Internet of Things Theory
The Internet of Things (IoT) is a concept that has rapidly gained momentum in recent years, transforming the way we live and interact with technology. With the proliferation of smart devices, interconnected sensors, and advanced data analytics, IoT is revolutionizing various industries and reshaping our daily lives. In this blog post, we will explore the fundamental aspects of the Internet of Things and its potential impact on our future.
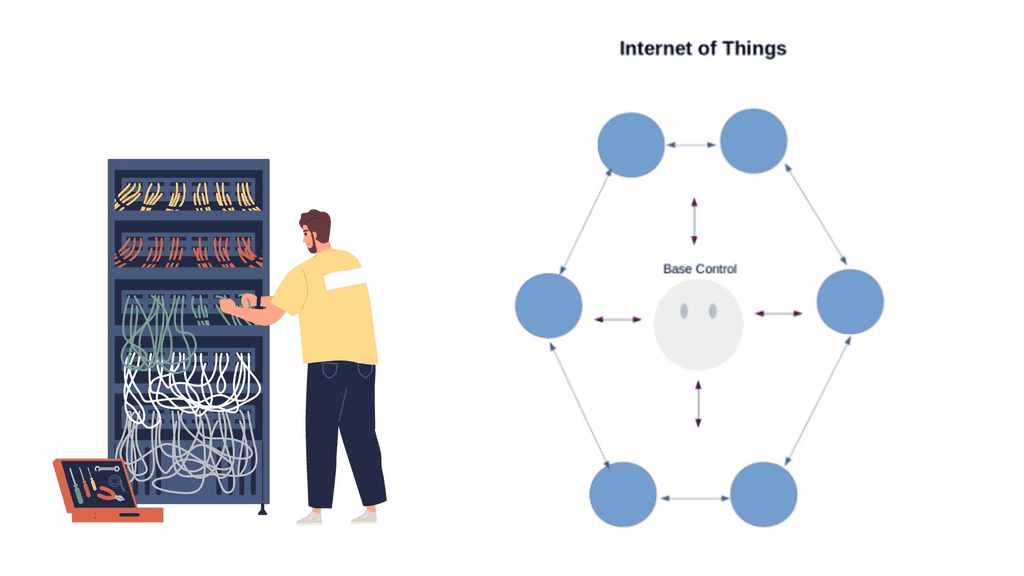
The Internet of Things refers to the interconnectivity of physical devices, vehicles, appliances, and other objects embedded with sensors, software, and network connectivity. These devices are capable of collecting and exchanging data, enabling them to communicate and interact with each other without human intervention. IoT is transforming how we perceive and utilize technology, from smart homes and cities to industrial applications.
Sensors and Actuators: At the heart of the Internet of Things lies a network of sensors and actuators. Sensors collect data from the physical world, ranging from temperature and humidity to motion and light. These devices are equipped with the ability to detect and measure specific parameters, providing valuable real-time information.
Actuators, on the other hand, enable physical actions based on the data received from sensors. They can control various mechanisms, such as opening and closing doors, turning on and off lights, or regulating the temperature in a room.
Communication Protocols: For the IoT to function seamlessly, effective communication protocols are essential. These protocols enable devices to transmit data between each other and to the cloud. Some popular communication protocols in the IoT realm include Wi-Fi, Bluetooth, Zigbee, and LoRaWAN. Each protocol possesses unique characteristics that make it suitable for specific use cases. For instance, Wi-Fi is ideal for high-speed data transfer, while LoRaWAN offers long-range connectivity with low power consumption.
Cloud Computing and Data Analytics: The massive amount of data generated by IoT devices requires robust storage and processing capabilities. Cloud computing plays a pivotal role in providing scalable infrastructure to handle this data influx. By leveraging cloud services, IoT devices can securely store and access data, as well as utilize powerful computational resources for advanced analytics. Data analytics, in turn, enables organizations to uncover valuable insights, optimize operations, and make data-driven decisions.
Edge Computing: While cloud computing offers significant advantages, some IoT applications demand real-time responsiveness, reduced latency, and enhanced privacy. This is where edge computing comes into play. Edge devices, such as gateways and edge servers, bring computational power closer to the data source, enabling faster processing and decision-making at the edge of the network. Edge computing minimizes the need for constant data transmission to the cloud, resulting in improved efficiency and reduced bandwidth requirements.Matt Conran
Highlights: Internet of Things Theory
IoT Theory
IoT: The Fundamentals:
The IoT theory is built on the foundation of connectivity and intercommunication. It involves the integration of sensors, software, and networks to enable data exchange between devices. This section will delve into the core components of the IoT, including sensors, actuators, connectivity protocols, and cloud platforms that form the backbone of this interconnected ecosystem.
IoT has already made a significant impact on various aspects of our daily lives. In homes, smart devices like voice-activated assistants, security cameras, and lighting systems enhance convenience and security. In the healthcare sector, IoT enables remote patient monitoring, improving healthcare delivery and patient outcomes. Meanwhile, in industries such as agriculture, IoT is revolutionizing farming practices through precision agriculture, where sensors and analytics help optimize crop yields and resource management.
The Internet Transformation:
The Internet is transforming, and this post discusses the Internet of Things Theory and highlights Internet of Things access technologies. Initially, we started with the Web and digitized content. The market then moved to track and control the digitized world with, for example, General Packet Radio Service ( GPRS ).
Machine-to-machine ( M2M ) connectivity introduces a different connectivity model and application use case. Now, we embark on Machine Learning, where machines can make decisions with supervised or unsupervised controls. This transformation requires new architecture and technologies to support IoT connectivity, including event stream processing and the 6LoWPAN range.
Note: IoT Theory Key Points:
– The IoT theory revolves around the concept of connecting everyday objects to the internet, enabling them to send and receive data. This section will explain the fundamental principles behind IoT, including sensors, connectivity, and data analysis.
– IoT has permeated various aspects of our daily lives, making activities more convenient and efficient. From smart homes that automate tasks to wearable devices that track health and fitness, this section will explore the numerous applications of IoT in our routines.
– Industries across the board have embraced IoT to streamline operations, enhance productivity, and reduce costs. We will take a closer look at how IoT is transforming manufacturing, transportation, healthcare, and agriculture, among other sectors.
– With the immense potential of IoT come significant impacts and challenges. This section will discuss the positive effects of IoT on sustainability, data analysis, and urban planning, as well as the concerns surrounding privacy, security, and data breaches.
**Distributed Edge Intelligence**
Traditional networks start with a group of network devices and a box-by-box mentality. The perimeter was more or less static. The move to Software-Defined Networking ( SDN ) implements a central controller, pushing networking into the software with the virtual overlay network. As we introduce the Internet of Things theory, the IoT world steadily progresses, and we require an application-centric model with distributed intelligence and time series data.
The Internet of Things theory connects everyday objects to the Internet, allowing them to communicate and share data. This section will provide a comprehensive overview of IoT’s fundamental concepts and components, including sensors, actuators, connectivity, and data analysis.
**Real-world Applications**
IoT has permeated various industries, from smart homes to industrial automation, bringing significant advancements. There are a showcase a range of practical applications, such as smart cities, wearable devices, healthcare systems, and transportation networks. By exploring these examples, readers will understand how IoT reshapes our lives.
**IoT Challenges and Concerns**
While the potential of IoT is immense, some challenges and concerns need to be addressed. This section will delve into data privacy, security vulnerabilities, ethical considerations, and the impact on the workforce. By understanding these challenges, we can work towards creating a safer and more sustainable IoT ecosystem.
The evolution of IoT theory is an ongoing process. In this section, we will explore the future implications of IoT, including the integration of artificial intelligence, machine learning, and blockchain technologies. Additionally, we will discuss the potential benefits and risks that lie ahead as the IoT landscape continues to expand.
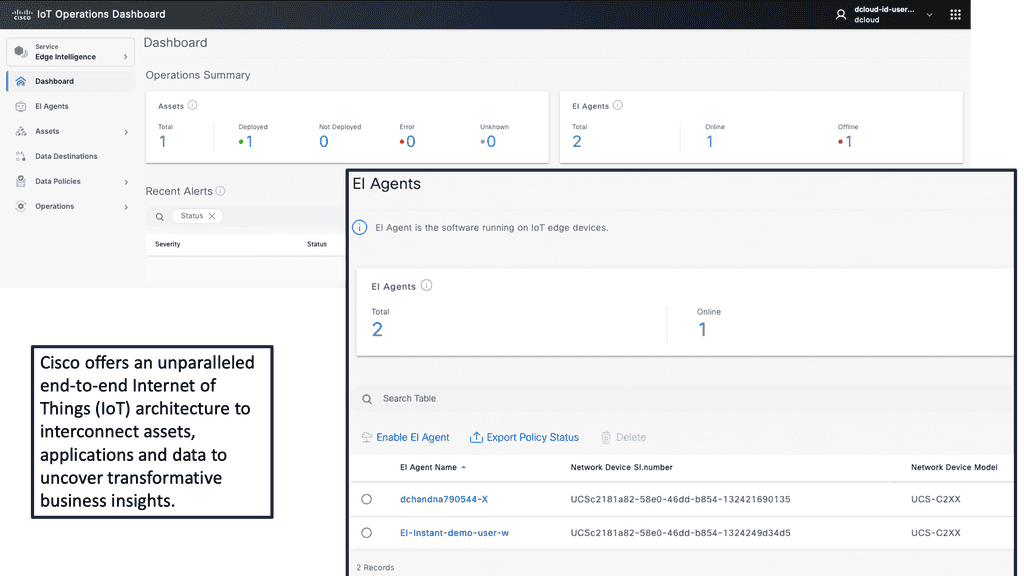
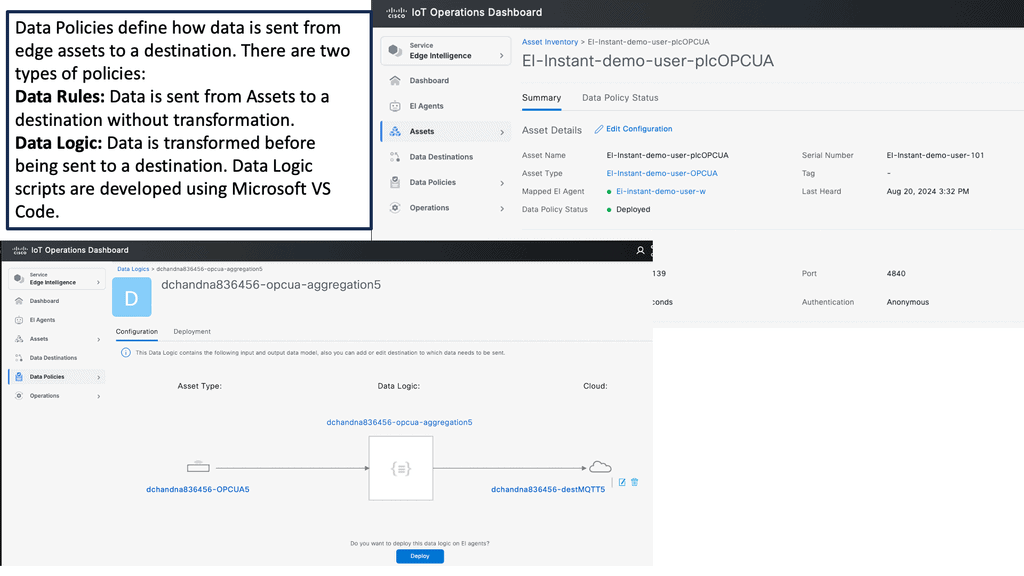
Example Product: Cisco IoT Operations Dashboard
**What is the Cisco IoT Operations Dashboard?**
The Cisco IoT Operations Dashboard is a cloud-based platform designed to simplify the management and monitoring of IoT devices. With its user-friendly interface and robust features, this dashboard allows businesses to seamlessly integrate, manage, and secure their IoT deployments. Whether you’re overseeing a small network of sensors or a vast array of connected devices, the Cisco IoT Operations Dashboard offers a scalable solution that grows with your needs.
**Key Features and Benefits**
1. **Comprehensive Device Management**
The dashboard provides a centralized view of all connected devices, enabling administrators to monitor device status, performance, and connectivity. This holistic approach ensures that any issues can be quickly identified and resolved, minimizing downtime and enhancing productivity.
2. **Enhanced Security**
Security is paramount in any IoT deployment. The Cisco IoT Operations Dashboard incorporates advanced security features, including end-to-end encryption, secure boot, and firmware updates. These measures protect your network from potential threats and ensure the integrity of your data.
3. **Scalability and Flexibility**
As your IoT network expands, the Cisco IoT Operations Dashboard scales effortlessly to accommodate new devices and applications. Its flexible architecture supports a wide range of protocols and standards, making it compatible with diverse IoT ecosystems.
**Real-World Applications**
The versatility of the Cisco IoT Operations Dashboard makes it suitable for various industries. In manufacturing, for instance, it can monitor machinery health and predict maintenance needs, reducing downtime and operational costs. In agriculture, the dashboard can track soil moisture levels and weather conditions, optimizing irrigation and improving crop yields. The potential applications are vast, underscoring the dashboard’s value across different sectors.
**Getting Started with Cisco IoT Operations Dashboard**
Implementing the Cisco IoT Operations Dashboard is straightforward. Businesses can begin by identifying their IoT needs and selecting the appropriate devices and sensors. Once the hardware is in place, the dashboard provides guided setup instructions to connect and configure devices. With its intuitive interface, users can quickly familiarize themselves with the platform and start leveraging its features to enhance their operations.
Related: Before you proceed, you may find the following helpful.
Internet of Things Theory
Internet of Things Theory and Use Cases
Applications of IoT:
The applications of IoT are vast and encompass various sectors, including healthcare, agriculture, transportation, manufacturing, and more. IoT is revolutionizing patient care in healthcare by enabling remote monitoring, wearable devices, and real-time health data analysis.
The agricultural industry benefits from IoT by utilizing sensors to monitor soil conditions and weather patterns and optimize irrigation systems. IoT enables intelligent traffic management, connected vehicles, and advanced navigation systems in transportation, enhancing efficiency and safety.
**Benefits and Challenges**
The Internet of Things offers numerous benefits, such as increased efficiency, improved productivity, enhanced safety, and cost savings. Smart homes, for instance, enable homeowners to control and automate various aspects of their living spaces, resulting in energy savings and convenience. IoT allows predictive maintenance, optimizes operations, and reduces downtime in the industrial sector.
However, with the vast amount of data generated by IoT devices, privacy and security concerns arise. Safeguarding sensitive information and protecting against cyber threats are critical challenges that must be addressed to ensure IoT’s widespread adoption and success.
**Enhanced Efficiency and Productivity**
With IoT, massive automation and real-time data collection have become possible. This translates into increased efficiency and productivity across industries. From smart factories optimizing production processes to automated inventory management systems, IoT streamlines operations and minimizes human intervention.
**Improved Quality of Life**
IoT has the potential to enhance our daily lives significantly. Smart homes with IoT devices allow seamless control of appliances, lighting, and security systems. Imagine waking up to a house that adjusts the temperature to your preference, brews your morning coffee, and even suggests the most efficient route to work based on real-time traffic data.
Leveraging IoT can significantly enhance safety and security measures. Smart surveillance systems can detect and react to potential threats in real-time. IoT-enabled wearable devices can monitor vital signs and send alerts during emergencies, ensuring timely medical assistance.
**Environmental Sustainability**
IoT plays a crucial role in promoting environmental sustainability. Smart grids enable efficient energy management and reduce wastage. IoT devices can monitor ecological parameters like air quality and water levels, facilitating proactive measures to protect our planet.
**The Future of IoT**
The Internet of Things has only scratched the surface of its potential. As technology advances, we can expect IoT to become more sophisticated and integrated into our daily lives.
The emergence of 5G networks will enable faster and more reliable connectivity, unlocking new possibilities for IoT applications. From intelligent cities that optimize energy consumption to personalized healthcare solutions, the future of IoT holds immense promise.
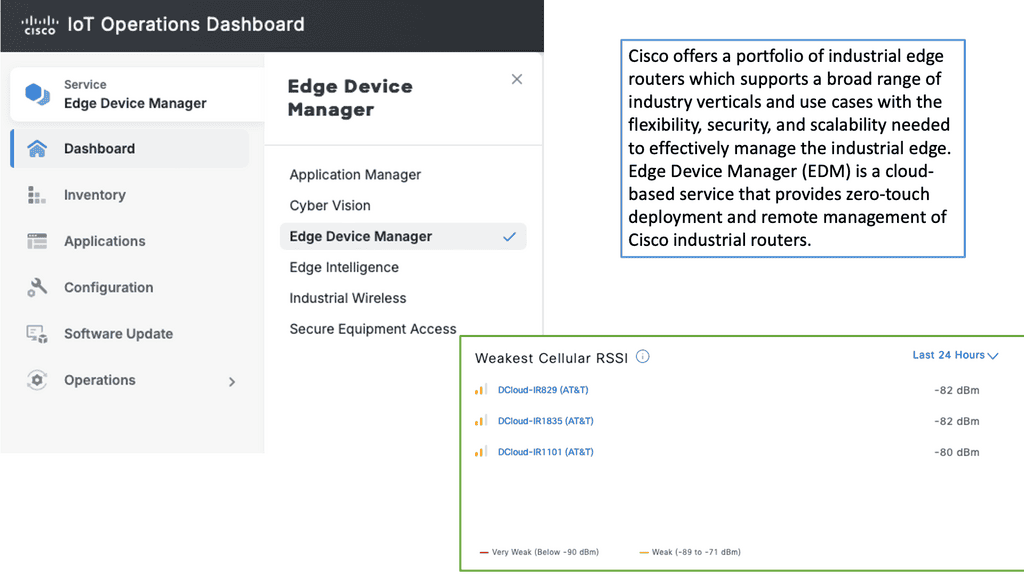
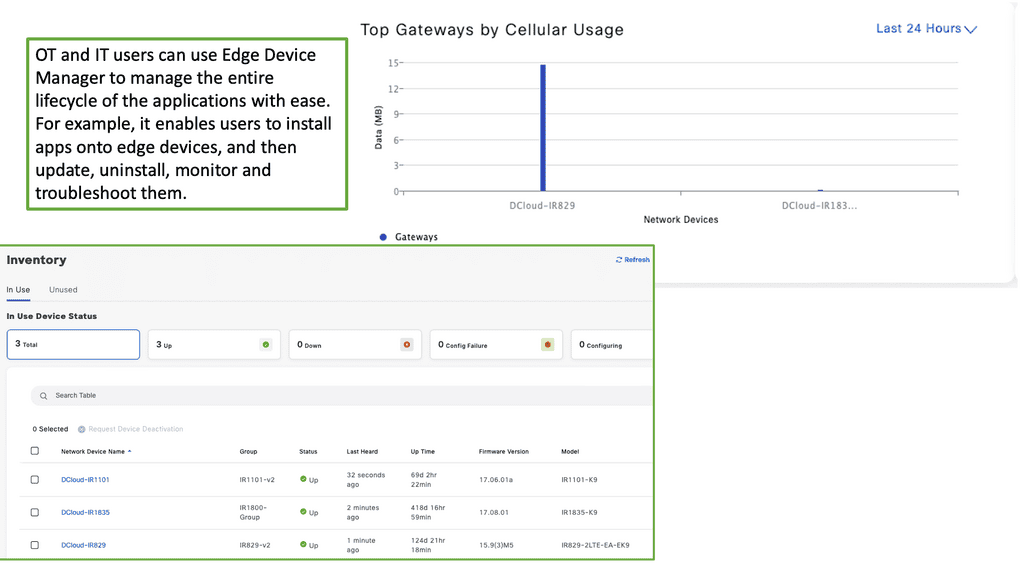
Example Product: Cisco Edge Device Manager
### What is Cisco Edge Device Manager?
Cisco Edge Device Manager is a cloud-based platform that provides centralized management for edge devices. It allows network administrators to monitor, configure, and troubleshoot devices remotely, thereby reducing the need for on-site interventions. This tool is particularly beneficial for businesses with distributed networks, where maintaining consistent performance can be challenging.
### Key Features and Benefits
#### Centralized Management
One of the standout features of Cisco Edge Device Manager is its ability to provide a single pane of glass for network management. Administrators can oversee all edge devices from a unified interface, making it easier to implement updates, monitor performance, and address issues promptly.
#### Enhanced Security
Security is a top priority in today’s digital age. Cisco Edge Device Manager integrates advanced security protocols to ensure that all managed devices are protected against potential threats. Features such as automated firmware updates and real-time security alerts help maintain a robust security posture.
#### Scalability and Flexibility
Whether you’re managing a small network or a vast array of devices across multiple locations, Cisco Edge Device Manager scales effortlessly to meet your needs. Its flexible architecture supports a wide range of applications, making it an ideal choice for businesses of all sizes.
### Integration with Cisco IoT Operations Dashboard
Cisco Edge Device Manager is a key component of the Cisco IoT Operations Dashboard, a holistic platform designed to streamline IoT operations. This integration allows for seamless data flow and enhanced visibility across all connected devices. By leveraging the capabilities of both tools, businesses can achieve greater operational efficiency and drive innovation.
### Real-World Applications
#### Smart Cities
In smart city deployments, managing a multitude of connected devices can be daunting. Cisco Edge Device Manager simplifies this task by providing centralized control, ensuring that all devices operate optimally and securely.
#### Industrial Automation
In industrial settings, downtime can be costly. With Cisco Edge Device Manager, companies can proactively monitor equipment, perform predictive maintenance, and minimize disruptions, thereby enhancing productivity and reducing operational costs.
Back to Basics With the Internet of Things Theory
When introducing the Internet of Things theory, we need to examine use cases. We know that IoT enables everyday physical objects, such as plants, people, animals, appliances, objects, buildings, and machines, to transmit and receive data—the practical use case for IoT is bound only to the limits of our imagination.
The devices section is where we will see the most innovation and creativity. For example, there has been plenty of traction in the car industry as IoT introduces a new era of hyperconnected vehicles. Connected cars in a mesh of clouds form a swarm of intelligence.
The ability to retrieve data from other vehicles opens up new types of safety information, such as black ice and high winds detection.
A: – ) No one can doubt that the Internet has a massive impact on society. This digital universe enables all types of mediums to tap into and communicate. In one way or another, it gets woven into our lives, maybe even to the point where people decide to use the Internet as a base point in starting their businesses. More importantly, the Internet is a product made by “people.”
B: – ) we are heading into a transformation stage that will make our current connectivity model look trivial. The Internet of Things drives a new Internet, a product made by “things,” not just people. These things or smart objects consist of billions or even trillions of non-heterogeneous devices. The ability of devices to sense, communicate, and acquire data helps build systems that manage our lives better.
C: – ) are beginning to see the introduction of IoT into what’s known as smart cities. In Boston, an iPhone app called Catchthebusapp informs application owners of public transport vehicles’ location and arrival times. GPRS trackers installed on each car inform users when they are running late.
D: – ) example proves that we are about to connect our planet, enabling a new way to interact with our world. The ability to interact, learn, and observe people and physical objects is a giant leap forward. Unfortunately, culture is one of the main factors for resistance.
Internet of thing Theory and IoT security
Due to IoT’s immaturity, concerns about its security and privacy are raised. The Internet of Things Security Foundation started in 2015 in response to these concerns. Security is often an afterthought because there is a rush to market with these new devices.
This leaves holes and gaps for cybercriminals to exploit. It’s not just cybercriminals who can access information and data; it’s so easy to access personal information nowadays. This explains the rise in people utilizing Proxy Services to protect their identity and allow for some privacy while protecting against hackers and those wanting to obtain personal data. The IoT would benefit from this proxy service.
A recent article on the register claims that a Wi-Fi baby heart monitor may have the worst IoT security of 2016. All data between the sensor and base station is unencrypted, meaning an unauthenticated command over HTTP can compromise the system. Channels must be encrypted to overcome information and physical tampering.
Denial-of-sleep attacks
IoT also opens up a new type of DDoS attack called denial-of-sleep attacks that drain a device’s battery. Many of these devices are so simplistic in design that they don’t support sophisticated security approaches from a hardware and software perspective. Many IoT processors are not capable of supporting strong security and encryption.
IoT opens up the back door to potentially billions of unsecured devices used as a resource to amplify DDoS attacks. The Domain Name System ( DNS ) is an existing lightweight protocol that can address IoT security concerns. It can tightly couple the detection and remediation of DDoS tasks. In addition, analyzing DNS queries with machine-learning techniques predicts malicious activity.
Internet of Things Theory: How Does it Work?
IoT is a concept, not a new technology. It connects data so applications can derive results from viewing the analytics. However, it’s a complex environment and not a journey a single company can take. Partnerships must be formed to offer a total data center-to-edge solution for a complete end-to-end solution.
Sense & Communicate
To have something participate in the Internet of Things, we must follow a few steps. At a fundamental level, we have intelligent objects that can “sense and communicate.” These objects must then be able to interact and collaborate with other things on the Internet.
These things or smart objects comprise a physical entity and a digital function. The physicals include sensory capabilities to measure temperature, vibration, and pollution data.
Sensors transmit valuable data to an Internet of Things Platform. The central IoT platform integrates data from many heterogeneous devices and shares the analytics with various applications addressing use cases that solve specific issues. The actuators perform a particular task – opening a window or a lock, changing traffic lights, etc.
Data Flow & Network Connectivity
The type of device depicts the chosen network connectivity. We have two categories: wireless and Wired. For example, a hospital would connect to the control center with a wired connection ( Ethernet or Serial ), while other low-end devices might use a Low-Power, Short-Range network.
Low-power short-range networks are helpful for intelligent homes with point-to-point, star, and mesh topologies. Devices using this type of network range between tens and hundreds of meters. They require long battery life, medium density, and low bandwidth. The device type does depict the network. If you want the battery to last ten years, you need the correct type of network for that.
Fog computing
Machine learning and IoT go hand in hand. With the sheer scale of IoT devices, there is too much data for the human mind to crunch. This results in the analysis carried out on the fly between devices or distributed between gateways at the edge. Fog computing pushes processing and computation power down to the actual device.
This is useful if there are expensive satellite links and when it is cost-effective to keep computation power at the device level instead of sending it over network links to the control center.
It’s also helpful when network communications increase the battery consumption in the sensor node. We expect to see a greater demand for fog computing systems as the IoT becomes more widely accepted and incorporated.
6LoWPAN
Gartner released a report stating over 20 billion devices will participate in the Internet of Things by 2020. A person may have up to 5,000 devices to interact with. This type of scale would not be possible without the adoption of IPv6 and 6LoWPAN. 6LoWPAN Range stands for Low-power Wireless Personal Area Networks. It enables small, low-powered, memory-constrained devices to connect and participate in IoT.
Its base topology has several mesh-type self-healing 6LoWPAN nodes connected to the Edge router for connectivity and integration to the Internet. The edge routers act as a bridge between the RF and Ethernet networks.
Closing Points on IoT Theory
To understand IoT theory, it’s essential to grasp the fundamental components that make it tick. The primary elements include sensors, connectivity, and data processing. Sensors are embedded in devices to collect data, which is then transmitted via various connectivity options such as Wi-Fi, Bluetooth, or cellular networks. Once the data reaches its destination, advanced processing systems analyze and interpret this information, leading to actionable insights. These building blocks create a seamless network of communication between devices, paving the way for smart solutions across industries.
The applications of IoT are vast and varied, extending across multiple sectors. In healthcare, IoT devices can monitor patients’ vital signs in real-time, ensuring timely intervention when necessary. In agriculture, sensors can track soil moisture levels and adjust irrigation systems accordingly, optimizing water usage. Meanwhile, in smart cities, IoT-powered infrastructure can improve traffic management and reduce energy consumption. These innovations demonstrate the transformative potential of IoT theory, driving efficiency and innovation in countless fields.
Despite its promising potential, IoT theory is not without its challenges. Security remains a top concern, as the proliferation of connected devices increases the risk of cyberattacks. Ensuring data privacy and protecting sensitive information are critical priorities for developers and users alike. Additionally, the sheer volume of data generated by IoT devices presents challenges in terms of storage and processing. Addressing these issues requires ongoing research and development to ensure the secure and efficient implementation of IoT solutions.
Summary: Internet of Things Theory
In this digital age, the Internet of Things (IoT) has become integral to our lives. IoT has revolutionized how we interact with technology, from smart homes to connected devices. In this blog post, we explored the various aspects of the Internet of Things and its impact on our daily lives.
What is the Internet of Things?
The Internet of Things refers to the network of interconnected devices and objects that can communicate and exchange data. These devices, equipped with sensors and connectivity, can range from smartphones and wearables to household appliances and industrial machinery. The IoT enables seamless communication and automation, making our lives more convenient and efficient.
Applications of the Internet of Things
The applications of IoT are vast and diverse. Smart homes, for instance, leverage IoT technology to control lighting, temperature, and security systems remotely. Healthcare systems also benefit from IoT, with wearable devices monitoring vital signs and transmitting real-time health data to healthcare professionals. Furthermore, industries are utilizing IoT to optimize production processes, track inventory, and enhance overall efficiency.
Challenges and Concerns
While the Internet of Things offers numerous advantages, it presents certain challenges and concerns. Security and privacy issues arise due to the vast amount of data being generated and transmitted by IoT devices. As more devices connect to the internet, the potential for cyber-attacks and data breaches increases. Additionally, the sheer complexity of managing and securing a large-scale IoT network poses a significant challenge.
The Future of IoT
The Internet of Things is poised for even more significant growth and innovation as technology advances. With the advent of 5G networks, the connectivity and speed of IoT devices will vastly improve, opening up new possibilities. Moreover, integrating artificial intelligence and machine learning with IoT promises smarter and more autonomous systems that can adapt to our needs.
Conclusion:
The Internet of Things has undoubtedly transformed how we live and interact with our surroundings. IoT has become an integral part of our digital ecosystem, from enhancing convenience and efficiency to driving innovation across industries. However, as we embrace this connected future, it is crucial to address security and privacy challenges to ensure a safe and trustworthy IoT landscape.
- DMVPN - May 20, 2023
- Computer Networking: Building a Strong Foundation for Success - April 7, 2023
- eBOOK – SASE Capabilities - April 6, 2023