Blog
Network Insight.
- Premium Consultancy, Ebooks, Videos and Elearning
Baseline Engineering
Baseline Engineering In today’s fast-paced digital landscape, network performance plays a vital role in ensuring seamless connectivity and efficient operations. Network baseline engineering is a powerful technique that allows organizations to establish a solid foundation for optimizing network performance, identifying anomalies, and planning for future scalability. In this blog post, …
Docker Security Options
Docker Security Options In the ever-evolving world of containerization, Docker has emerged as a leading platform for deploying and managing applications. As the popularity of Docker continues to grow, so does the importance of securing your containers and protecting your valuable data. In this blog post, we will delve into …
Safe-T SDP- Why Rip and Replace your VPN?
SDP VPN Although organizations realize the need to upgrade their approach to user access control, deploying existing technologies is holding back the introduction of Software Defined Perimeter (SDP). A recent Cloud Security Alliance (CSA) report on the “State of Software-Defined Perimeter” states that existing in-place security technologies are …
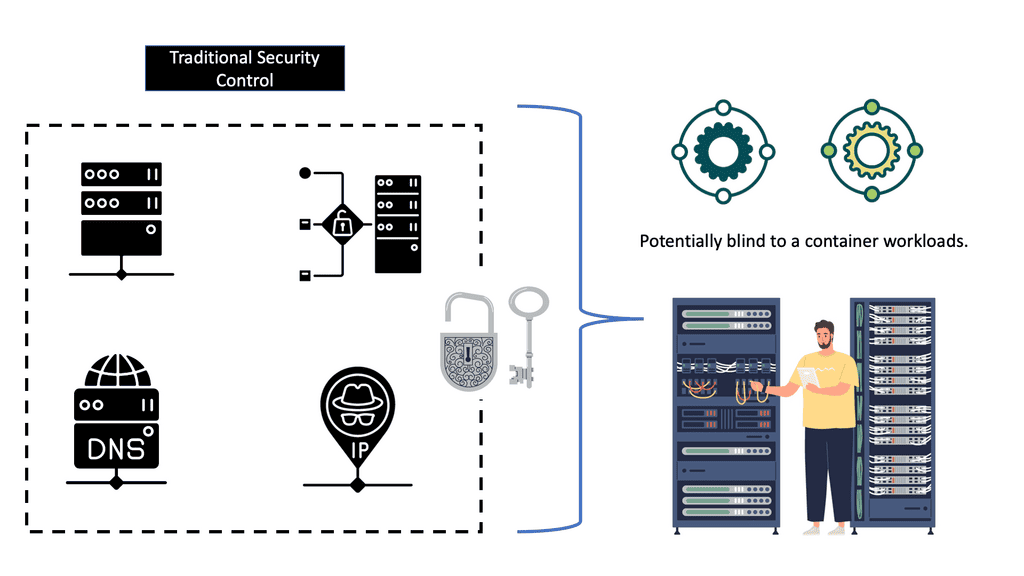
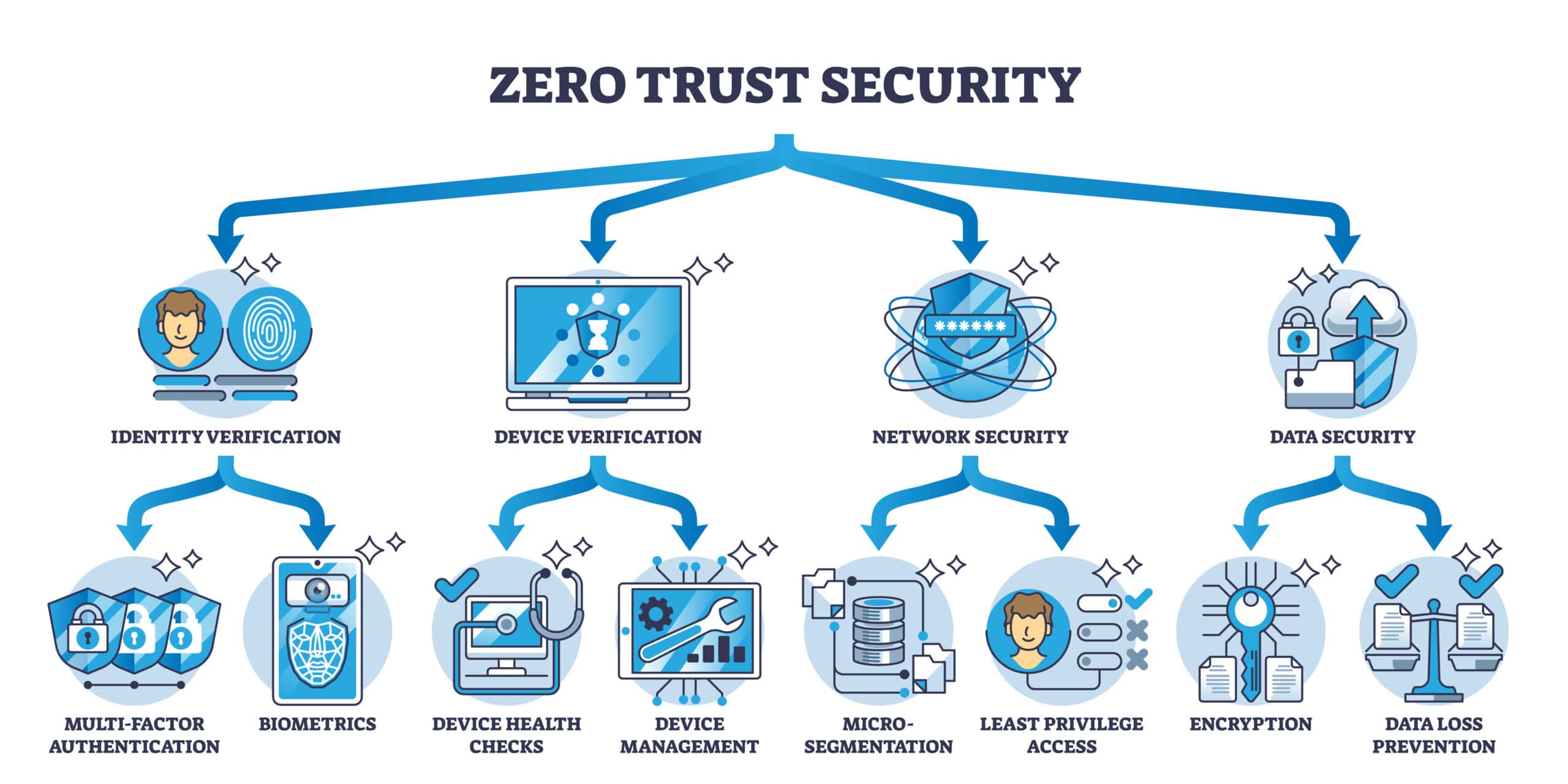
Safe-T; A Progressive Approach to Zero Trust Access
Zero Trust SDP The foundations that support our systems are built with connectivity, not security, as an essential feature. TCP connects before it authenticates. Security policy and user access based on IP lack context and allow architectures with overly permissive access. This will likely result in a brittle …
Remote Browser Isolation
Remote Browser Isolation In today’s digital landscape, where cyber threats continue to evolve at an alarming rate, businesses and individuals are constantly seeking innovative solutions to safeguard their sensitive information. One such solution that has gained significant attention is Remote Browser Isolation (RBI). In this blog post, we will explore …
Intent-Based Networking
Intent Based Networking In today’s rapidly advancing technological landscape, the demand for efficient and intelligent networking solutions continues to rise. Intent-Based Networking (IBN) has emerged as a transformative approach that simplifies network management, enhances security, and enables businesses to align their network operations with their overall objectives. Intent-Based Networking represents …
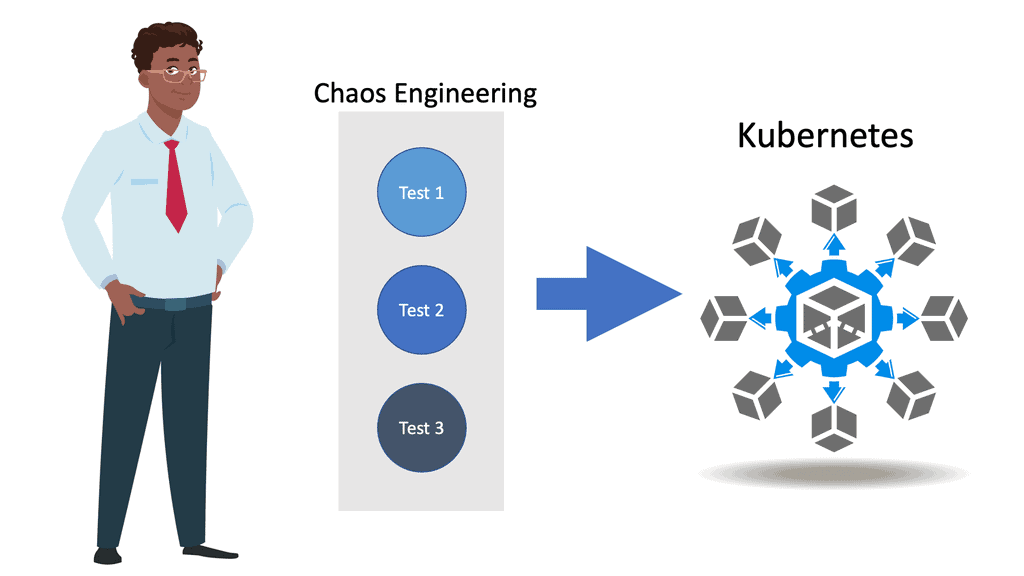
Kubernetes Security Best Practice
Kubernetes Securtiy Best Practices In today’s rapidly evolving technological landscape, Kubernetes has emerged as a powerful platform for managing containerized applications. However, with great power comes great responsibility, especially when it comes to security. In this blog post, we will explore essential best practices to ensure the utmost security in …
Software defined perimeter (SDP) A disruptive technology
Software-Defined Perimeter In the evolving landscape of cybersecurity, organizations are constantly seeking innovative solutions to protect their sensitive data and networks from potential threats. One such solution that has gained significant attention is the Software Defined Perimeter (SDP). In this blog post, we will delve into the concept of SDP, …
Zero Trust: Single Packet Authorization | Passive authorization
Single Packet Authorization In today’s fast-paced world, where digital security is paramount, traditional authentication methods are often susceptible to malicious attacks. Single Packet Authorization (SPA) emerges as a powerful solution to enhance the security of networked systems. In this blog post, we will delve into the concept of SPA, its …
SDP Network
SDP Network The world of networking has undergone a significant transformation with the advent of Software-Defined Perimeter (SDP) networks. These innovative networks have revolutionized connectivity by providing enhanced security, flexibility, and scalability. In this blog post, we will explore the key features and benefits of SDP networks, their impact on …
Ericom Browser Isolation: Making surfing the internet safer
Ericom Browser Isolation Today, organizations cannot know when and where the next attack will surface and how much damage it will cause. The risk is compounded by the fact that castle-and-moat security no longer exists. Network perimeters are fluid, with no clear demarcation points between “outside” and dangerous, …
Removing State from Network Functions
Removing State From Network Functions In recent years, the networking industry has witnessed a significant shift towards stateless network functions. This revolutionary approach has transformed the way networks are designed, managed, and operated. In this blog post, we will explore the concept of removing state from network functions and delve …