness, such as file transfers and web browsing.
**Key Differences Between TCP and UDP**
The primary differences between TCP and UDP lie in their reliability, connection orientation, and speed. TCP’s connection-oriented approach ensures reliable data transfer with error correction, making it slower but more accurate. In contrast, UDP’s connectionless nature allows for quick transmission, sacrificing reliability for speed.
Another difference is in how they handle data flow. TCP uses flow control mechanisms to prevent network congestion, while UDP does not, allowing it to send data without waiting for acknowledgments. This makes TCP more suitable for applications requiring stable connections, whereas UDP is better for scenarios needing rapid data exchange.
**Applications and Use Cases**
Understanding when to use TCP and UDP is essential for optimizing network performance. TCP’s reliability makes it perfect for applications like web servers, email clients, and FTP services, where data integrity is crucial. On the other hand, UDP’s speed is beneficial for live broadcasts, online gaming, and voice communication, where delays can disrupt the user experience.
Use Cases and Applications
1. UDP:
– Real-time streaming: UDP’s low latency and reduced overhead suit real-time applications like video and audio streaming.
– Online gaming: The fast-paced nature of online gaming benefits from UDP, providing quick updates and responsiveness.
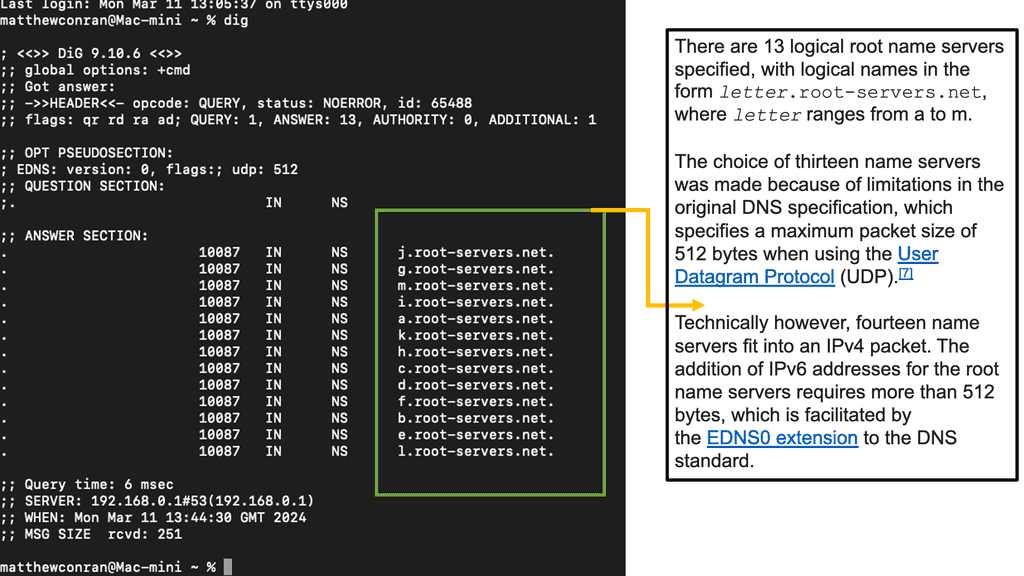
– DNS (Domain Name System): UDP is commonly used for DNS queries, where quick responses are essential for efficient web browsing.
2. TCP:
– Web browsing: TCP’s reliability ensures that web pages and their resources are fully and accurately loaded.
– File transfers: TCP’s error-checking and retransmission mechanisms guarantee the successful delivery of large files.
– Email delivery: TCP’s reliability ensures that emails are transmitted without loss or corruption.
The TCP 3-Way Handshake
TCP, or Transmission Control Protocol, is a more reliable protocol for applications requiring error-free data transmission and guaranteed message delivery. TCP is a connection-oriented protocol that establishes a dedicated end-to-end connection between the sender and receiver before sending data. TCP uses a three-way handshake to establish a connection and provides error checking, retransmission, and flow control mechanisms to ensure data is transmitted reliably and efficiently.
In summary, UDP is a lightweight and fast protocol suitable for applications that do not require reliable data transmissions, such as real-time streaming media and online gaming. TCP is a more reliable protocol ideal for applications requiring error-free data transmissions and guaranteed message delivery, such as web browsing, email, and file transfer.
BGP and TCP Port 179
In the context of BGP, TCP is used to establish a connection between two routers and exchange routing information. When a BGP speaker wants to connect with another BGP speaker, a TCP SYN message is sent to the other speaker. If the other speaker is available and willing to join, it sends a SYN-ACK message. The first speaker then sends an ACK message to complete the connection.
Once the connection is established, the BGP speakers can exchange routing information. BGP uses a set of messages to exchange information about the networks that each speaker can reach. The messages include information about the network prefix, the path to the network, and various attributes that describe the network.
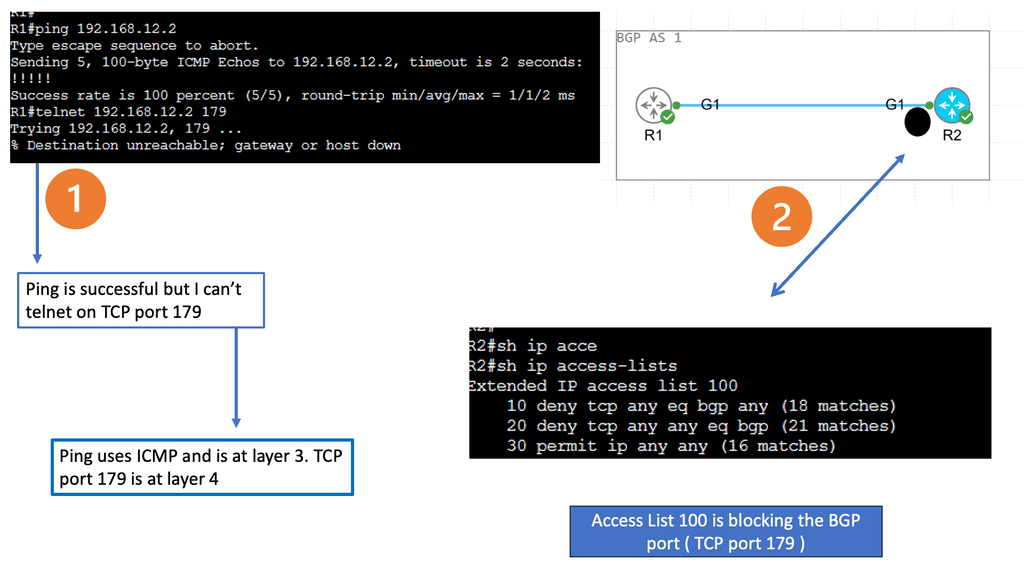
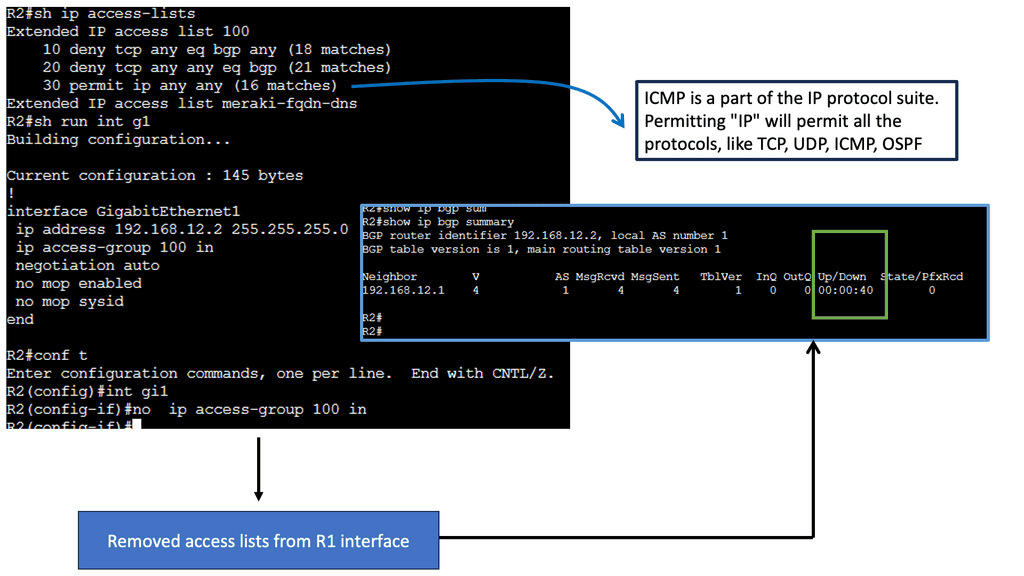
Guide: Filtering TCP Port 179
The following will display the effects of filtering BGP port 179. Below is a simple design of 2 BGP peers—plain and simple. The routers use the directly connected IP addresses for the BGP neighbor adjacency. However, we have a problem: the BGP neighbor relationship is down, and we are not becoming neighbors. What could be wrong? We use the directly connected interfaces so nothing could go wrong except for L2/L2 issues.
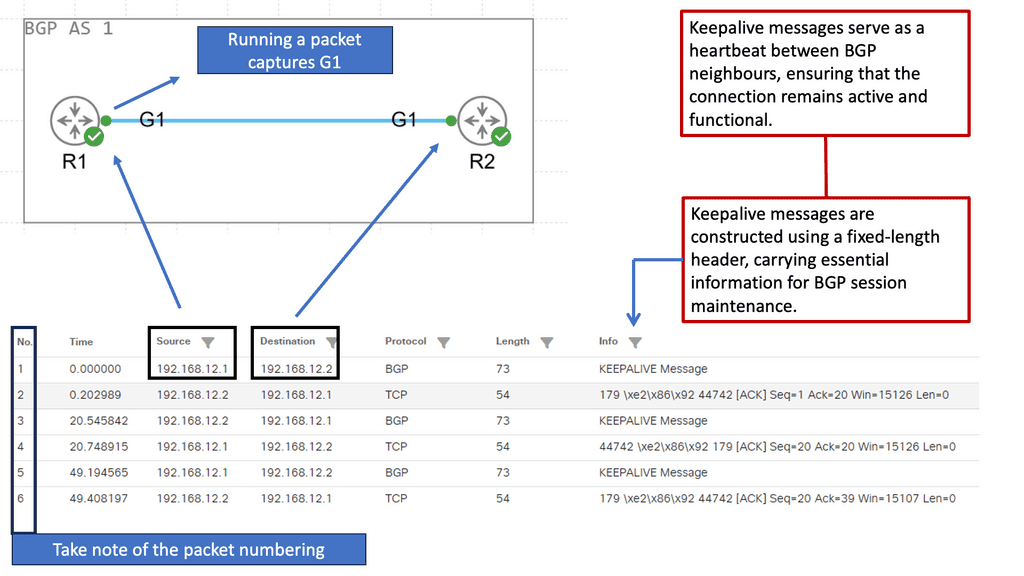
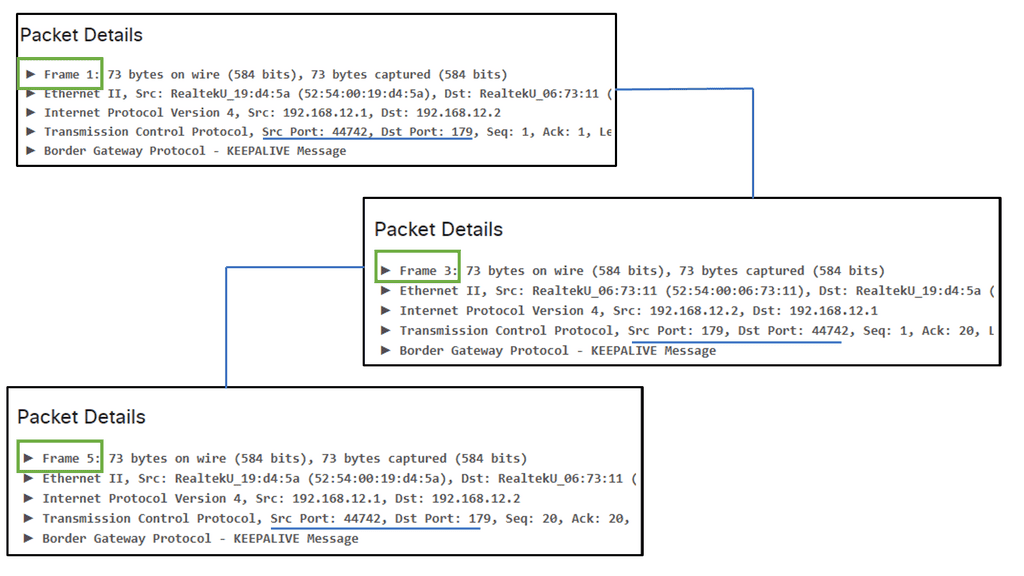
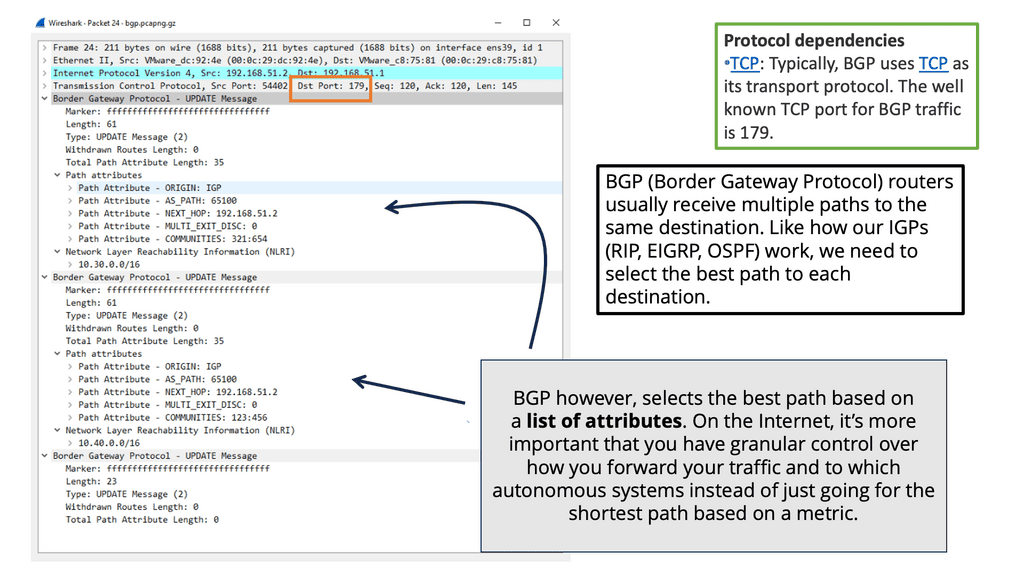
Guide: BGP Update Messages
In the following lab guide, you will see we have two BGP peers. There is also a packet capture that displays the BGP update messages. BGP uses source and destination ports other than 179, depending on who originates the session. BGP is a standard TCP-based protocol that runs on client and server computers.
A successful TCP connection must exist before negotiating a BGP session between two peers. TCP provides a reliable transmission medium between the two peers and allows the exchange of BGP-related messages. A broken TCP connection also breaks the BGP session. BGP sessions are not always established after successful TCP connections.
1: – In BGP, the session establishment phase operates independently of TCP, i.e., BGP rides on top of TCP. As a result, two peers may form a TCP connection but disagree on BGP parameters, resulting in a failed peering attempt. The BGP FSM oscillates between IDLE, ACTIVE, and CONNECT states while establishing the TCP connection.
2: – To establish a connection with a TCP server, a TCP client first sends a TCP SYN packet with the destination port as the well-known port. In this first SYN, we are requesting to open a session. The server will reply with a TCP SYN ACK if it permits the session to open. It also wants to open a session. The source port of this SYN-ACK response is a well-known port, and the destination port is randomly chosen. After the three-way handshake, the client responds to the server with a TCP ACK, acknowledging the server’s response.
3: – As far as BGP is concerned, TCP clients and servers are routers. When the “client” router initiates the BGP connection, it sends a request to the server with a destination port 179 and a random X source port. The server then responds with a source port of 179 and a destination port of X. Consequently, all client-to-server traffic uses destination 179, while all server-to-client traffic uses source 179.
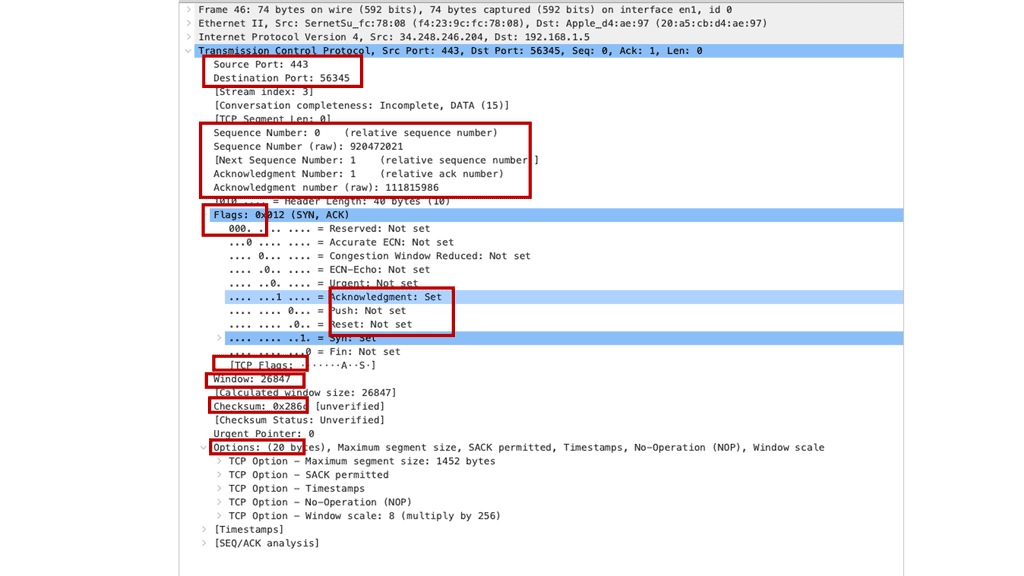
The following Wireshark output shows a sample BGP update message. Notice the Dst Port: 179 highlighted in red.
To achieve reliable delivery, developers could either build a new transport protocol or use an existing one. The BGP creators leveraged TCP’s already robust reliability mechanisms instead of reinventing the wheel. This integration with TCP creates two phases of BGP session establishment:
- TCP connection establishment phase
- BGP session establishment phase
BGP uses a finite state machine (FSM) throughout the two phases of session establishment. In computing, a finite state machine is a construct that allows an object – the machine here – to operate within a fixed number of states. There is a specific purpose and set of operations for each state. The machine exists in only one of these states at any given moment. Input events trigger state changes. BGP’s FSM has six states in total. The following three states of BGP’s FSM pertain to TCP connection establishment:
- Idle
- Connect
- Active
TCP messages are exchanged in these states for reliable delivery of BGP messages. After the TCP connection establishment phase, BGP enters the following three states of the BGP FSM, which pertain to the BGP session establishment phase:
- Opensent
- Openconfirm
- Established
In these states, BGP exchanges messages related to the BGP session. The OPENSENT and OPENCONFIRM states correspond to the exchange of BGP session attributes between the BGP speakers. The ESTABLISHED state indicates the peer is stable and can accept BGP routing updates.
Together, these six states make up the entire BGP FSM. BGP maintains a separate FSM for each intended peer. Upon receiving input events, a peer transitions between these states. When a TCP connection is successfully established in the CONNECT or ACTIVE states, the BGP speaker sends an OPEN message and enters the OPENSENT state. An error event could cause the peer to transition to IDLE in any state.
TCP Connection Establishment Phase
Successful TCP connections are required before negotiating a BGP session between two peers. Over TCP, BGP-related messages can be exchanged reliably between two peers. A broken TCP connection also breaks the BGP session. BGP sessions are not permanently established after successful TCP connections.
Because BGP operates independently within a TCP connection, it “rides” on top of TCP. Peering attempts can fail when two peers agree on TCP parameters but disagree on BGP parameters. While establishing the TCP connection, the BGP FSM oscillates between IDLE, ACTIVE, and CONNECT states.
TCP is a connection-oriented protocol. This means TCP establishes a connection between two speakers, ensuring the information is ordered and delivered reliably. To create this connection, TCP uses servers and clients.
- Clients connect to servers, making them the connecting side
- Servers listen for incoming connections from prospective clients
TCP uses port numbers to identify the services and applications a server hosts. HTTP traffic uses TCP port 80, one of the most well-known. Clients initiate connections to these ports to access a specific service from a TCP server. Randomly generated TCP port numbers will be used by TCP clients to source their messages.
Whenever a TCP connection is made, a passive side waits for a connection, and an active side tries to make the connection. The following two methods can be used to open or establish TCP connections:
- Passive Open
- Active Open
A passive open occurs when a TCP server accepts a TCP client’s connection attempts on a specific TCP port. A WebServer, for instance, is configured to accept connections on TCP port 80, also referred to as “listening” on TCP port 80.
Active open occurs when a TCP client attempts to connect to a specific port on a TCP server. In this case, Client A can initiate a connection request to connect to the Web Server’s TCP Port 80.
To establish and manage a TCP connection, clients and servers exchange TCP control messages. Messages sent in TCP/IP packets are characterized by control bits in the TCP header. As shown in the Wireshark capture below, the SYN and ACK bits in the TCP header of the TCP/IP packet play a crucial role in the basic setup of the TCP connection.
Source: PacketPushers
The SYN bit indicates an attempt to establish a connection. To ensure reliable communication, it synchronizes TCP sequence numbers. An ACK bit suggests that a TCP message has been acknowledged. Reliability is based on the requirement that messages be acknowledged.
TCP connections are generally established by exchanging three control messages:
- The client initiates an active open by sending a TCP/IP packet with the SYN bit set in the TCP header. This is a SYN message.
- The server responds with its SYN message (the SYN bit is set in the TCP header), resulting in a passive open. The server also acknowledges the client’s SYN segment by indicating the ACK bit in the same control message. Since both SYN and ACK bits are set in the same message, this message is called the SYN-ACK message.
- The Client responds with a TCP/IP packet, with the ACK bit set in the TCP header, to acknowledge that it received the Server’s SYN segment.
A TCP three-way handshake involves exchanging control messages or segments. Once the handshake is completed, a TCP connection has been established, and data can be exchanged between the devices.
BGP’s three-way handshake is performed as follows:
- BGP speakers register the BGP process on TCP port 179 and listen for connection attempts from configured clients.
- As the TCP client, one speaker performs an active open by sending a SYN packet destined to the remote speaker’s TCP port 179. The packet is sourced from a random port number.
- The remote speaker, acting as a TCP server, performs a passive open by accepting the SYN packet from the TCP client on TCP port 179 and responding with its own SYN-ACK packet.
- The client speaker responds with an ACK packet, acknowledging it received the server’s SYN packet.
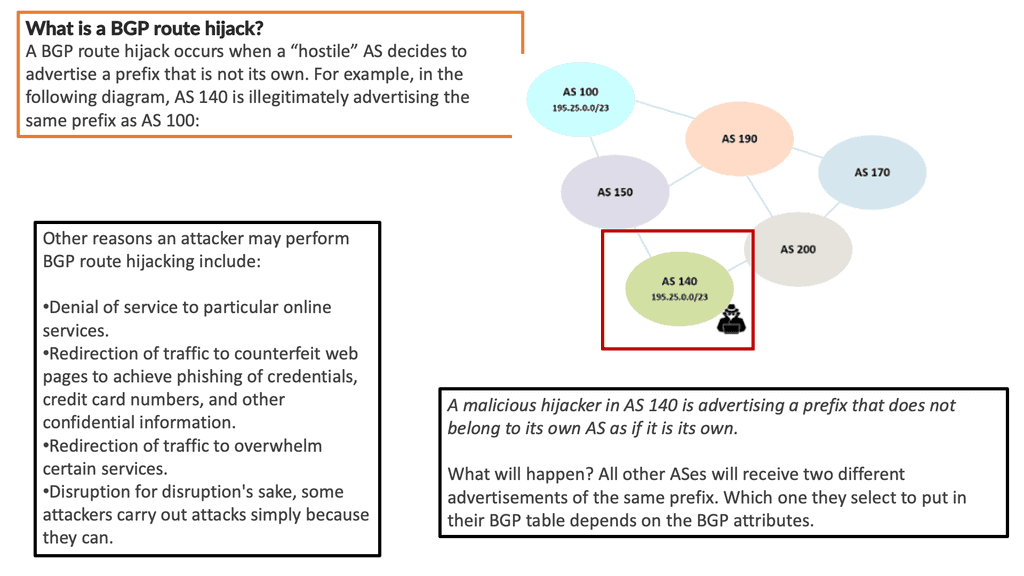
Bonus Content: What Is BGP Hijacking?
A BGP hijack occurs when attackers maliciously reroute Internet traffic. The attacker accomplishes this by falsely announcing ownership of IP prefixes they do not control, own, or route. When a BGP hijack occurs, all the signs on a stretch of the freeway are changed, and traffic is redirected to the wrong exit.
The BGP protocol assumes that interconnected networks are telling the truth about which IP addresses they own, so BGP hijacking is nearly impossible to stop. Imagine if no one watched the freeway signs. The only way to tell if they had been maliciously changed was by observing that many cars ended up in the wrong neighborhoods. To hijack BGP, an attacker must control or compromise a BGP-enabled router that bridges two autonomous systems (AS), so not just anyone can do so.
Inject False Routing Information
BGP hijacking can occur when an attacker gains control over a BGP router and announces false routing information to neighboring routers. This misinformation causes the routers to redirect traffic to the attacker’s network instead of the intended destination. The attacker can then intercept, monitor, or manipulate the traffic for malicious purposes, such as eavesdropping, data theft, or launching distributed denial of service (DDoS) attacks.
Methods for BGP Hijacking
There are several methods that attackers can use to carry out BGP hijacking. One common technique is prefix hijacking, where the attacker announces a more specific IP address prefix for a given destination than the legitimate owner of that prefix. This causes traffic to be routed through the attacker’s network instead of the legitimate network.
Another method is AS path manipulation, where the attacker modifies the AS path attribute of BGP updates to make their route more appealing to neighboring routers. By doing so, the attacker can attract traffic to their network and then manipulate it as desired.
Mitigate BGP Hijacking
Network operators can implement various security measures to mitigate the risk of BGP hijacking. One crucial step is validating BGP route announcements using Route Origin Validation (ROV) and Resource Public Key Infrastructure (RPKI). These mechanisms allow networks to verify the legitimacy of BGP updates and reject any malicious or unauthorized announcements.
Additionally, network operators should establish BGP peering relationships with trusted entities and implement secure access controls for their routers. Regular monitoring and analysis of BGP routing tables can also help detect and mitigate hijacking attempts in real-time.
BGP Exploit and Port 179
Exploiting Port 179
Port 179 is the designated port for BGP communication. Cybercriminals can exploit this port to manipulate BGP routing tables, redirecting traffic to unauthorized destinations. Attackers can potentially intercept and use sensitive data by impersonating a trusted BGP peer or injecting false routing information.
The consequences of a successful BGP exploit can be severe. Unauthorized rerouting of internet traffic can lead to data breaches, service disruptions, and even financial losses. The exploit can be particularly damaging for organizations that rely heavily on network connectivity, such as financial institutions and government agencies.
Protecting your network from BGP exploits requires a multi-layered approach. Here are some essential measures to consider:
1. Implement BGP Security Best Practices: Ensure your BGP routers are correctly configured and follow best practices, such as filtering and validating BGP updates.
2. BGP Monitoring and Alerting: Deploy robust monitoring tools to detect anomalies and suspicious activities in BGP routing. Real-time alerts can help you respond swiftly to potential threats.
3. Peer Authentication and Route Validation: Establish secure peering relationships and implement mechanisms to authenticate BGP peers. Additionally, consider implementing Resource Public Key Infrastructure (RPKI) to validate the legitimacy of BGP routes.
BGP Port 179 Exploit
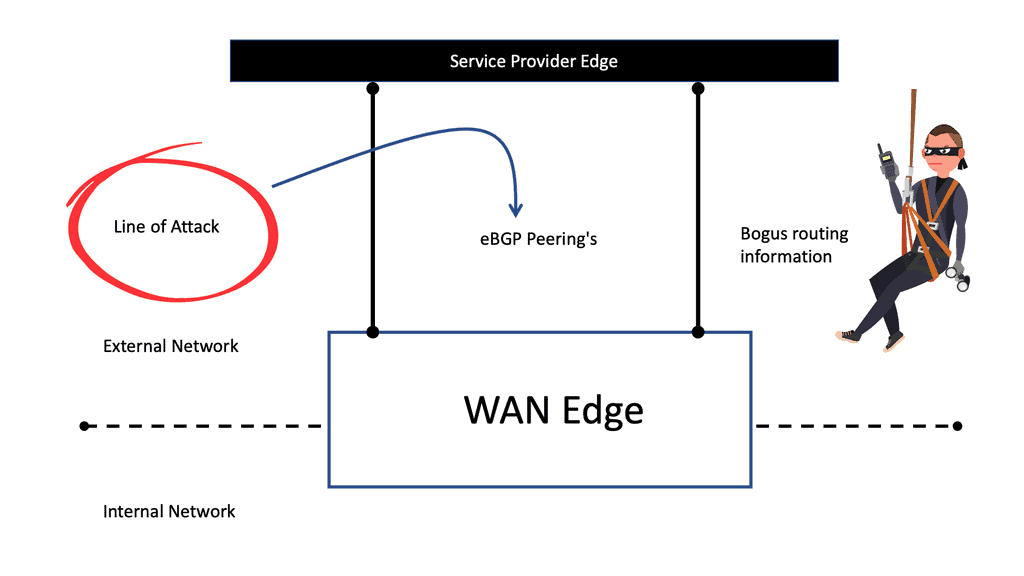
What is the BGP protocol in networking? The operation of the Internet Edge and BGP is crucial to ensure that Internet services are available. Unfortunately, this zone is a public-facing infrastructure exposed to various threats, such as denial-of-service, spyware, network intrusion, web-based phishing, and application-layer attacks. BGP is highly vulnerable to multiple security breaches due to the lack of a scalable means of verifying the authenticity and authorization of BGP control traffic.
As a result, a bad actor could compromise BGP and inject believable BGP messages into the communication between BGP peers. As a result, they were injecting bogus routing information or breaking the peer-to-peer connection.
In addition, outsider sources can also disrupt communications between BGP peers by breaking their TCP connection with spoofed RST packets. To do this, you need to undergo BGP vulnerability testing. One option is to use the port 179 BGP exploit to collect data on the security posture of BGP implementations.
Metasploit: A Powerful Penetration Testing Tool:
Metasploit, developed by Rapid7, is an open-source penetration testing framework that provides a comprehensive set of tools for testing and exploiting vulnerabilities. One of its modules focuses specifically on BGP port 179, enabling ethical hackers and security professionals to assess the security posture of their networks.
Exploiting BGP with Metasploit:
Metasploit offers a wide range of BGP-related modules that can be leveraged to simulate attacks and identify potential vulnerabilities. These modules enable users to perform tasks such as BGP session hijacking, route injection, route manipulation, and more. By utilizing Metasploit’s BGP modules, network administrators can proactively identify weaknesses in their network infrastructure and implement appropriate mitigation strategies.
Benefits of Metasploit BGP Module:
The utilization of Metasploit’s BGP module brings several benefits to network penetration testing:
- Comprehensive Testing: Metasploit’s BGP module allows for thorough testing of BGP implementations, helping organizations identify and address potential security flaws.
- Real-World Simulation: By simulating real-world attacks, Metasploit enables security professionals to gain deeper insights into the impact of BGP vulnerabilities on their network infrastructure.
- Enhanced Risk Mitigation: Using Metasploit to identify and understand BGP vulnerabilities helps organizations develop effective risk mitigation strategies, ensuring the integrity and availability of their networks.
Border Gateway Protocol Design
**Service Provider ( SP ) Edge Block**
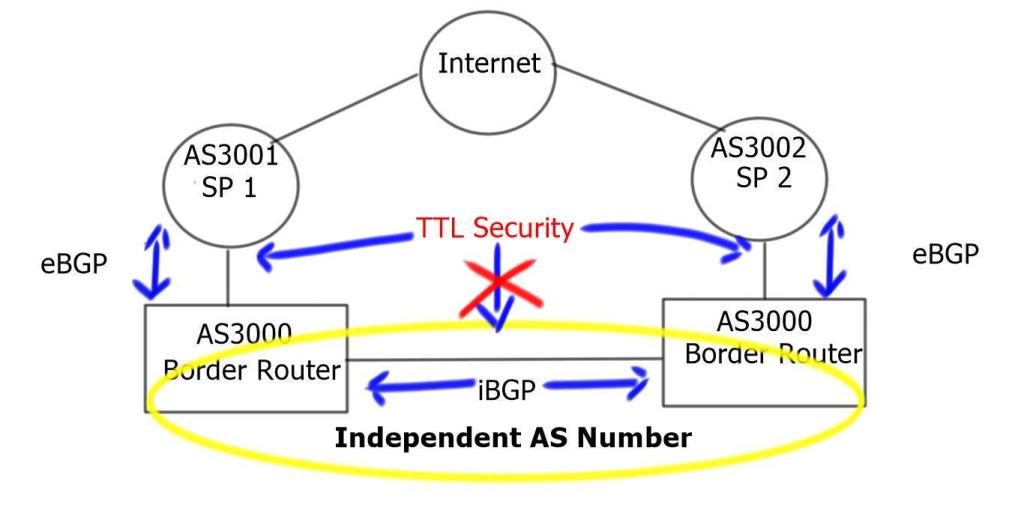
Service Provider ( SP ) Edge comprises Internet-facing border routers. These routers are the first line of defense and will run external Border Gateway Protocol ( eBGP ) to the Internet through dual Internet Service Providers ( ISP ).
Border Gateway Protocol is a policy-based routing protocol deployed at the edges of networks connecting to 3rd-party networks and has redundancy and highly available methods such as BGP Multipath. However, as it faces the outside world, it must be secured and hardened to overcome numerous blind and semi-blind attacks it can face, such as DoS or Man-in-the-Middle Attacks.
**Man-in-the-middle attacks**
Possible attacks against BGP could be BGP route injection from a bidirectional man-in-the-middle attack. In theory, BGP route injection seems simple if one compares it to a standard ARP spoofing man-in-the-middle attack, but in practice, it does not. To successfully insert a “neighbor between neighbors,” a rogue router must successfully TCP hijack BGP.
Requires the following:
- Correctly matching the source address and source port.
- Matching the destination port.
- Guess the TTL if a BGP TTL hacks if applied.
- Match the TCP sequence numbers.
- Bypassing MD5 authentication ( if any ).
Although this might seem like a long list, it is possible. The first step would be to ARP Spoof the connection between BGP peers using Dsniff or Ettercap. After successfully spoofing the session, launch tools from CIAG BGP, such as TCP hijack. The payload is a BGP Update or a BGP Notification packet fed into the targeted session.
**Blind DoS attacks against BGP routers**
A DoS attack on a BGP peer would devastate the overall network, more noticeably for exit traffic, as BGP deployment occurs at the network’s edges. On the other hand, a DoS attack could bring down a BGP peer and cause route flapping or dampening. A widespread DoS attack floods the target BGP service, enabling MD5 authentication using SYN TCP packets with MD5 signatures. The attack overloads the targeted peer with loads of MD5 authentication processing, which consumes all its resources that should process standard control and data plane function packets.
**Countermeasures – Protecting the Edge**
One way to lock down BGP is to implement the “BGP TTL hack,” known as the BGP TTL security check. This feature protects eBGP sessions ( not iBGP ) and compares the value in the received IP packet’s Time-to-Live ( TTL ) field with a hop count locally configured on each eBGP neighbor. All packets with values less than the expected value are silently discarded.
One security concern with BGP is the possibility of a malicious attacker injecting false routing information into the network. To mitigate this risk, a TTL (Time to Live) security check can be implemented.
TTL Security Check
The TTL security check involves verifying the TTL value of a BGP update message. The TTL value is a field in the IP header specifying the maximum number of hops a packet can travel before being discarded. When a BGP update message is received, the TTL value is checked to ensure that the message has traveled fewer hops than expected. If the TTL value is higher than expected, the message is discarded.
Implementing a TTL security check can help prevent attacks such as route hijacking and route leaks. Route hijacking is an attack where a malicious actor announces false routing information to redirect traffic to a different destination. Route leaks occur when a network announces routes that it does not control, leading to potential traffic congestion and instability.
Importance of BGP TTL Security Check:
1. Mitigating Route Leaks: Route leaks occur when BGP routers inadvertently advertise routes to unauthorized peers. By implementing TTL security checks, routers can verify the authenticity of received BGP packets, preventing unauthorized route advertisements and mitigating the risk of route leaks.
2. Preventing IP Spoofing: TTL security check is crucial in preventing IP spoofing attacks. By verifying the TTL value of incoming BGP packets, routers can ensure that the source IP address is legitimate and not spoofed. This helps maintain the trustworthiness of routing information and prevents potential network attacks.
3. Enhancing BGP Routing Security: BGP TTL security check adds an extra layer of security to BGP routing. By validating the TTL values of incoming packets, network operators can detect and discard packets with invalid TTL values, thus preventing potential attacks that manipulate TTL values.
Implementation of BGP TTL Security Check:
To implement BGP TTL security checks, network operators can configure BGP routers to verify the TTL values of received BGP packets. This can be done by setting a minimum TTL threshold, which determines the minimum acceptable TTL value for incoming BGP packets. Routers can then drop packets with TTL values below the configured threshold, ensuring that only valid packets are processed.
It is possible to forge the TTL field in the IP packet header. To forge accurately, the TTL count of matching the TTL count of the configured neighbor is nearly impossible. The trusted peer would most likely be compromised for this to take place. After you enable the check, the configured BGP peers send all their updates with a TTL of 255. This router only accepts BGP packets with a TTL value of 252 or more significant in the command syntax below.
| Neighbor 192.168.1.1 TTL-security hops 2 | The external BGP neighbor may be up to 2 hops away. |
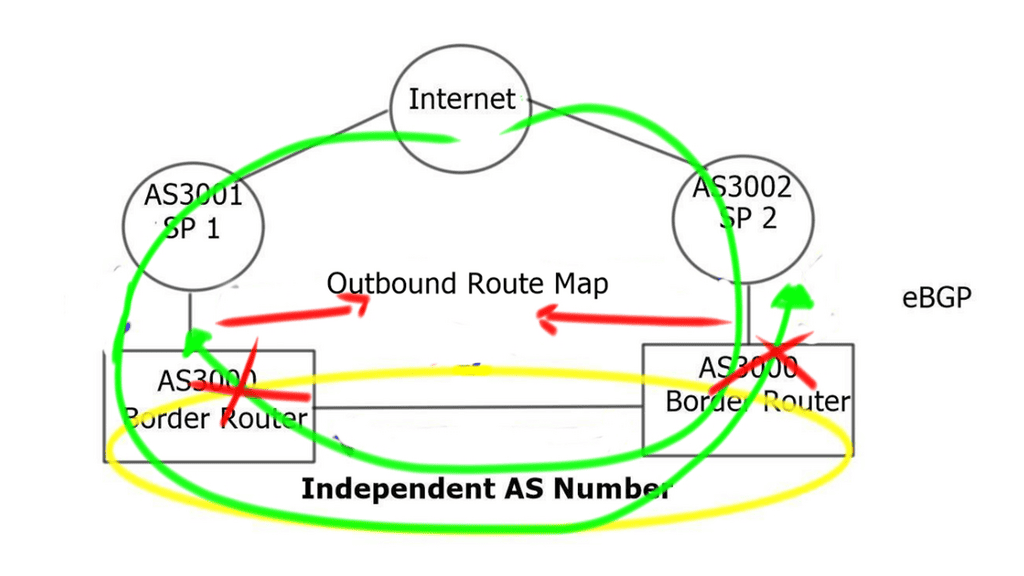
Routers learned from SP 1 should not be leaked to SP 2 and vice versa. The following should be matched and applied to an outbound route map.
| ip as-path access-list 10 permit ^$ | Permit only if there is no as-path prepend |
| ip as-path access-list 10 deny .* | Deny if there is an as-path prepend |
A final note on BGP security
|
BGP is one of the protocols that makes the Internet work. Most hackers and attackers worldwide target BGP due to its criticality and importance to the Internet. Attackers are primarily interested in finding vulnerabilities in systems like BGP and exploiting them. If they are successful, they can cause significant disruption to the Internet by finding a loophole in BGP. This is the primary reason for securing a BGP.
Before securing BGP, there are a few primary areas to focus on:
- Authentication: BGP neighbors in the same AS or two different ASs must be authenticated. BGP sessions and routing information should be shared only with authenticated BGP neighbors.
- Message integrity: BGP messages should not be illegally modified during transport.
- Availability: BGP speakers should be protected from Denial-of-Service (DoS) or Distributed Denial-of-Service (DDoS) attacks.
- Prefix origination validation: Implementing a mechanism to distinguish between invalid and legitimate routes for BGP destinations is necessary.
- AS path verification: Verify that no illegal entity falsifies an AS_PATH (modifies it with a wrong AS number or deletes it). This can result in traffic black holes for the destination prefix as the route selection process uses AS_PATH.
A Final Note on BGP Security
BGP (Border Gateway Protocol) is a protocol used to exchange routing information between different Autonomous Systems (AS) on the Internet. The Internet must function correctly, but it introduces various security challenges.
BGP Hijacking
One of the most significant security challenges with BGP is the possibility of BGP hijacking. BGP hijacking occurs when an attacker announces illegitimate routes to a BGP speaker, causing traffic to be diverted to the attacker’s network. This can lead to severe consequences, such as loss of confidentiality, integrity, and availability of the affected network.
Various security mechanisms have been proposed to prevent BGP hijacking. One of the most commonly used mechanisms is the Resource Public Key Infrastructure (RPKI). RPKI is a system that enables network operators to verify the legitimacy of BGP advertisements. RPKI associates a public key with a route object in the BGP routing table. If the public key associated with a route object matches the public key of the originating AS, the route is considered legitimate.
BGPsec
Another mechanism to prevent BGP hijacking is the use of BGPsec. BGPsec is a security extension to BGP that provides cryptographic protection to BGP messages. BGPsec ensures that BGP messages are not tampered with during transit and that the origin of the BGP messages can be verified.
In addition to BGP hijacking, BGP is also susceptible to other security threats, such as BGP route leaks and BGP route flaps. Various best practices should be followed to mitigate these threats, such as implementing route filtering, route reflectors, and deploying multiple BGP sessions.
In conclusion, BGP is a critical Internet protocol that introduces various security challenges. To ensure the security and stability of the Internet, network operators must implement appropriate security mechanisms and best practices to prevent BGP hijacking, route leaks, and other security threats.
A Final Note on BGP Port 179
BGP (Border Gateway Protocol) is a crucial component of the internet infrastructure, facilitating the exchange of routing information between different networks. One of the most critical aspects of BGP is its use of well-known port numbers to establish connections and exchange data. Port 179 holds a significant role among these port numbers.
Port 179 is designated explicitly for BGP communication. It serves as the default port for establishing TCP connections between BGP routers. BGP routers utilize this port to exchange routing information and ensure the optimal flow of network traffic.
BGP Sessions
Port 179’s importance in BGP cannot be overstated. It acts as the gateway for BGP sessions to establish connections between routers. BGP routers use this port to communicate and share information about available routes, network prefixes, and other relevant data. This allows routers to make informed decisions about the most efficient path-forwarding traffic.
When a BGP router initiates a connection, it sends a TCP SYN packet to the destination router on port 179. If the destination router is configured to accept BGP connections, it responds with a SYN-ACK packet, establishing a TCP connection. Once the connection is established, BGP routers exchange updates and inform each other about network changes.
Port 179 is typically used for external BGP (eBGP) sessions, where BGP routers from different autonomous systems connect to exchange routing information. However, it can also be used for internal BGP (iBGP) sessions within the same autonomous system.
Port 179 is a well-known port.
It is worth noting that port 179 is a well-known port, meaning it is standardized and widely recognized across networking devices and software. This standardization ensures compatibility and allows BGP routers from different vendors to communicate seamlessly.
While port 179 is the default port for BGP, it is essential to remember that BGP can be configured to use other port numbers if necessary. This flexibility allows network administrators to adapt BGP to their specific requirements, although it is generally recommended to stick with the default port for consistency and ease of configuration.
In conclusion, port 179 enables BGP routers to establish connections and exchange routing information. It is the gateway for BGP sessions, ensuring efficient network traffic flow. Understanding the significance of port 179 is essential for network administrators working with BGP and plays a vital role in maintaining a robust and efficient internet infrastructure.
Note: BGP operation is unaffected by the client/server model except for those who connect to port 179 and those who source from port 179. The client or server can be on either side of the BGP session. In some designs, however, assigning TCP server and client roles to specific devices might be desirable. Such a client/server interaction with BGP can be found in hub-spoke topologies such as DMVPN – DMVPN phases, where the hub is configured as a route-reflector and the spokes are configured as route-reflector clients. BGP dynamic neighbors can be used to ensure that the hub listens and accepts connections from various potential IP addresses, so it becomes a TCP server waiting passively for the spokes to open TCP connections.
Summary: BGP Port 179 Exploit Metasploit
In the vast realm of networking, BGP (Border Gateway Protocol) plays a crucial role in facilitating the exchange of routing information between different autonomous systems. As network administrators and enthusiasts, understanding the significance of BGP Port 179 is essential. In this blog post, we delved into the intricacies of BGP Port 179, exploring its functions, common issues, and best practices.
The Basics of BGP Port 179
BGP Port 179 is the designated port the BGP protocol uses for establishing TCP connections between BGP speakers. It serves as the gateway for communication and exchange of routing information. BGP Port 179 acts as a doorway through which BGP peers connect, allowing them to share network reachability information and determine the best paths for data transmission.
Common Issues and Troubleshooting
Like any networking protocol, BGP may encounter various issues that can disrupt communication through Port 179. One common problem is establishing BGP sessions. Misconfigurations, firewall rules, or network connectivity issues can prevent successful connections. Troubleshooting BGP Port 179 involves analyzing logs, checking routing tables, and verifying BGP configurations to identify and resolve any problems that may arise.
Security Considerations and Best Practices
Given its critical role in routing and network connectivity, securing BGP Port 179 is paramount. Implementing authentication mechanisms like MD5 authentication can prevent unauthorized access and potential attacks. Applying access control lists (ACLs) to filter incoming and outgoing BGP traffic can add an extra layer of protection. Regularly updating BGP software versions and staying informed about security advisories are crucial best practices.
Scaling and Performance Optimization
As networks grow in size and complexity, optimizing BGP Port 179 becomes vital for efficient routing. Techniques such as route reflection and peer groups help reduce the computational load on BGP speakers and improve scalability. Implementing route-dampening mechanisms or utilizing BGP communities can enhance performance and fine-tune routing decisions.
- DMVPN - May 20, 2023
- Computer Networking: Building a Strong Foundation for Success - April 7, 2023
- eBOOK – SASE Capabilities - April 6, 2023