Remote Browser Isolation
In today's digital landscape, where cyber threats continue to evolve at an alarming rate, businesses and individuals are constantly seeking innovative solutions to safeguard their sensitive information. One such solution that has gained significant attention is Remote Browser Isolation (RBI). In this blog post, we will explore RBI, how it works, and its role in enhancing security in the digital era.
Remote Browser Isolation, as the name suggests, is a technology that isolates web browsing activity from the user's local device. Instead of directly accessing websites and executing code on the user's computer or mobile device, RBI redirects browsing activity to a remote server, where the web page is rendered and interactions are processed. This isolation prevents any malicious code or potential threats from reaching the user's device, effectively minimizing the risk of a cyberattack.
Remote browser isolation offers several compelling benefits for organizations. Firstly, it significantly reduces the surface area for cyberattacks, as potential threats are contained within a remote environment. Additionally, it eliminates the need for frequent patching and software updates on endpoint devices, reducing the burden on IT teams.
Implementing remote browser isolation requires careful planning and consideration. This section will explore different approaches to implementation, including on-premises solutions and cloud-based services. It will also discuss the integration challenges that organizations might face and provide insights into best practices for successful deployment.
While remote browser isolation offers immense security benefits, it is crucial to address potential challenges that organizations may encounter during implementation. This section will highlight common obstacles such as compatibility issues, user experience concerns, and cost considerations. By proactively addressing these challenges, organizations can ensure a seamless and effective transition to remote browser isolation.Matt Conran
Highlights: Remote Browser Isolation
Understanding Remote Browser Isolation
Remote browser isolation, also known as web isolation or browser isolation, is a cutting-edge security technique that eliminates the risks associated with web browsing. By executing web content in a remote environment, separate from the user’s device, remote browser isolation effectively shields users from malicious websites, zero-day attacks, and other web-based threats.
Remote browser isolation utilizes virtualization technology to create a secure barrier between the user’s device and the internet. When a user initiates a web browsing session, the web content is rendered and executed remotely.
At the same time, only the safe visual representation is transmitted to the user’s browser. This ensures that any potentially harmful code or malware is contained within the isolated environment, preventing it from reaching the user’s device.
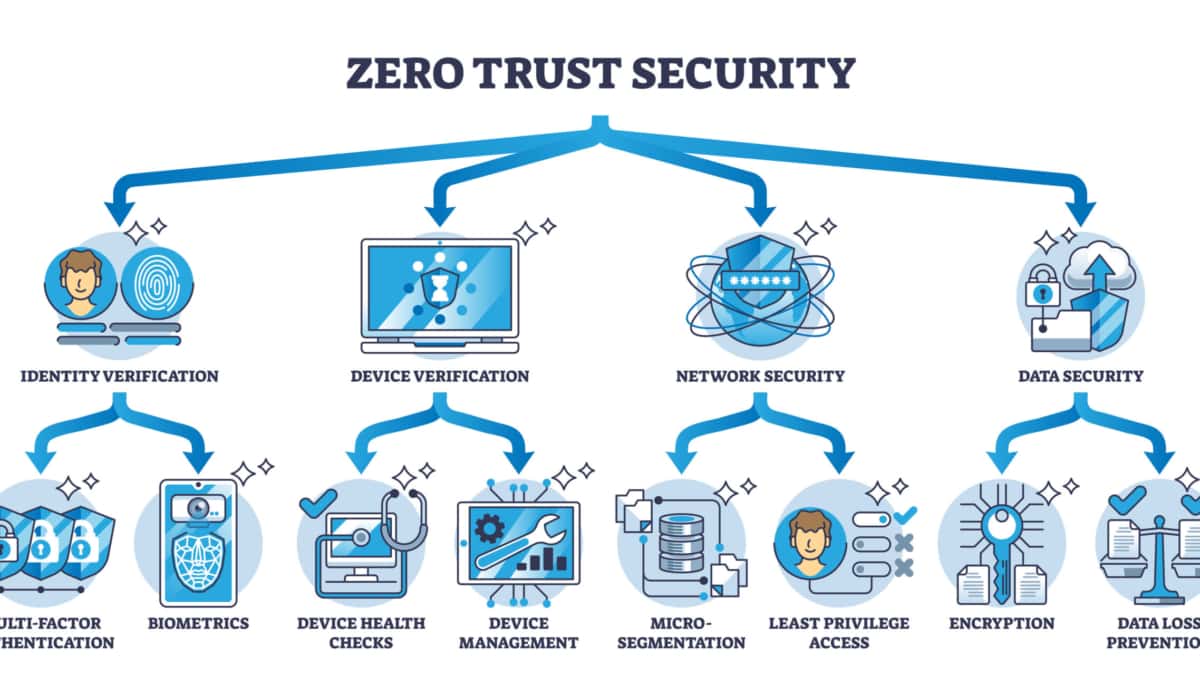
RBI & Zero Trust Principles
In remote browser isolation (RBI), or web isolation, users’ devices are isolated from Internet surfing by hosting all browsing activity in a remote cloud-based container. As a result of sandboxing internet browsing, data, devices, and networks are protected from all types of threats originating from infected websites
In remote browser isolation, Zero-Trust principles are applied to internet browsing. Remote browser isolation isolates websites that are not trusted in a container so that no website code can execute on endpoints rather than determining which sites are good and which are bad.
Challenge: Various Security Threats
The Internet is a business’s most crucial productivity tool and its most outstanding liability since it exposes it to various security threats. Old methods like blocking known risky domains can protect against some web-browsing threats, but they do not prevent other exploitations. In light of the growing number of threats on the internet, how can organizations protect users, data, and systems?
Challenge: Dynamic Environment
Our digital environment has been transformed significantly. Unlike earlier times, we now have different devices, access methods, and types of users accessing applications from various locations. This makes it more challenging to know which communications can be trusted. The perimeter-based approach to security can no longer be limited to just the enterprise’s physical location.
Challenge: A Fluid Perimeter
In this modern world, the perimeter is becoming increasingly difficult to enforce as organizations adopt mobile and cloud technologies. Hence, the need for Remote Browser Isolation (RBI) has become integral to the SASE definition. For example, Cisco Umbrella products have several Zero Trust SASE components, such as the CASB tools, and now RBI is integrated into one solution.
**It’s Just a matter of time**
Under these circumstances, the perimeter is more likely to be breached; it’s just a matter of time. A bad actor would then be relatively free to move laterally, potentially accessing the privileged intranet and corporate data on-premises and in the cloud. Therefore, we must assume that users and resources on internal networks are as untrustworthy as those on the public internet and design enterprise application security with this in mind.
Related: Before you proceed, you may find the following posts helpful for pre-information:
Remote Browser Isolation
A: ) Remote browser isolation (RBI), also known as web isolation or browser isolation, is a web security solution developed to protect users from Internet-borne threats. So, we have on-premise isolation and remote browser isolation.
B: ) On-premise browser isolation functions similarly to remote browser isolation. But instead of taking place on a remote server, which could be in the cloud, the browsing occurs on a server inside the organization’s private network, which could be at the DMZ. So why would you choose on-premise isolation as opposed to remote browser isolation?
C: ) Firstly, performance. On-premise isolation can reduce latency compared to some types of remote browser isolation that need to be done in a remote location.
**The Concept of RBI**
The RBI concept is based on the principle of “trust nothing, verify everything.” By isolating web browsing activity, RBI ensures that any potentially harmful elements, such as malicious scripts, malware, or phishing attempts, cannot reach the user’s device. This approach significantly reduces the attack surface and provides an added layer of protection against threats that may exploit vulnerabilities in the user’s local environment.
So, how does Remote Browser Isolation work in practice? When a user initiates a web browsing session, the RBI solution establishes a secure connection to a remote server instead of directly accessing the website. The remote server acts as a virtual browser, rendering the web page, executing potentially dangerous code, and processing user interactions.
Only the harmless visual representation of the webpage is transmitted back to the user’s device, ensuring that any potential threats are confined to the isolated environment.
Key RBI Advantages & Take Aways
– One critical advantage of RBI is its ability to protect against known and unknown threats. Since the browsing activity is isolated from the user’s device, even if a website contains an undiscovered vulnerability or a zero-day exploit, the user’s device remains protected. This is particularly valuable in today’s dynamic threat landscape, where new vulnerabilities and exploits are constantly discovered.
– Furthermore, RBI offers a seamless user experience, allowing users to interact with web pages just as they would with a traditional browser. Whether submitting forms, watching videos, or accessing web applications, users can perform their desired actions without compromising security. From an IT perspective, RBI also simplifies security management, as it enables centralized control and monitoring of browsing activity, making it easier to identify and address potential threats.
– As organizations increasingly adopt cloud-based infrastructure and embrace remote work, Remote Browser Isolation has emerged as a critical security solution. By isolating web browsing activity, businesses can protect their sensitive data, intellectual property, and customer information from cyber threats. RBI significantly reduces the risk of successful attacks, enhances overall security posture, and provides peace of mind to organizations and individuals.
What within the perimeter makes us assume it can no longer be trusted?
Security becomes less and less tenable once there are many categories of users, device types, and locations. Users are diverse, so it is impossible, for example, to slot all vendors into one user segment with uniform permissions.
As a result, access to applications should be based on contextual parameters such as who and where the user is. Sessions should be continuously assessed to ensure they’re legit.
We need to find ways to decouple security from the physical network and, more importantly, application access from the network. In short, we need a new approach to providing access to the cloud, network, and device-agnostic applications. This is where Software-Defined Perimeter (SDP) comes into the picture.
What is a Software-Defined Perimeter (SDP)?
SDP VPN complements zero trust, which considers internal and external networks and actors untrusted. The network topology is divorced from the trust. There is no concept of inside or outside of the network.
This may result in users not automatically being granted broad access to resources simply because they are inside the perimeter. Security pros must primarily focus on solutions that allow them to set and enforce discrete access policies and protections for those requesting to use an application.
SDP lays the foundation and secures the access architecture, which enables an authenticated and trusted connection between the entity and the application. Unlike security based solely on IP, SDP does not grant access to network resources based on a user’s location.
Access policies are based on device, location, state, associated user information, and other contextual elements. Applications are considered abstract, so whether they run on-premise or in the cloud is irrelevant to the security policy.
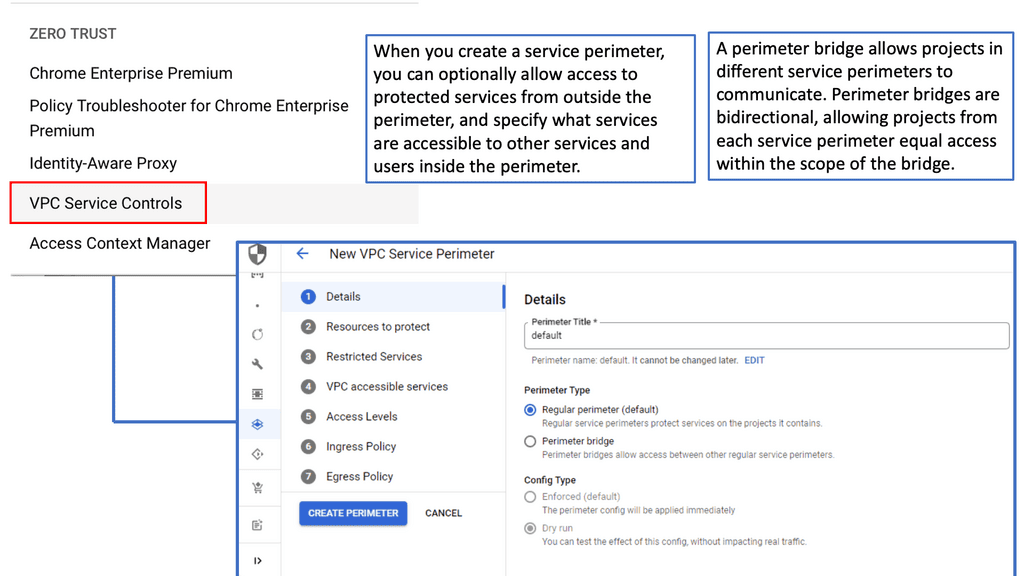
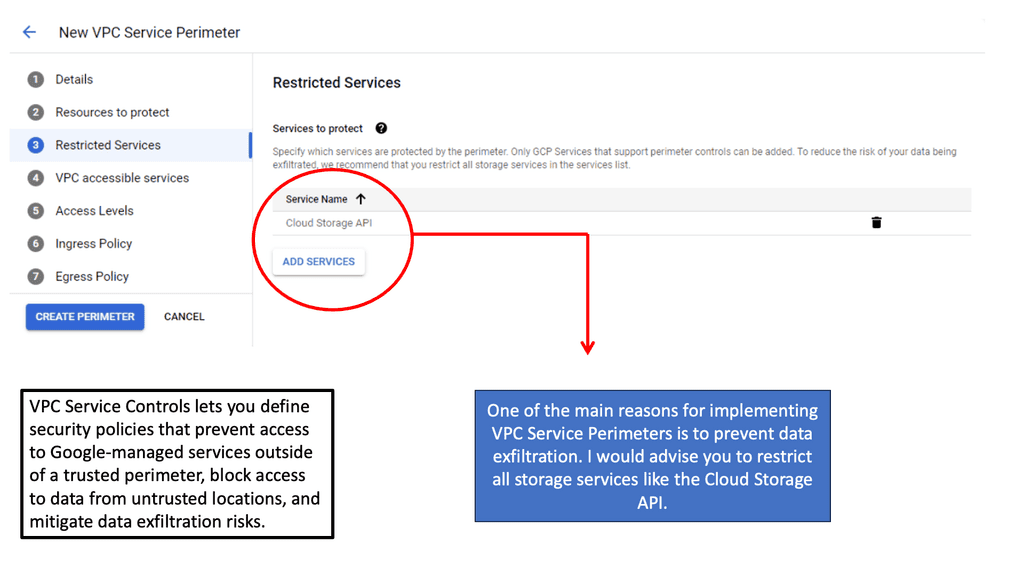
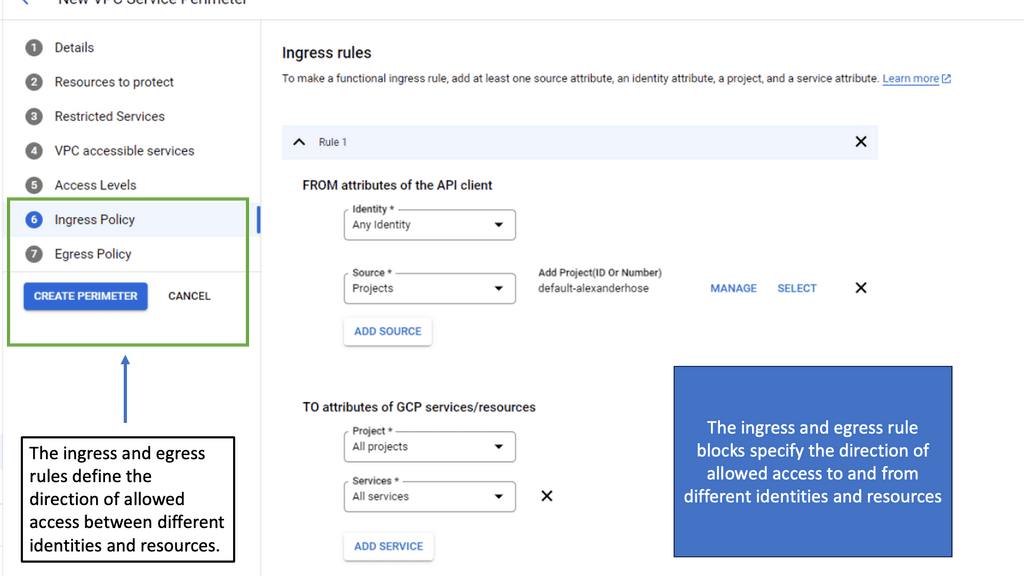
Example Technology: VPC Service Controls
Periodic Security Checking
Clients and their interactions are periodically checked to comply with the security policy. Periodic security checking protects against additional actions or requests not allowed while the connection is open. For example, let’s say you have a connection open to a financial application, and users access the recording software to record the session.
In this case, the SDP management platform can check whether the software has been started. If so, it employs protective mechanisms to ensure smooth and secure operation.
Microsegmentation
Front-end authentication and periodic checking are one part of the picture. However, we need to go a layer deeper to secure the application’s front door and the numerous doors within, which can potentially create additional access paths. Primarily, this is the job of microsegmentation. Microsegmentation can be performed at all layers of the OSI Model.
It’s not sufficient to provide network access. We must enable granular application access for dynamic segments of 1. In this scenario, a microsegment is created for every request. Microsegmentation creates the minimal accessible network required to complete specific tasks smoothly and securely. This is accomplished by subdividing more extensive networks into small, secure, and flexible micro-perimeters.
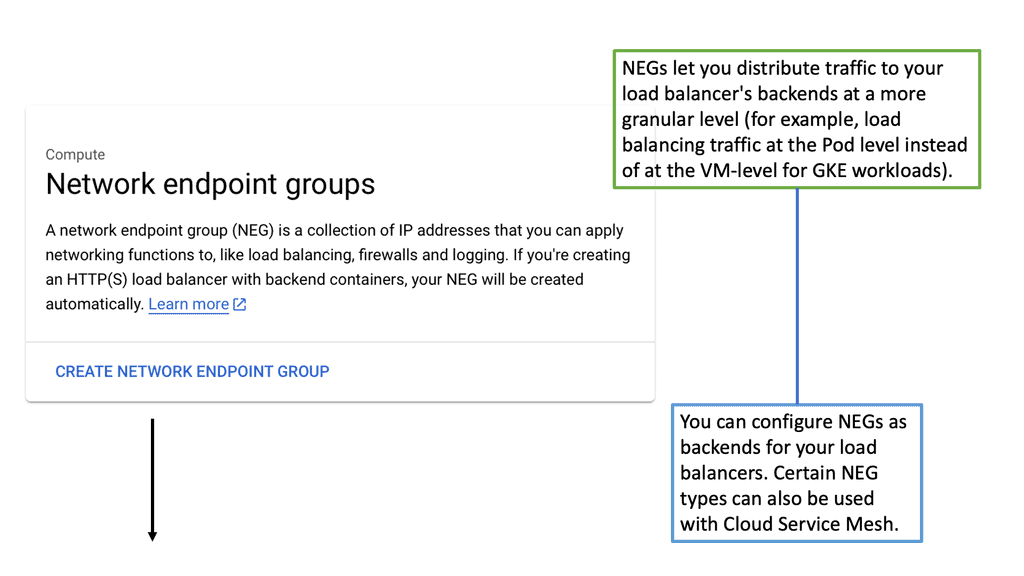
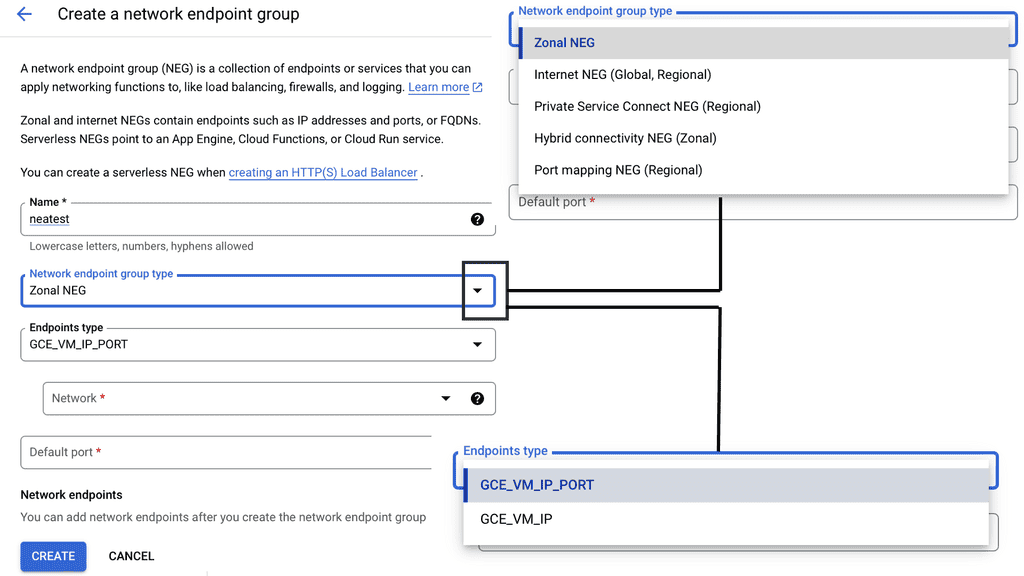
Example Technology: Network Endpoint Groups (NEGs)
Deep Dive Remote Browser Isolation (RBI)
SDP provides mechanisms to prevent lateral movement once users are inside the network. However, we must also address how external resources on the internet and public clouds can be accessed while protecting end-users, their devices, and the networks they connect. This is where remote browser isolation (RBI) and technologies such as Single Packet Authorization come into the picture.
What is Remote Browser Isolation? We started with browser isolation, which protects the user from external sessions by isolating the interaction. Essentially, it generates complete browsers within a virtual machine on the endpoint, providing a proactive approach to isolating users’ sessions from, for example, malicious websites, emails, and links. However, these solutions do not reliably isolate the web content from the end-user’s device on the network.
Remote browser isolation takes local browser isolation to the next level by enabling the rendering process to occur remotely from the user’s device in the cloud. Because only a clean data stream touches the endpoint, users can securely access untrusted websites from within the perimeter of the protected area.
**SDP, along with Remote Browser Isolation (RBI)**
Remote browser isolation complements the SDP approach in many essential ways. When you access a corporate asset, you operate within the SDP. But when you need to access external assets, RBI is required to keep you safe.
Zero trust and SDP are about authentication, authorization, and accounting (AAA) for internal resources, but secure ways must exist to access external resources. For this, RBI secures browsing elsewhere on your behalf.
No SDP solution can be complete without including rules to secure external connectivity. RBI takes zero trust to the next level by ensuring the internet browsing perspective. If access is to an internal corporate asset, we create a dynamic tunnel of one individualized connection. For external access, RBI transfers information without full, risky connectivity.
This is particularly crucial when it comes to email attacks like phishing. Malicious actors use social engineering tactics to convince recipients to trust them enough to click on embedded links.
Quality RBI solutions protect users by “knowing” when to allow user access while preventing malware from entering endpoints, entirely blocking malicious sites, or protecting users from entering confidential credentials by enabling read-only access.
The RBI Components
To understand how RBI works, let’s look under the hood of Ericom Shield. With RBI, for every tab a user opens on their device, the solution spins up a virtual browser in its dedicated Linux container in a remote cloud location. For additional information on containers, in particular Docker Container Security.
For example, if the user is actively browsing 19 open tabs on his Chrome browser, each will have a corresponding browser in its remote container. This sounds like it takes a lot of computing power, but enterprise-class RBI solutions do a lot of optimizations to ensure that it is not eating up too much of the endpoint resources.
If a tab is unused for some time, the associated container is automatically terminated and destroyed. This frees up computing resources and also eliminates the possibility of persistence.
As a result, whatever malware may have resided on the external site being browsed is destroyed and cannot accidentally infect the endpoint, server, or cloud location. When the user shifts back to the tab, he is reconnected in a fraction of a second to the exact location but with a new container, creating a secure enclave for internet browsing.
Website rendering
Website rendering is carried out in real-time from the remote browser. The web page is translated into a media stream, which then gets streamed back to the end-user via HTML5 protocol. In reality, the browsing experience is made up of images. When you look at the source code on the endpoint browser, you will find that the HTML code consists solely of a block of Ericom-generated code. This block manages to send and receive images via the media stream.
Whether the user is accessing the Wall Street Journal or YouTube, they will always get the same source code from Ericom Shield. This is ample proof that no local download, drive-by download, or any other contact that may try to hook up into your endpoint will ever get there, as it does not come into contact with the endpoint. It runs only remotely in a container outside the local LAN. The browser farm does all the heavy — and dangerous — lifting via container-bound browsers that read and execute the user’s uniform resource locator (URL) requests.
**Closing Points: Remote Browser Isolation**
SDP vendors have figured out device user authentication and how to secure sessions continuously. However, vendors are now looking for a way to ensure the tunnel through to external resource access.
If you use your desktop to access a cloud application, your session can be hacked or compromised. But with RBI, you can maintain one-to-one secure tunneling. With a dedicated container for each specific app, you are assured of an end-to-end zero-trust environment.
RBI, based on hardened containers and with a rigorous process to eliminate malware through limited persistence, forms a critical component of the SDP story. Its power is that it stops known and unknown threats, making it a natural evolution from the zero-trust perspective.
In conclusion, remote browser isolation is crucial to enhancing security in the digital era. By isolating web browsing activity from the user’s device, RBI provides an effective defense against a wide range of cyber threats. With its ability to protect against known and unknown threats, RBI offers a proactive approach to cybersecurity, ensuring that organizations and individuals can safely navigate the digital landscape. Remote Browser Isolation will remain vital to a comprehensive security strategy as the threat landscape evolves.
Summary: Remote Browser Isolation
In today’s digital landscape, where cyber threats loom large, ensuring robust web security has become a paramount concern for individuals and organizations. One innovative solution that has gained significant attention is remote browser isolation. In this blog post, we explored the concept of remote browser isolation, its benefits, and its potential to revolutionize web security.
Understanding Remote Browser Isolation
Remote browser isolation is a cutting-edge technology that separates the web browsing activity from the local device, creating a secure environment for users to access the internet. By executing web browsing sessions in isolated containers, any potential threats or malicious code are contained within the remote environment, preventing them from reaching the user’s device.
Enhancing Protection Against Web-Based Attacks
One key advantage of remote browser isolation is its ability to protect users against web-based attacks, such as drive-by downloads, malvertising, and phishing attempts. By isolating the browsing session in a remote environment, even if a user unknowingly encounters a malicious website or clicks on a harmful link, the threat is confined to the isolated container, shielding the user’s device and network from harm.
Mitigating Zero-Day Vulnerabilities
Zero-day vulnerabilities pose a significant challenge to traditional web security measures. These vulnerabilities refer to software flaws that cybercriminals exploit before a patch or fix is available. The risk of zero-day exploits can be significantly mitigated with remote browser isolation. Since the browsing session occurs in an isolated environment, even if a website contains an unknown or unpatched vulnerability, it remains isolated from the user’s device, rendering the attack ineffective.
Streamlining BYOD Policies
Bring Your Device (BYOD) policies have become prevalent in many organizations, allowing employees to use their devices for work. However, this brings inherent security risks, as personal devices may lack robust security measures. By implementing remote browser isolation, organizations can ensure that employees can securely access web-based applications and content without compromising the security of their devices or the corporate network.
Conclusion:
Remote browser isolation holds immense potential to strengthen web security by providing an innovative approach to protecting users against web-based threats. By isolating browsing sessions in secure containers, it mitigates the risks associated with malicious websites, zero-day vulnerabilities, and potential exploits. As the digital landscape continues to evolve, remote browser isolation emerges as a powerful solution to safeguard our online experiences and protect against ever-evolving cyber threats.
- DMVPN - May 20, 2023
- Computer Networking: Building a Strong Foundation for Success - April 7, 2023
- eBOOK – SASE Capabilities - April 6, 2023