SASE Visibility with Cisco ThousandEyes
In today's interconnected digital landscape, enterprises are increasingly adopting Secure Access Service Edge (SASE) solutions to streamline their network and security infrastructure. One key aspect of SASE implementation is ensuring comprehensive visibility into the network performance and security posture. In this blog post, we will explore how Cisco ThousandEyes can enhance SASE visibility, empowering organizations to optimize their network operations and ensure a secure and seamless user experience.
SASE visibility refers to the ability to monitor and analyze network traffic, performance metrics, and security events across the entire SASE architecture. It involves gaining insights into user experience, application performance, network latency, and security threats. By leveraging Cisco ThousandEyes, organizations can achieve end-to-end visibility, enabling them to proactively identify and address any potential issues that may impact their SASE deployment.
Monitoring User Experience: User experience is a critical aspect of SASE visibility. With Cisco ThousandEyes, organizations can monitor real-time user experience metrics such as application response time, page load time, and transaction success rates. This granular visibility helps IT teams quickly identify and resolve performance bottlenecks, ensuring a seamless user experience regardless of user location or device.
Ensuring Application Performance: Application performance is another crucial component of SASE visibility. Cisco ThousandEyes enables organizations to monitor and analyze application performance across the SASE architecture, including public clouds, data centers, and remote locations. By leveraging comprehensive network measurements and deep packet inspection, IT teams can proactively optimize application delivery, ensuring high performance and availability.
Detecting and Mitigating Security Threats: Security is paramount in any SASE implementation. Cisco ThousandEyes offers robust security monitoring capabilities, allowing organizations to detect and mitigate potential threats in real-time. With advanced threat intelligence and anomaly detection, IT teams can identify and respond to security incidents promptly, safeguarding critical assets and ensuring compliance with industry regulations.
Cisco ThousandEyes plays a pivotal role in enhancing SASE visibility for organizations. By providing comprehensive insights into user experience, application performance, and security threats, Cisco ThousandEyes empowers IT teams to optimize network operations, ensure a seamless user experience, and protect against potential risks. With its advanced monitoring and analysis capabilities, Cisco ThousandEyes is a valuable tool in the SASE journey, enabling organizations to achieve greater visibility, security, and performance.Matt Conran
Highlights: SASE Visibility with Cisco ThousandEyes
Understanding SASE Visibility
SASE visibility refers to gaining deep insights and real-time analytics into network traffic, security events, and user behavior across the entire network infrastructure. By leveraging advanced technologies such as AI and machine learning, SASE visibility gives organizations a comprehensive view of their network, enabling proactive threat detection, incident response, and policy enforcement.
### The Importance of Visibility in SASE
Visibility is the backbone of any effective SASE architecture. Without it, organizations are essentially navigating the digital world blindfolded. Visibility within SASE encompasses the ability to monitor traffic, detect anomalies, and enforce policies in real-time. This capability is crucial for identifying potential threats, ensuring compliance, and optimizing network performance. By having a clear line of sight into every activity within the network, businesses can proactively address vulnerabilities before they become detrimental.
### Implementing SASE Visibility in Your Organization
Implementing SASE visibility requires a strategic approach. Start by assessing your current network architecture and identifying areas that could benefit from enhanced visibility. Invest in solutions that offer comprehensive monitoring and analytics capabilities.
Training your IT staff to interpret data insights effectively is also crucial in maximizing the benefits of SASE visibility. Collaboration with trusted vendors can further streamline the integration process, ensuring a smooth transition to a more secure and efficient network environment.
SASE visibility comprises several vital components that work in synergy to deliver comprehensive insights:
1. Network Traffic Monitoring: SASE visibility empowers organizations to monitor network traffic at a granular level, identifying potential security gaps, abnormal behavior, and bandwidth bottlenecks. This enables timely remediation and ensures a seamless user experience.
2. Application Visibility: With SASE, organizations gain unparalleled application usage and performance visibility. This allows for practical application control, optimization, and prioritization, ensuring critical business applications receive the necessary resources and identifying potential security risks.
3. User Behavior Analytics: SASE visibility goes beyond traditional user monitoring, employing advanced analytics to detect and respond to suspicious user behavior. Organizations can swiftly identify anomalies and mitigate potential threats by establishing baseline behavior patterns.
SASE Visibility with Cisco ThousandEyes
Visibility forms the foundation of effective network management, security, and troubleshooting. In the context of SASE, visibility refers to the ability to monitor and gain insights into network traffic, application performance, security threats, and user experience. Due to SASE’s distributed and dynamic nature, traditional monitoring tools fail to provide visibility. This is where Cisco ThousandEyes steps in.
**Network Intelligence Platform**
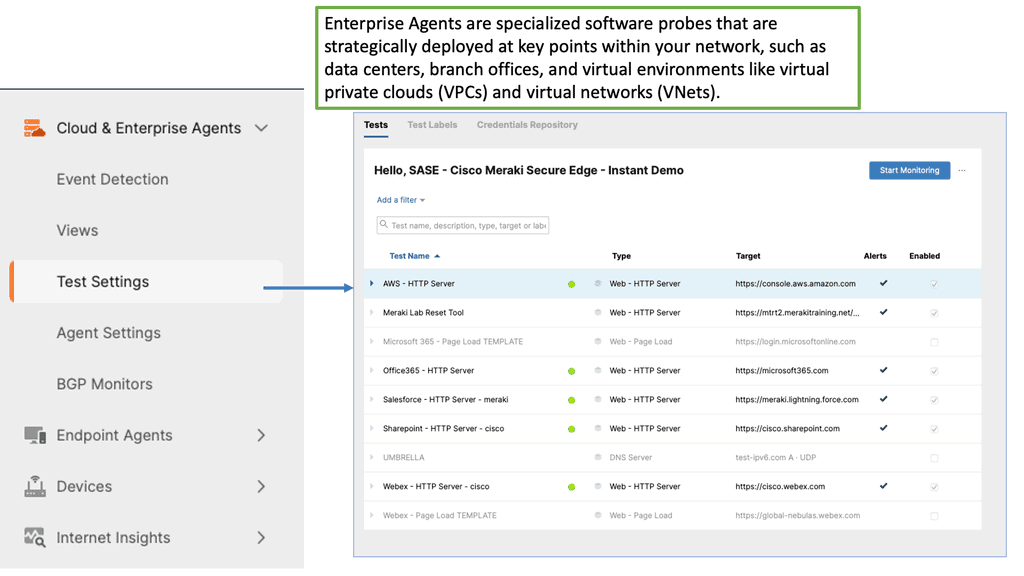
Cisco ThousandEyes is a comprehensive network intelligence platform that empowers organizations with end-to-end visibility across their SASE infrastructure. It combines network monitoring, application performance monitoring, and security capabilities to deliver a holistic view of the network ecosystem. By leveraging active and passive monitoring techniques, ThousandEyes enables organizations to proactively identify and resolve issues, ensure optimal application performance, and strengthen security posture.
A. Network Monitoring: Cisco ThousandEyes provides real-time visibility into network paths, latency, and packet loss, helping organizations identify bottlenecks and optimize traffic routing. With its global network of monitoring agents, it offers insights into network performance from various locations, ensuring a comprehensive view.
B. Application Performance Monitoring: Ensuring optimal application performance is critical in a SASE environment. ThousandEyes monitors application performance metrics, such as response time, throughput, and availability, enabling organizations to identify and troubleshoot performance issues.
C. Security Monitoring: Cisco ThousandEyes helps organizations monitor security threats within their SASE architecture. It leverages deep packet inspection and threat intelligence to detect and mitigate potential security risks. By providing visibility into traffic patterns and anomalies, ThousandEyes strengthens security posture and enhances incident response capabilities.
Network & Application Visibility Technologies:
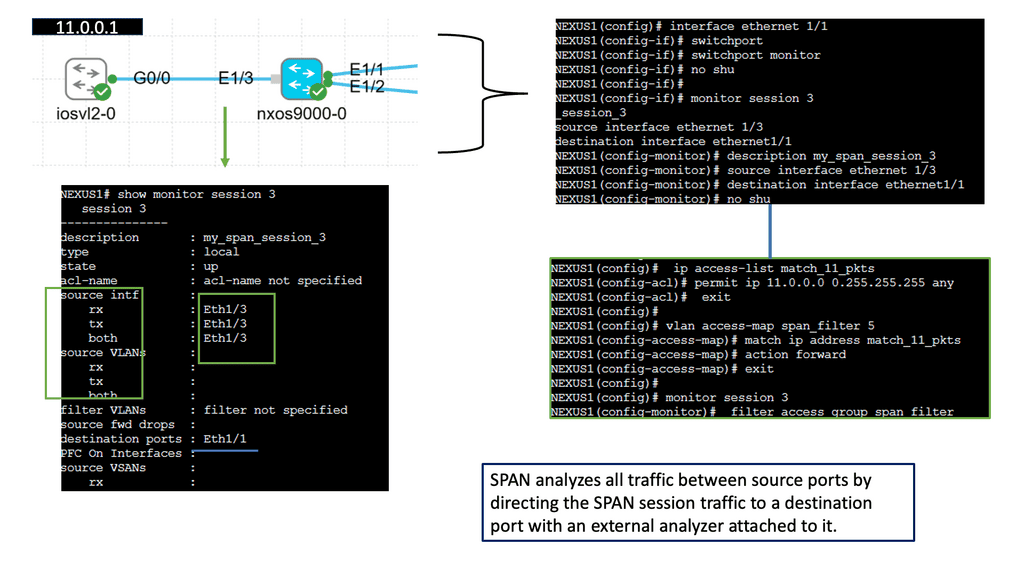
**Understanding SPAN**
SPAN, also known as port mirroring, is a feature that enables the monitoring of network traffic on a switch. It replicates packets from one or more source ports to a destination port, where a network analyzer or monitoring tool can capture and analyze the traffic. By implementing SPAN, network administrators gain valuable insights into network behavior, troubleshoot issues, and ensure network security.
**SPAN Configuration**
Configuring SPAN on Cisco NX-OS is straightforward. Administrators can define the source ports from which traffic will be mirrored and specify the destination port where the mirrored traffic will be sent. Additionally, Cisco NX-OS provides flexible options to configure SPAN filters, allowing administrators to selectively mirror specific types of traffic based on various criteria, such as VLANs, protocols, or IP addresses.
**Key SPAN Benefits**
The benefits of utilizing SPAN on Cisco NX-OS are vast. Firstly, it enables network administrators to conduct in-depth network traffic analysis, helping them identify potential bottlenecks, anomalies, or security threats. This visibility is essential for optimizing network performance and maintaining a secure environment. Secondly, SPAN allows seamless integration with third-party monitoring tools, providing network administrators a wide range of options for analyzing captured traffic. Lastly, SPAN on Cisco NX-OS is highly scalable, supporting the monitoring of multiple source ports and accommodating the evolving needs of network infrastructures.
Understanding sFlow
sFlow is a sampling technology that enables network devices to collect and analyze traffic data. By sampling packets regularly, sFlow provides a representative view of the overall network traffic, allowing administrators to identify and address potential issues efficiently. It offers a scalable and non-intrusive approach to network monitoring.
sFlow provides valuable insights into network performance metrics, such as bandwidth utilization, top talkers, and application-level statistics. Network administrators can proactively identify and address potential bottlenecks by analyzing these metrics, ensuring optimal network performance. The real-time nature of sFlow allows for quick troubleshooting and capacity planning, ultimately improving the overall user experience.
ThousandEyes & SASE: A Proactive Approach
Combining Cisco ThousandEyes with your SASE VPN gives you end-to-end visibility into the SASE security stacks and all network paths, including nodes. These can be consumed from Cisco ThousandEyes, enabling a proactive approach to monitoring your SASE solution, a bundle of components. Cisco ThousandEyes has several agent deployment models that you can use depending on whether you want visibility into remote workers or users at the branch site or even agent-to-agent testing.
Remember that ThousandEyes is not just for a Cisco SASE solution; it has multiple monitoring use cases, of which Cisco Umbrella SASE is just one. ThousandEyes also has good integrations with Cisco AppDynamics for full-stack end-to-end observability. First, let’s do a quick recap on the SASE definition.
Example Product: Cisco ThousandEyes
### What is Cisco ThousandEyes?
Cisco ThousandEyes is a cloud-based network intelligence platform that offers deep insights into network performance from multiple vantage points, including local networks, cloud environments, and even end-user devices. By leveraging a combination of synthetic and real-user monitoring techniques, ThousandEyes helps organizations identify and resolve performance issues before they impact users. This comprehensive visibility allows IT teams to pinpoint the root cause of problems swiftly, reducing downtime and improving overall user experience.
### Key Features of Cisco ThousandEyes
Cisco ThousandEyes boasts a plethora of features designed to empower IT teams with actionable intelligence. Some of the standout features include:
1. **End-to-End Visibility**: Gain insights into every hop between your users and the applications they rely on, whether they are hosted on-premises or in the cloud.
2. **Synthetic Monitoring**: Simulate user interactions to proactively detect performance issues across different regions and ISPs.
3. **Real-User Monitoring**: Capture real-time data from actual user sessions to understand how network performance impacts user experience.
4. **Network Path Visualization**: Visualize the entire network path to identify bottlenecks and pinpoint where performance degradation occurs.
5. **Alerts and Notifications**: Set customizable alerts to stay informed about network anomalies and performance thresholds in real-time.
### Benefits of Using Cisco ThousandEyes
Implementing Cisco ThousandEyes can yield numerous benefits for organizations, including:
1. **Improved Troubleshooting**: With detailed network path visualization and comprehensive performance data, IT teams can troubleshoot issues more effectively and efficiently.
2. **Enhanced User Experience**: By proactively monitoring and addressing performance issues, organizations can ensure a smoother and more reliable user experience.
3. **Increased Visibility**: Gain unparalleled insights into both internal and external networks, helping to identify and mitigate risks before they impact operations.
4. **Optimized Resource Allocation**: Leverage performance data to make informed decisions about network infrastructure investments and optimizations.
### Practical Applications of Cisco ThousandEyes
Cisco ThousandEyes can be utilized in a variety of scenarios to enhance network performance and reliability:
1. **Cloud Migrations**: Monitor and troubleshoot performance issues during cloud migration projects to ensure a seamless transition.
2. **SaaS Performance Monitoring**: Keep tabs on the performance of critical SaaS applications to ensure they meet user expectations.
3. **Remote Workforce Support**: Provide remote employees with reliable access to corporate resources by monitoring and optimizing network performance from their locations.
4. **ISP Performance Comparison**: Compare the performance of different ISPs to make informed decisions about service providers and optimize connectivity.
Challenges to the Cisco SASE Solution
The Internet is unstable
The first issue is that the Internet is fragile. We have around 14,000 BGP routing incidents per year. This includes a range of outages and attacks on the BGP protocol and peering relationships: Port 179. Border Gateway Protocol (BGP) is the glue of the Internet backbone, so attacks and outages can ripple effects across different Autonomous Systems (AS). So, if BGP is not stable, which it is not, it can cause problems.
Cloud connectivity based on the Internet will not be stable. Internet cloud providers need more stability regarding network performance on the Internet. These providers rely on the public Internet instead of using a private backbone to carry traffic.
**A: Internet Blindspots**
When moving to a SASE environment, we face several challenges. Internet blindspots can be an Achilles’ heel to SASE deployments and performance. After all, network paths today consist of many more hops over longer and more complex segments (e.g., Internet, security, and cloud providers) that may be entirely out of IT’s control.
Legacy network monitoring tools are no longer suitable for this Internet-centric environment because they primarily collect passive data from on-premises infrastructure. We also have a lot of complexity and moving parts. Modern applications have become increasingly complex, involving modular architectures distributed across multi-cloud platforms. Not to mention a complex web of interconnected API calls and third-party services.
As a result, understanding the application experience for an increasingly remote and distributed workforce is challenging—and siloed monitoring tools fail to provide a complete picture of the end-to-end experience.
**B: Out of your control**
Now that workers are everywhere and cloud-based applications are abundant, the Internet is the new enterprise network. The perimeter has moved to the edges, with most devices and components out of their control. This has many consequences. So, how do enterprises ensure a digital experience when they no longer own the underlying transport, services, and applications their business relies on?
With these new complex and dynamic deployment models, we now have significant blind spots. Network paths are now much longer than they were in the past. Nothing is just one or two hops away. If you do a traceroute from your SASE VPN client, it may seem like one hop, but it’s much more.
**C: Multiple Segments & Components**
We have a lot of complexity with numerous segments and different types of components, such as the Internet, security providers such as Zscaler, and cloud providers. All of this is out of your control. If I were to put my finger in the air, on average, 80% could be out of my control. So, it would help if you paid immediate attention to some things, such as visibility into the underlay, applications, and service dependencies.
Useful Network Troubleshooting
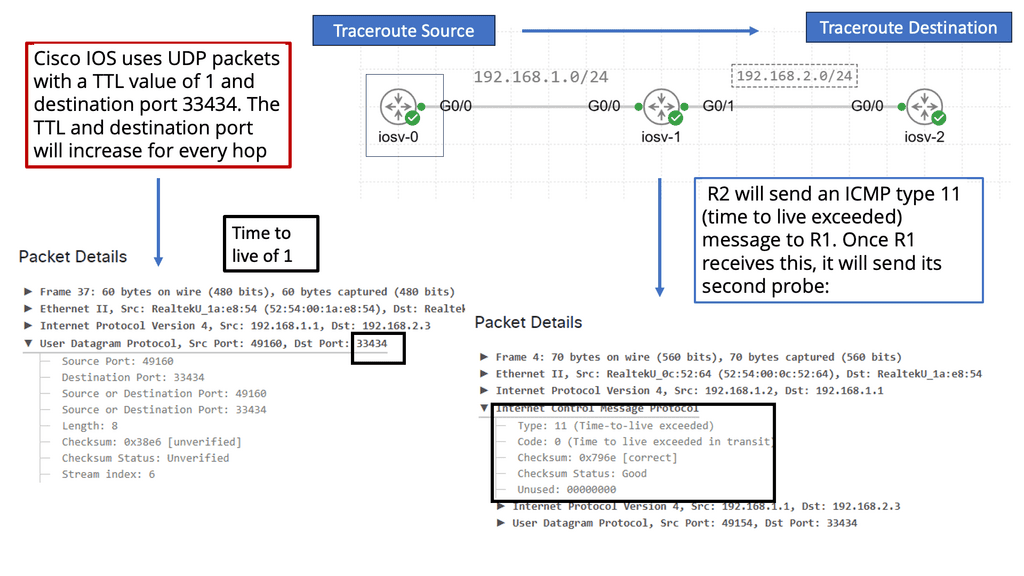
What is Traceroute?
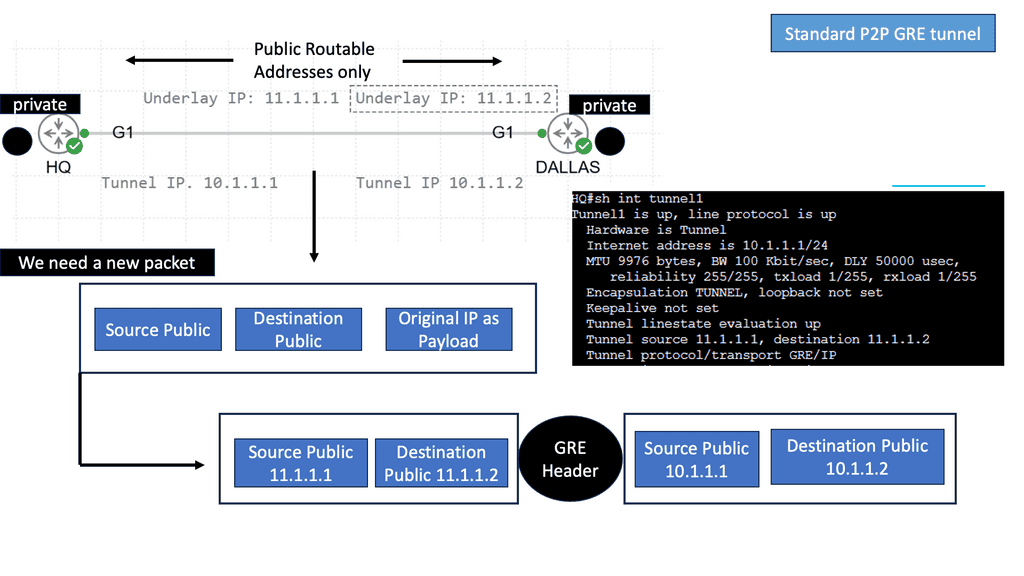
A traceroute is a command-line tool that traces the path data packets take from one point to another on the Internet. It provides valuable information about network hops, latency, and data routing. The traceroute maps the route by sending packets with increasing Time-To-Live (TTL) values, revealing each intermediate node.
When executing the traceroute command, a detailed output is generated. Each line represents a hop, displaying the IP address, domain name (if available), and round-trip time (RTT) for that specific hop. The RTT indicates the time a packet travels from the source to that particular hop and back. Analyzing this output can unveil valuable insights into network performance and potential bottlenecks.
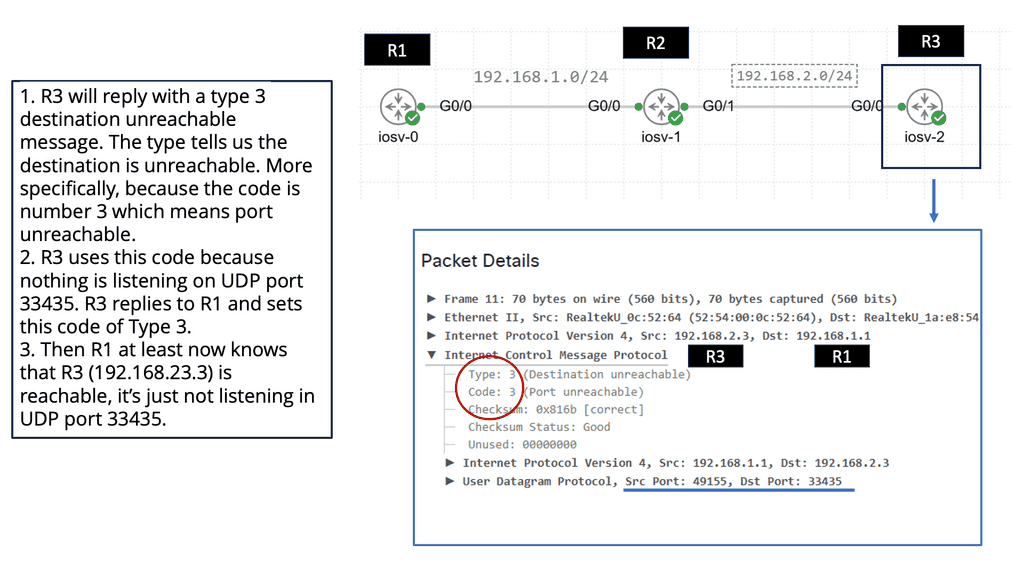
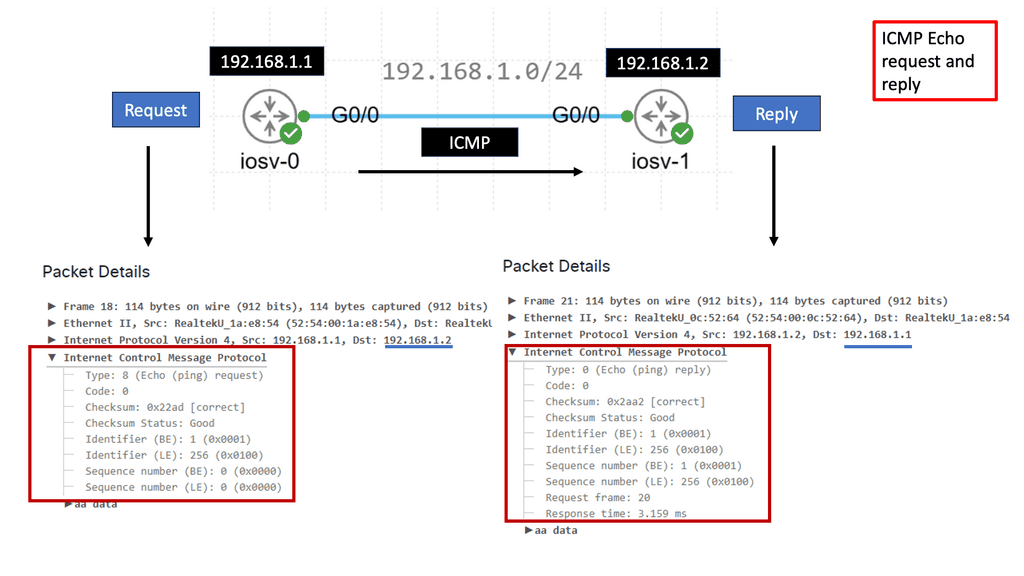
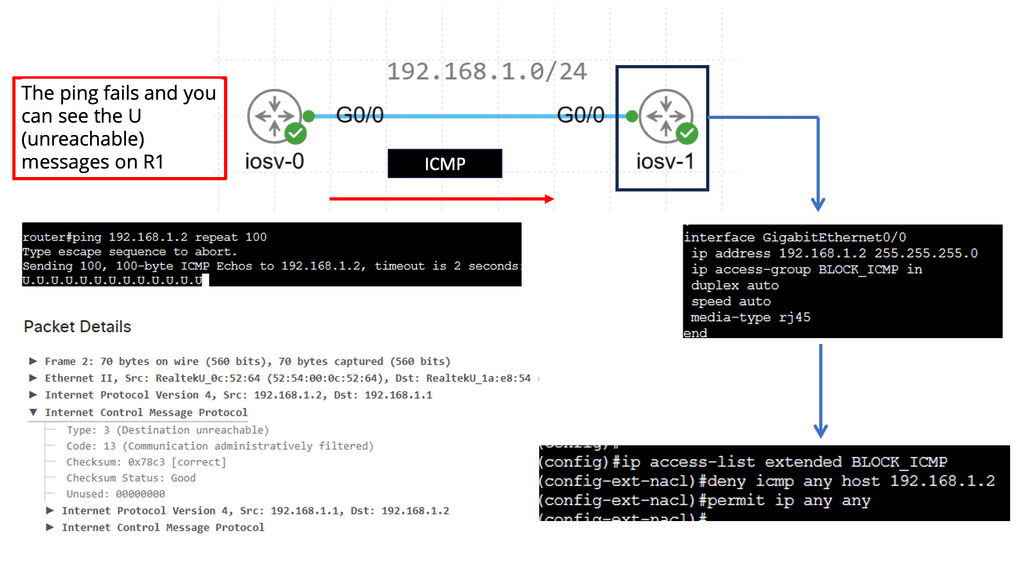
Understanding ICMP Basics
ICMP, often called the “heartbeat of the Internet,” is an integral part of the Internet protocol suite. It operates at the network layer and facilitates essential functions, including error reporting, network diagnostics, and congestion control. By exchanging control messages between routers and hosts, ICMP plays a crucial role in maintaining the smooth flow of data packets across the network.
Echo Request & Echo Reply
ICMP messages come in various forms, each serving a specific purpose. From Echo Request and Echo Reply messages, commonly associated with the ubiquitous Ping utility, to Destination Unreachable and Time Exceeded messages, ICMP provides valuable feedback on network issues and packet status. We will explore the different ICMP message types and their significance in troubleshooting network problems and ensuring efficient communication.
Related: Before you proceed, you may find the following posts helpful:
Integration with Cisco ThousandEyes
ThousandEyes & SASE Integration
Cisco ThousandEyes, a leading network intelligence platform, seamlessly integrates with SASE visibility, amplifying its capabilities. With this integration, organizations can leverage ThousandEyes’ comprehensive network monitoring and troubleshooting capabilities, combined with SASE visibility’s holistic approach.
This collaboration empowers organizations to identify network issues, optimize performance, and ensure a secure and seamless user experience. Cisco Umbrella SASE provides recursive DNS services and helps organizations securely embrace direct internet access (DIA). When applications are hosted in the cloud, we don’t need to backhaul all traffic to the enterprise data center; there will still be applications hosted in the data center; we can use SD-WAN.
Cisco Umbrella started with DNS security solutions and then expanded to include the following features, all delivered from a single cloud security service: DNS-layer security and interactive threat intelligence, a secure web gateway, firewall, cloud access security broker (CASB) functionality, and integration with Cisco SD-WAN.
The Way Forward: SASE VPN End-to-End
–Network Underlay Visibility
Firstly, you need to gain visibility into the network underlay. If you do a traceroute, you may see only one hop. Still, it would help if you had insights into every Layer 3 hop across the network underlay, including Layer 2 or firewalling and load-balancing services in the path.
–Monitoring Metrics
Secondly, you also need to monitor business-critical applications efficiently and thoroughly understand how users are experiencing an application with full-page loads, metrics that matter most to them, and multistep transactions beyond an application’s front door. This will include login availability along with the entire application workflow.
–Understanding Dependancies
Gaining actionable visibility into service dependencies would help. This will enable you to detect, for example, any service disruptions in ISP networks and DNS providers and see how they impact application availability, response times, and page load performance.
–DNS Server Performance
However, we have a hierarchy of servers involved in the DNS process to support the number of steps in the DNS process. For example, some of these steps would include requesting website information, contacting the recursive DNS servers, querying the authoritative DNS servers, Accessing the DNS record, etc.
We must consider the performance of your network’s DNS servers, resolvers, and records. And this can include various vendors across the DNS hierarchy.
Gaining Control & WAN Visibility
You lose control and visibility when WAN connectivity and business-critical applications migrate to shared infrastructure, the Internet, and public cloud locations. One way to regain visibility and control is with Cisco ThousandEyes. Cisco ThousandEyes allows you to monitor your users’ digital experience against software as a service and on-prem applications, regardless of where they are, through the essential elements of your SASE architecture.
SASE is not just one virtual machine (VM) or virtual network function; it comprises various technologies or VNFs such as SD-WAN, SWG, VPN, and ZTNA.
A) SD-WAN: A Good Starting Point
We know the SASE definition and the convergence of networking and security in cloud-native solutions with global PoP. Cisco SD-WAN is a great starting point for your Cisco SASE solution, especially SD-WAN security, which has been mainstream for a while now. But what would you say about gaining the correct visibility into your SASE model? We have a lot of networking and security functionality now bundled into PoPs, along with different ways to connect to the PoP, whether you are at home or working from the branch office.
B) Connecting To The SASE PoPs
So, if you are at home, you will have a VPN client and go directly to Cisco Umbrella SASE. If you are in the Office, you will likely connect to the SASE PoP or on-premise application via Cisco SD-WAN. The SD-WAN merges with the SASE PoP with redundant IPsec tunnels. You can have up to 8 IPsec tunnels with four active tunnels. The automated policy can be set up between Cisco vManage and Cisco Umbrella, so it’s a good interaction.
C) Cisco Umbrella SASE
Cisco Umbrella SASE is about providing secure connectivity to our users and employees. We need to know precisely what they are doing and not always blame the network when there is an issue. Unfortunately, the network is easy to blame, even though it could be something else.
Scenario: Remote Worker: Creating a SASE VPN
Let’s say we have a secure remote worker. They need to access the business application that could be on-premises in the enterprise data center or served in the cloud. So, users will initiate their SASE VPN client to access a VPN gateway for on-premise applications and then land on the corporate LAN. Hopefully, the LAN will be tied down with microsegmentation, and the SASE VPN users will not get overly permissive broad access.
Suppose the applications are served over the Internet in a public cloud SaaS environment. In this case, the user must go through Cisco Umbrella, not to the enterprise data center but to the cloud. You know that Cisco Umbrella SASE will have a security stack that includes DNS-layer filtering, CASB, and URL filtering. DNS-layer filtering is the first layer of defense.
SASE VPN: Identity Service
In both cases, working remotely or from the branch office, some Identity services may fall under the zero trust network access (ZTNA) category. Identity services are done with Cisco Duo. CyberArk also has complete identity services.
These identity providers offer identity services such as Single-Sign-On (SSO) and Multi-Factor Authentication (MFA) to ensure users are who they say they are. They present users with multiple MFA challenges and a seamless experience with SSO via an identity portal.
**Out of your control**
In both use cases of creating an SASE VPN, we need visibility into several areas that are out of your control. For example, suppose the user works from home. In that case, we will need visibility into their WiFi network, the secure SASE VPN tunnel to the nearest Umbrella PoP, the transit ISP, and the SASE security functions.
**Require Full Visibility**
We need visibility into numerous areas, and each region is different. But one thing that they share is that they are all out of our control. Therefore, we must question and gain complete visibility into something out of our control.
We will have similar problems with edge use cases where workers work from branch sites. If these users go to the Internet, they will still use the Cisco Umbrella SASE security stack, but it will go through SD-WAN first.
Monitoring SD-WAN
However, using SD-WAN will allow us to monitor another part. So, with SD-WAN, we add another layer of needed visibility into the SD-WAN overlay and underlay. The SD-WAN underlay will have multiple ISPs, components, and decades-old equipment.
A: Overlay and Application Mappings
We will have different applications mapped to other overlays for the overlay network, potentially changing them on the fly based on performance metrics. The diagram below shows that some application types prefer different paths and network topologies based on performance metrics such as latency.
B: New Monitoring Tools
With SD-WAN, the network overlay is now entirely virtualized, allowing an adaptive, customized network infrastructure that responds to an organization’s changing needs. So when you move to a SASE environment, you are becoming more dependent on an increasing number of external networks and services that you do not own and that traditional tools can’t monitor, resulting in blind spots that will lead to gaps in security and many operational challenges to moving to SASE.
Cisco ThousandEyes: Different Vantage Points.
Cisco ThousandEyes provides visibility end-to-end across your SASE environment. It allows you to be proactive and see problems before they happen, reducing your time to resolution. Remember that today, we have a complex environment with many new and unpredictable failure modes. Having the correct visibility lets you control the known and unknown failure modes.
Cisco ThousandEyes can also give you actionable data. For example, when service degradation occurs, you can quickly identify where the problem is. So, your visibility will need to be actionable. To gain actionable visibility, you need to monitor different things from different levels. One way to do this is with other types of agents.
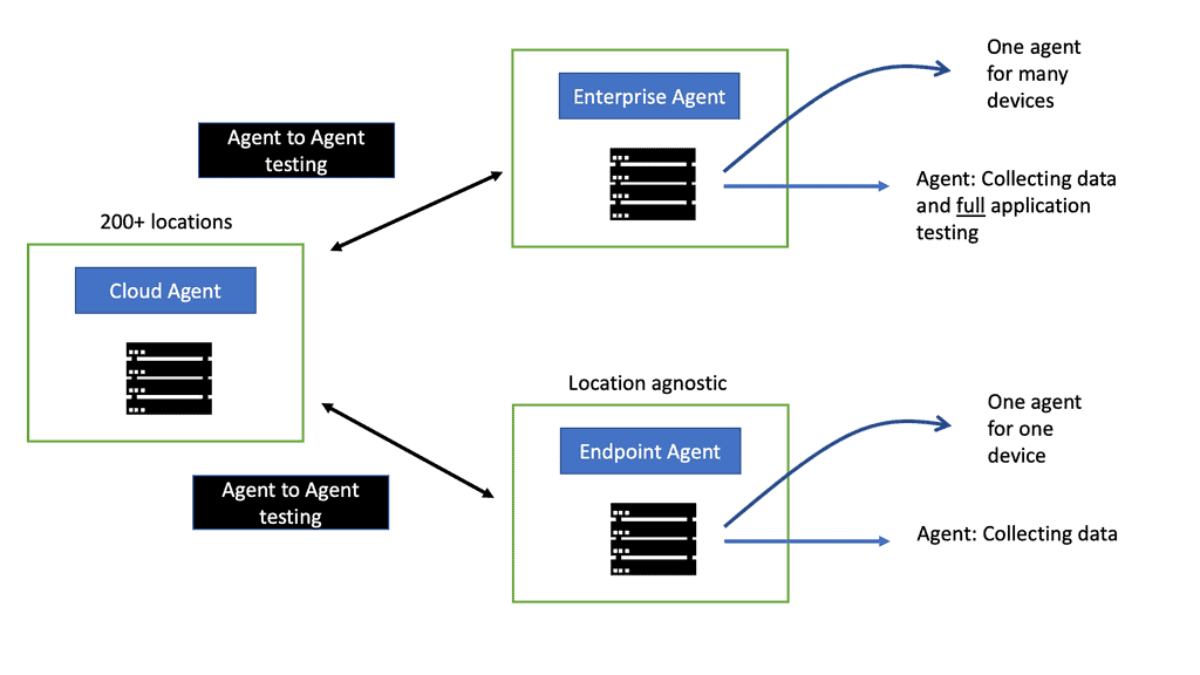
Cloud, Enterprise, and End-user Vantage Points
Using a global collective of cloud, enterprise, and end-user vantage points, ThousandEyes enables organizations to see any network, including those belonging to Internet and cloud providers, as if it were their own—and to correlate this visibility with application performance and employee experience.
From Thousand Eyes’ different vantage points, which are based on deploying agents, we can see the layer 3 hop-by-hop underlays from remote users and SD-WAN sites to secure edge and from secure edge to application servers SaaS application performance, including monitoring login availability and application workflows, service dependency monitoring, including secure edge PoP, and DNS servers.
**Example of an Issue: HTTP Response Time**
That’s quite a lot of areas to grasp. So, let’s say you are having performance issues with Office365, and the response time has increased. First, you would notice an increase in HTTP response time from a specific office. The next stage would be to examine the network layer and see an increase in latency. So, in this case, we have network problems.
Then, you can investigate the problem further using the packet visualization Cisco ThousandEyes offers to pinpoint precisely where it is happening. The packet visualization shows you the exact path of the Office to the Internet via Umbrella. It provides all the legs of the Internet and can pinpoint the problem to the specific device. So now we have end-to-end visibility via this remote worker right to the application.
Cisco ThousandEyes Agents
Endpoint Agent Testing:
The secure remote worker could be on the move and working from anywhere. In this case, you need the ThousandEyes Endpoint agent. The Endpoint agent performs active application and network performance tests and passively collects performance data, such as WiFi and device-level metrics like CPU and memory.
It also detects and monitors any SASE VPN, other VPN gateways, and proxies. The most crucial point to note about the Endpoint agent is that it follows the user regardless of where they work, whether in the branch office or remote locations. The endpoint agent is location-agnostic. However, creating a baseline for users with this type of movement will be challenging.
**Passive Monitoring**
The endpoint agent, by default, does some passive monitoring. WiFi performance is a metric that always sees the percentage of retransmitted packets that would indicate a problem occurring. If the user is working from home and saying this application is not working, you can tell if the WiFi is now working and ask them to carry out the necessary troubleshooting if the issue is at their end.
The endpoint agent also automatically performs default gateway networking testing. This is synthetic network testing using the default gateway. Remote working has an extensive internal network, so you can map it out and help them troubleshoot.
**Underlay Network Testing**
They can test the underlay network to the VPN termination points. So, if you are on a VPN, you have one hop! But if you need to determine any packet loss, etc., you must see the exact underlay. The underlay testing can tell you if there is a problem with the upstream ISP or the VPN termination points.
Enterprise Agent Testing:
The Enterprise agent is set up from the Endpoint agent. The Enterprise agent has, on top of it, complete application testing. Unlike the endpoint agents, it can do page load testing. Using Webex, you can set up the RTP tests for the agent running in the various WebEx data centers.
Then, we have the secure edge design, where the users work from a branch office. This is where we have an Enterprise agent—one agent from all users working in the Office. So, one agent for all users and devices in the LAN can be installed on several device types—for example, Cisco Catalyst 8000 or ISR 4000 series. Or if you can’t install it on a Cisco device, you can install it as a Docker container or in a smaller office; you can deploy it on a Raspberry PI.
**Network Performance Testing**
It performs active application and network performance testing, similar to the Endpoint agent. However, one main difference is that it can perform complex web application tests. The Enterprise agent has a fully-fledged browser on top of it, and it can open up a web application, download images needed to load the page load event and log in to the application.
This is an essential test for the zero trust network access (ZTNA) category, as it supports complete web testing for applications beyond SSO. It can also test VPN and the SDN overlay and underlay. In addition, it provides a continuous baseline regardless of whether there are any active users. The baseline is 24/7, and you can immediately know if there are problems. This is compared to the Endpoint agent, which can’t provide a baseline due to choppy data.
Cisco ThousandEyes also has a Cloud agent that can augment the Enterprise agent. The Cloud agent is installed in over 200 locations worldwide and in WebEx data centers. Consider the cloud agent to increase the enterprise agent. It allows you to do two-way networking and bidirectional testing. Here, we can test agent to agent.
SD-WAN Underlay Visibility
The enterprise agent can also test the SD-WAN underlay. In this testing, you can configure some data policies and allow the network test to go into the underlay. You can even test the Umbrella IPsec Gateway or the SD-WAN router in the data center, which gives you hop-by-hop insights into the underlay.
Device Layer Visibility
We also have device layer visibility. Here, we gather network device topology to gain visibility into the performance of the secure edge internal devices. This will show you all the Layer 3 nodes in your network, firewall, load balancer, and other Layer 2 devices.
Summary: SASE Visibility with Cisco ThousandEyes
In today’s digital landscape, the demand for secure and efficient network connectivity is higher than ever. With the rise of remote work and cloud adoption, organizations are turning to Secure Access Service Edge (SASE) solutions to streamline their network infrastructure. Cisco Thousandeyes emerges as a powerful tool in this realm, offering enhanced visibility and control. In this blog post, we explored the key features and benefits of Cisco Thousandeyes, shedding light on how it can revolutionize SASE visibility.
Understanding SASE Visibility
To grasp the importance of Cisco Thousandeyes, it’s crucial to comprehend the concept of SASE visibility. SASE visibility refers to monitoring and analyzing network traffic, performance, and security across an organization’s network infrastructure. It provides valuable insights into user experience, application performance, and potential security threats.
The Power of Cisco Thousandeyes
Cisco Thousandeyes empowers organizations with comprehensive SASE visibility that extends across the entire network. By leveraging its advanced monitoring capabilities, businesses gain real-time insights into network performance, application behavior, and end-user experience. With Thousandeyes, IT teams can identify and troubleshoot issues faster, ensuring optimal network performance and security.
Key Features and Functionalities
In this section, we will delve into the key features and functionalities offered by Cisco Thousandeyes. These include:
1. Network Monitoring: Thousandeyes provides end-to-end visibility, allowing organizations to monitor their network infrastructure from a single platform. It tracks network performance metrics, such as latency, packet loss, and jitter, enabling proactive issue resolution.
2. Application Performance Monitoring: With Thousandeyes, businesses can gain deep insights into application performance across their network. IT teams can identify bottlenecks, optimize routing, and ensure consistent application delivery to enhance user experience.
3. Security Monitoring: Cisco Thousandeyes offers robust security monitoring capabilities, enabling organizations to detect and mitigate potential threats. It provides visibility into network traffic, identifies anomalies, and facilitates rapid incident response.
Integration and Scalability
One of the significant advantages of Cisco Thousandeyes is its seamless integration with existing network infrastructure. It can integrate with various networking devices, cloud platforms, and security tools, ensuring a cohesive and scalable solution. This flexibility allows businesses to leverage their current investments while enhancing SASE visibility.
Conclusion:
In conclusion, Cisco Thousandeyes proves to be a game-changer in SASE visibility. Its comprehensive monitoring capabilities empower organizations to optimize network performance, ensure application reliability, and enhance security posture. By embracing Cisco Thousandeyes, businesses can journey toward a more efficient and secure network infrastructure.
- DMVPN - May 20, 2023
- Computer Networking: Building a Strong Foundation for Success - April 7, 2023
- eBOOK – SASE Capabilities - April 6, 2023