Virtual Firewalls
In cybersecurity, firewalls protect networks from unauthorized access and potential threats. Traditional firewalls have long been employed to safeguard organizations' digital assets. However, with the rise of virtualization technology, virtual firewalls have emerged as a powerful solution to meet the evolving security needs of the modern era. This blog post will delve into virtual firewalls, exploring their advantages and why they should be considered an integral part of any comprehensive cybersecurity strategy.
Virtual firewalls, or software firewalls, are software-based security solutions operating within a virtualized environment. Unlike traditional hardware firewalls, which are physical devices, virtual firewalls are implemented and managed at the software level. They are designed to protect virtual machines (VMs) and virtual networks by monitoring and controlling incoming and outgoing network traffic.
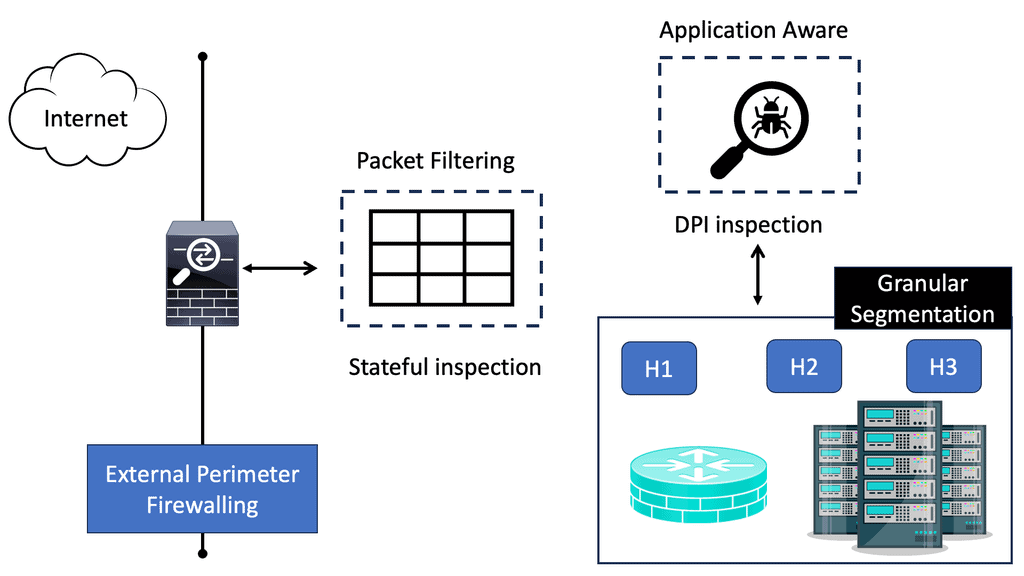
Virtual firewalls, also known as software firewalls, are security solutions designed to monitor and control network traffic within virtualized environments. Unlike traditional hardware firewalls, which operate at the network perimeter, virtual firewalls are deployed directly on virtual machines or within hypervisors. This positioning enables them to provide granular security policies and protect the internal network from threats that may originate within virtualized environments.
Segmentation: Virtual firewalls facilitate network segmentation by isolating virtual machines or groups of VMs, preventing lateral movement of threats within the virtual environment.
Intrusion Detection and Prevention: By analyzing network traffic, virtual firewalls can detect and prevent potential intrusions, helping organizations proactively defend against cyber threats.
Application Visibility and Control: With deep packet inspection capabilities, virtual firewalls provide organizations with comprehensive visibility into application-layer traffic, allowing them to enforce fine-grained policies and mitigate risks.
Enhanced Security: Virtual firewalls strengthen the overall security posture by augmenting traditional perimeter defenses, ensuring comprehensive protection within the virtualized environment.
Scalability and Flexibility: Virtual firewalls are highly scalable, allowing organizations to easily expand their virtual infrastructure while maintaining robust security measures. Additionally, they offer flexibility in terms of deployment options and configuration.
Centralized Management: Virtual firewalls can be managed centrally, simplifying administration and enabling consistent security policies across the virtualized environment.
Performance Impact: Virtual firewalls introduce additional processing overhead, which may impact network performance. It is essential to evaluate the performance implications and choose a solution that meets both security and performance requirements.
Integration with Existing Infrastructure: Organizations should assess the compatibility and integration capabilities of virtual firewalls with their existing virtualization platforms and network infrastructure.
Virtual firewalls have become indispensable tools in the fight against cyber threats, providing organizations with a robust layer of protection within virtualized environments. By leveraging their advanced features, such as segmentation, intrusion detection, and application control, businesses can fortify their digital fortresses and safeguard their critical assets. As the threat landscape continues to evolve, investing in virtual firewalls is a proactive step towards securing the future of your organization.
Matt Conran
Highlights: Virtual Firewalls
Background: Virtual Firewalls
– The virtual firewall (VF) is a network firewall appliance that runs within a virtualized environment and provides packet filtering and monitoring functions similar to those of a physical firewall. You can implement a VF on an existing guest virtual machine, as a traditional software firewall, as a virtual security appliance, as a virtual switch with enhanced security capabilities, or as a kernel process within the host hypervisor.
– A virtual firewall provides packet filtering and monitoring in a virtualized environment, even as another virtual machine, but also within the hypervisor. A guest VM running within a virtualized environment can be installed with VF as a traditional software firewall, a virtual security appliance designed to protect virtual networks, a virtual switch with additional security capabilities, or a kernel process that runs on top of all VM activity within the host hypervisor.
– There is a trend in virtual firewall technology to combine security-capable virtual switches with virtual security appliances. Virtual firewalls can incorporate additional networking features like VPN, QoS, and URL filtering.
Note: Types of Virtual Firewalls
a) Host-based Virtual Firewalls: Host-based virtual firewalls are installed on individual virtual machines (VMs) or servers. They monitor and control network traffic at the host level, providing added security for each VM.
b) Network-based Virtual Firewalls: Network-based virtual firewalls are deployed at the network perimeter, allowing for centralized monitoring and control of inbound and outbound traffic. They are instrumental in cloud environments where multiple VMs are running.
Integration with Virtualization Platforms:
Virtual firewalls seamlessly integrate with popular virtualization platforms such as VMware and Hyper-V. This integration enables centralized management, simplifying the configuration and monitoring of virtual firewalls across your virtualized infrastructure. Additionally, virtual firewalls can leverage the dynamic capabilities of virtualization platforms, adapting to changes in the virtual environment automatically.
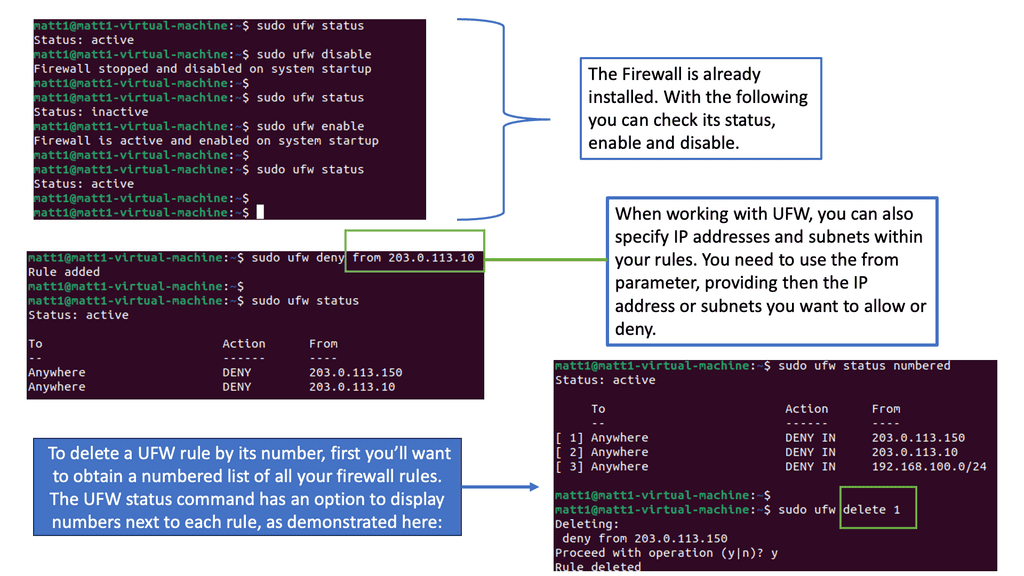
Example Technology: Linux Firewalling
Understanding UFW Firewall
To begin our journey, let’s first understand a UFW firewall. UFW, short for Uncomplicated Firewall, is a user-friendly interface that simplifies managing netfilter firewall rules. It is built upon the robust iptables framework and provides an intuitive command-line interface for configuring firewall rules.
UFW firewall offers many features that contribute to a secure network environment. From simple rule management to support for IPv4 and IPv6 protocols, UFW ensures your network is protected against unauthorized access. It also provides flexible configuration options, allowing you to define rules based on ports, IP addresses, and more.
Implementing Virtual Firewalls:
Assessing Network Requirements: Before implementing virtual firewalls, it’s crucial to assess your network environment, identify potential vulnerabilities, and determine the specific security needs of your organization. This comprehensive assessment enables you to tailor your virtual firewall deployment to address specific threats and risks effectively.
Choosing the Right Virtual Firewall Solution: There are various virtual firewall solutions available in the market, each with its own set of features and capabilities. It’s essential to evaluate your organization’s requirements, such as throughput, performance, and integration with existing security infrastructure. This evaluation will help you select the most suitable virtual firewall solution for your network.
Configuring Security Policies: Once you have selected a virtual firewall solution, the next step is to configure security policies. This involves defining access control rules, setting up intrusion detection and prevention systems, and configuring virtual private networks (VPNs) if necessary. It’s crucial to align these policies with your organization’s security objectives and industry best practices.
Advantages of Virtual Firewalls:
1. Enhanced Flexibility: Virtual firewalls offer greater flexibility than their hardware counterparts. They are software-based and can be easily deployed, scaled, and managed in virtualized environments without additional hardware. This flexibility enables organizations to adapt to changing business requirements more effectively.
2. Cost-Effectiveness: Virtual firewalls eliminate the need to purchase and maintain physical hardware devices. Organizations can significantly reduce their capital and operational expenses by leveraging existing virtualization infrastructure. This cost-effectiveness makes virtual firewalls an attractive option for businesses of all sizes.
3. Centralized Management: Virtual firewalls can be centrally managed through a unified interface, providing administrators with a consolidated view of the entire virtualized network. This centralized management simplifies the configuration, monitoring, and enforcement of security policies across multiple virtual machines and networks, saving time and effort.
4. Segmentation and Isolation: Virtual firewalls enable organizations to segment their virtual networks into different security zones, isolating sensitive data and applications from potential threats. This segmentation ensures that the rest of the network remains protected even if one segment is compromised. By enforcing granular access control policies, virtual firewalls add a layer of security to prevent lateral movement within the virtualized environment.
5. Scalability: Virtual firewalls are software-based and can be easily scaled up or down to accommodate changing network demands. This scalability allows organizations to expand their virtual infrastructure without investing in additional physical hardware. With virtual firewalls, businesses can ensure that their security solutions grow with their evolving needs.
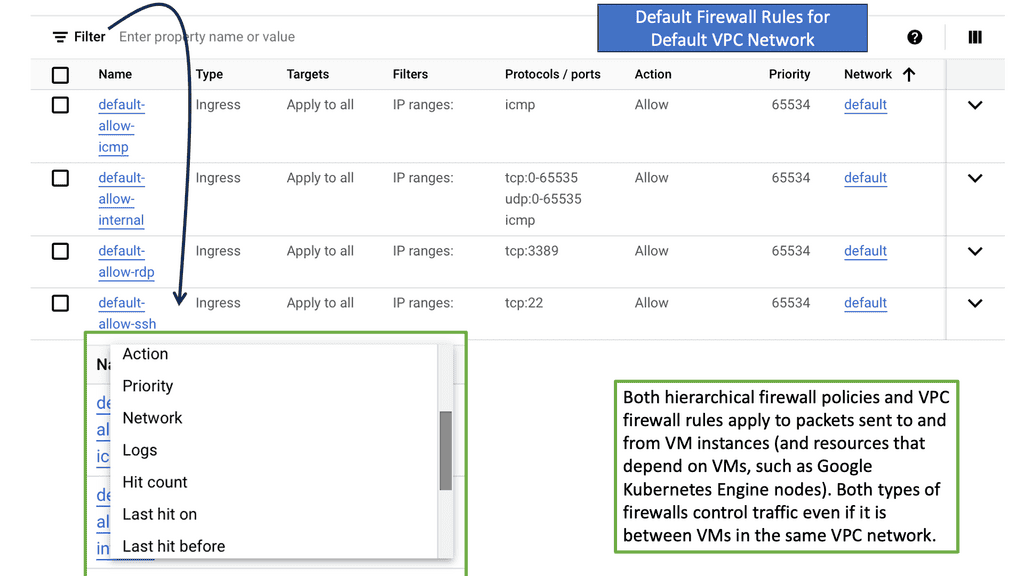
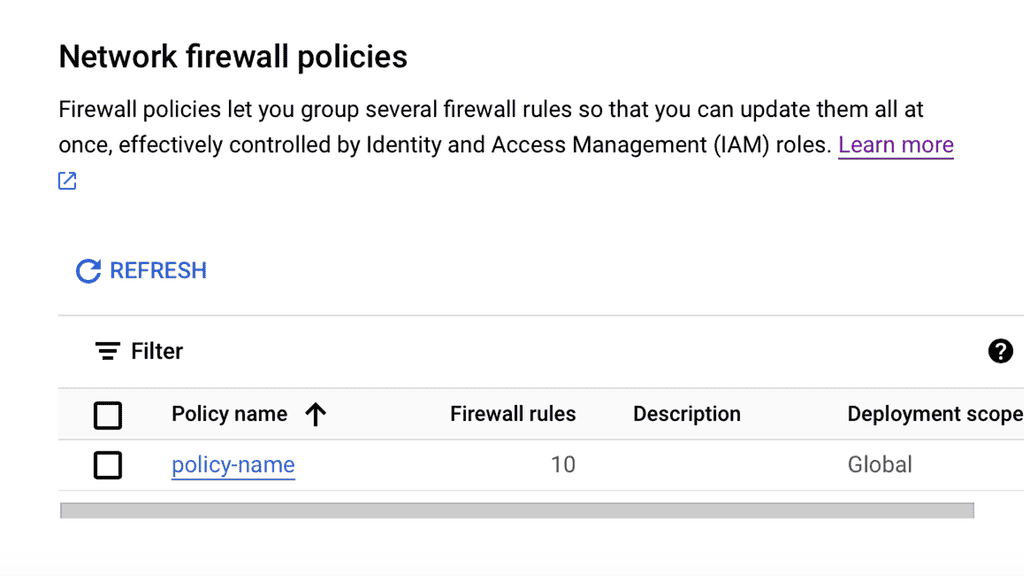
Example Default Firewall Rules in VPC Network
### What Are Default Firewall Rules?
When you create a new VPC network, it typically comes with a set of default firewall rules. These rules are designed to allow basic network functionality and to provide a base layer of security for your network. Understanding these default rules is crucial for managing your network’s security posture effectively.
### The Role of Ingress and Egress Rules
Default firewall rules usually include both ingress (incoming) and egress (outgoing) rules. Ingress rules determine what traffic can enter your VPC, while egress rules control the traffic leaving your VPC. Typically, default rules allow all egress traffic, enabling your resources to communicate with external networks, but restrict ingress traffic to ensure that only authorized connections can be established.
### Customizing Default Rules
While default rules provide a starting point, they may not fit the specific needs of your application or organization. It’s essential to review and customize these rules based on your security policies and compliance requirements. This involves defining more specific rules that allow or deny traffic based on various parameters such as IP address ranges, protocols, and ports.
### Best Practices for Managing Firewall Rules
To maintain a secure and efficient VPC network, follow best practices when managing firewall rules. Regularly review and audit your rules to ensure they align with your security policies. Document changes and maintain a clear understanding of the purpose of each rule. Additionally, consider implementing a least privilege approach, where only necessary traffic is permitted, minimizing the potential attack surface.
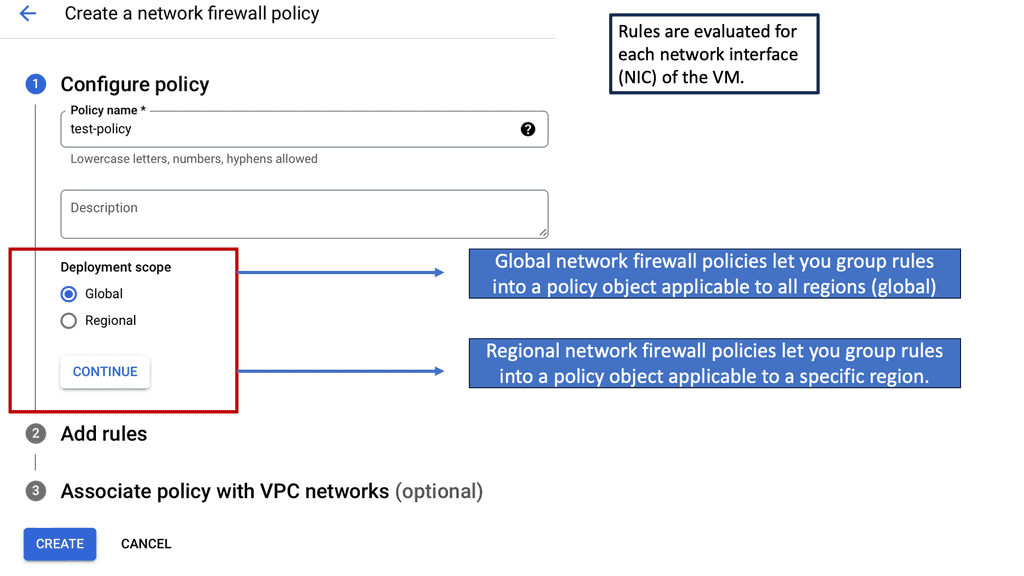
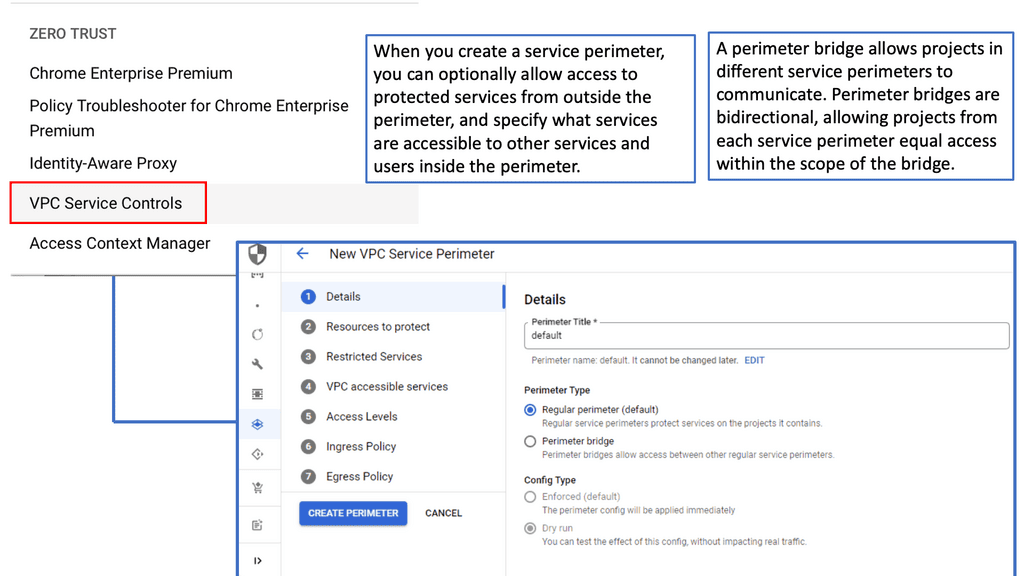
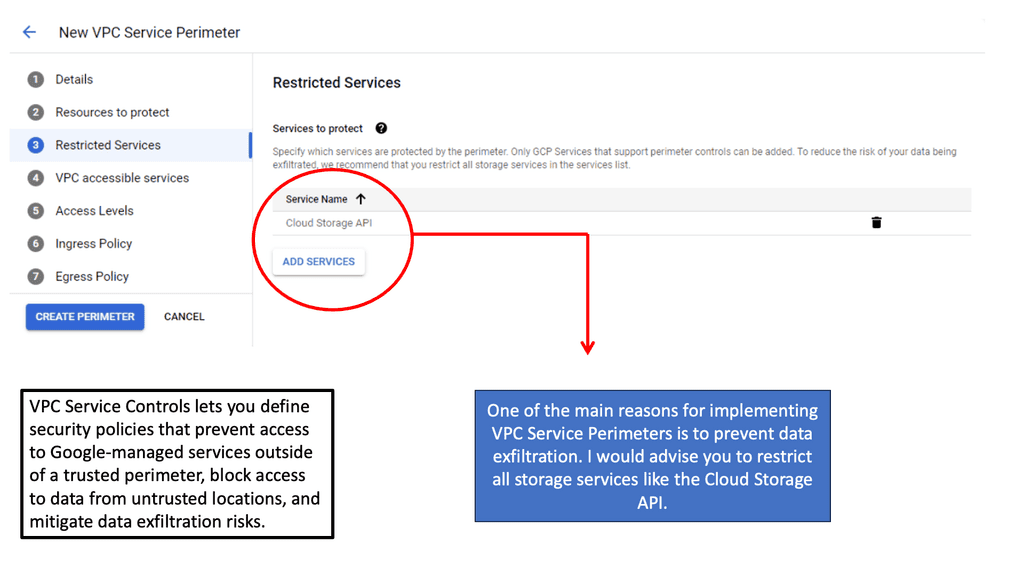
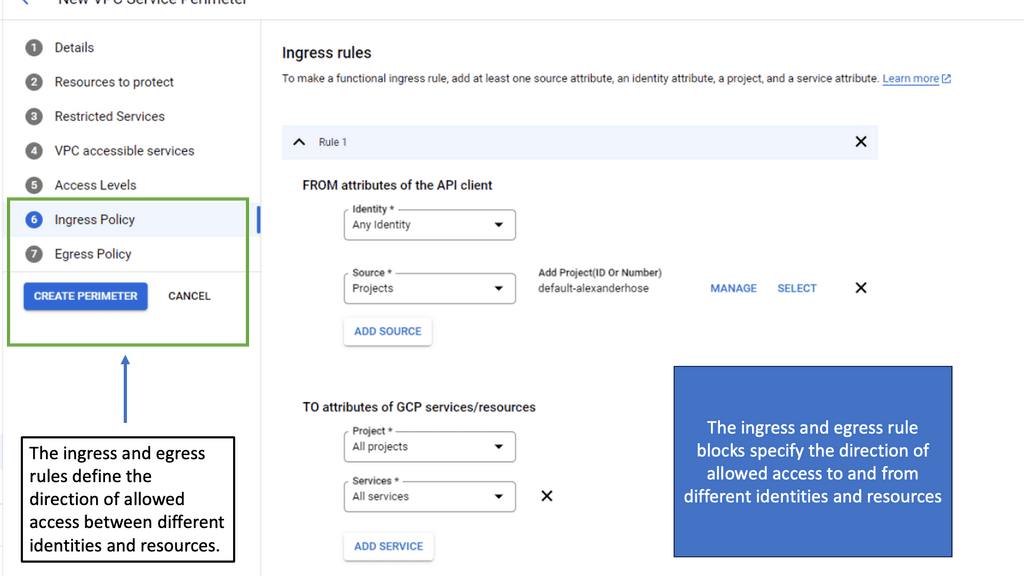
VPC Service Controls
**Understanding the Basics**
VPC Service Controls provide an additional layer of security by enabling organizations to set up a virtual perimeter that restricts data access and movement. By configuring service perimeters, businesses can enforce security policies that prevent data exfiltration and unauthorized access. This is particularly beneficial for organizations handling sensitive information, such as financial data or personal customer information, as it helps maintain compliance with stringent data protection regulations.
**Implementing VPC Service Controls**
Implementing VPC Service Controls involves creating service perimeters around the resources you want to protect. These perimeters act like a security fence, allowing only authorized access to the data within. To get started, identify the resources you want to include and configure policies that define who and what can access these resources. Google Cloud’s intuitive interface makes it easy to set up and manage these perimeters, ensuring that your cloud environment remains secure without compromising performance.
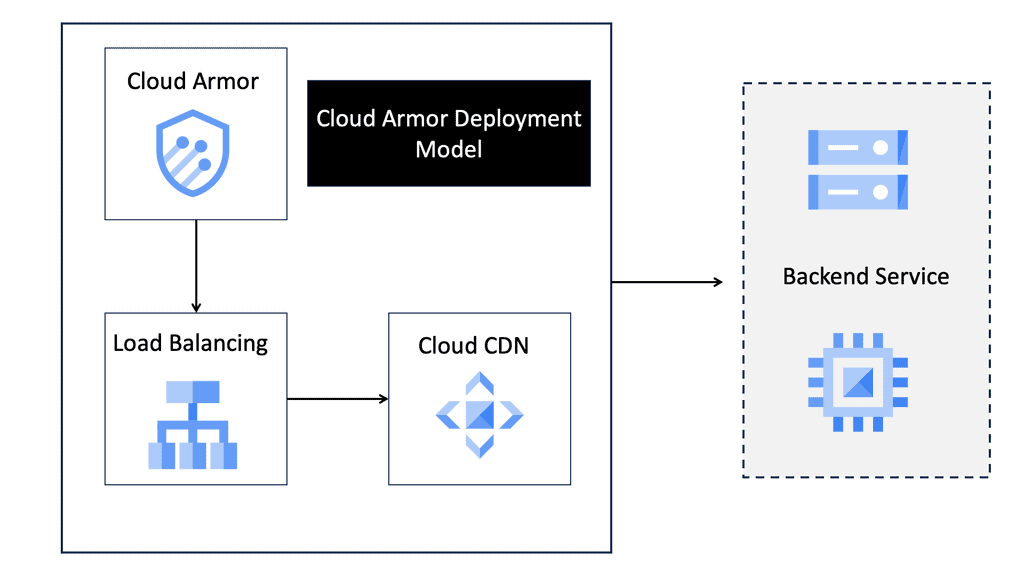
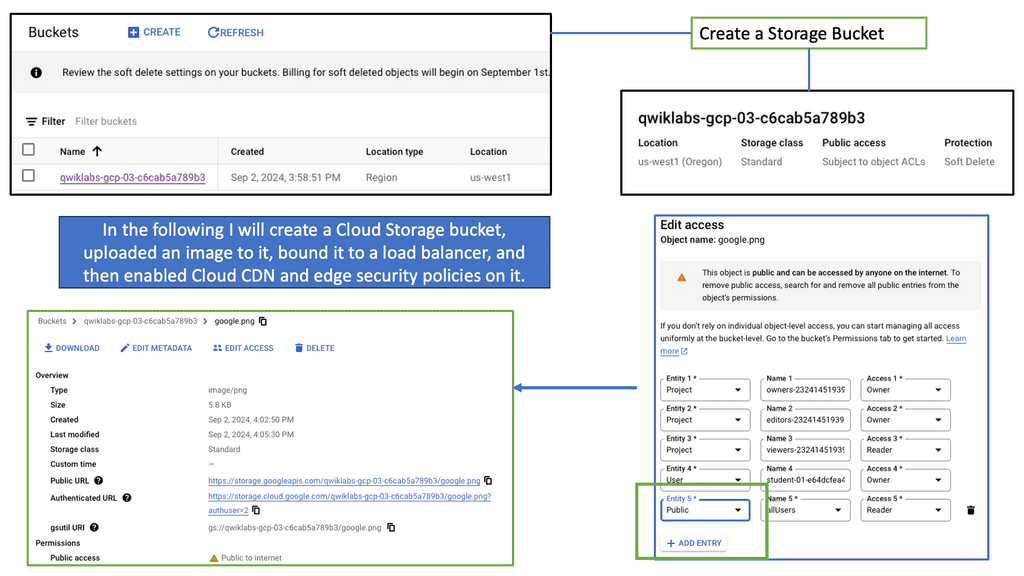
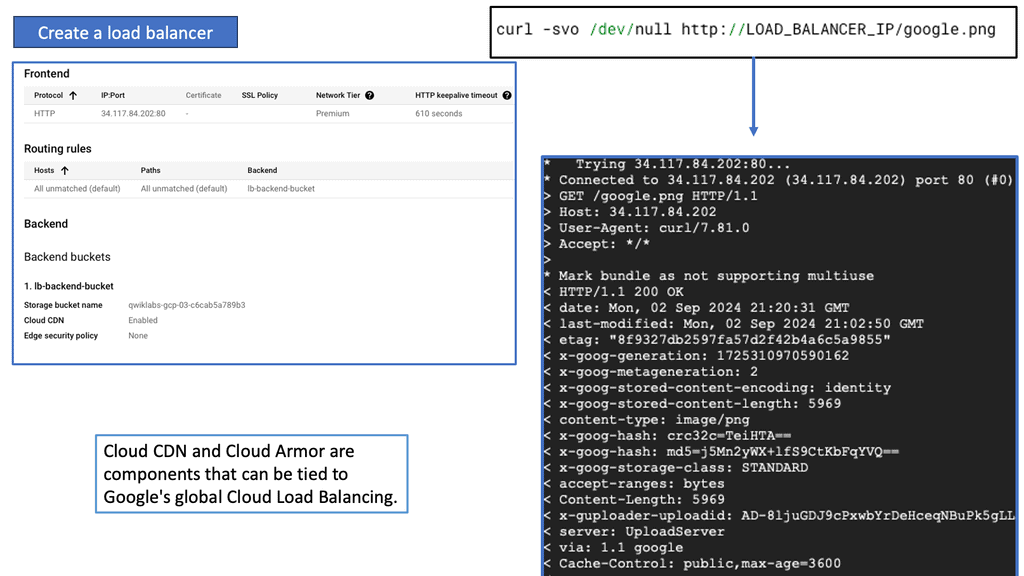
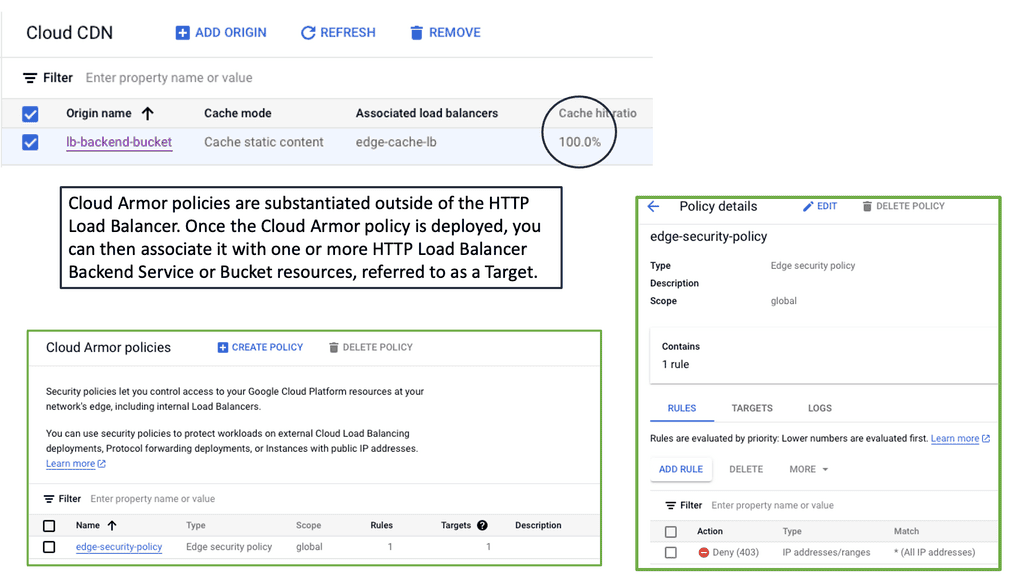
Virtual Firewall with Cloud Armor
**What is Cloud Armor?**
Cloud Armor is a security service that offers advanced protection for your applications hosted on the cloud. It provides a robust shield against various cyber threats, including DDoS attacks, SQL injections, and cross-site scripting. By leveraging Google’s global infrastructure, Cloud Armor ensures that your applications remain secure and available, even during the most sophisticated attacks.
**Key Features of Cloud Armor**
One of the standout features of Cloud Armor is its ability to create and enforce edge security policies. These policies allow you to control and monitor traffic to your applications, ensuring that only legitimate users gain access. Additionally, Cloud Armor provides real-time monitoring and alerts, enabling you to respond swiftly to potential threats. With its customizable rules and rate limiting capabilities, you can fine-tune your security settings to meet your specific needs.
**Edge Security Policies: Your First Line of Defense**
Edge security policies are a critical component of Cloud Armor. These policies act as your first line of defense, filtering out malicious traffic before it reaches your applications. By defining rules based on IP addresses, geographic locations, and other criteria, you can block unwanted traffic and reduce the risk of attacks. Moreover, edge security policies help in mitigating DDoS attacks by distributing traffic across multiple regions, ensuring your applications remain accessible.
**Benefits of Using Cloud Armor**
Implementing Cloud Armor offers numerous benefits. Firstly, it enhances the security of your applications, protecting them from a wide range of cyber threats. Secondly, it ensures high availability, even during large-scale attacks, by distributing traffic and preventing overload. Thirdly, Cloud Armor’s real-time monitoring and alerts enable proactive threat management, allowing you to respond quickly to potential issues. Lastly, its customizable policies provide flexibility, ensuring your security settings align with your specific requirements.
**Range of attack vectors**
On-campus networks, mobile devices, and laptops are highly vulnerable to malware and ransomware, as well as to phishing, smishing, malicious websites, and infected applications. Thus, a solid network security design is essential to protect endpoints from such security threats and enforce endpoint network access control. End users can validate their identities before granting access to the network to determine who and what they can access.
Virtual firewalls, also known as cloud firewalls or virtualized NGFWs, grant or deny network access between untrusted zones. They provide inline network security and threat prevention in cloud-based environments, allowing security teams to gain visibility and control over cloud traffic. In addition to being highly scalable, virtual network firewalls are ideal for protecting virtualized environments because they are deployed in a virtualized form factor.
Because Layer 4 firewalls cannot detect attacks at the application layer, virtual firewalls are ideal for cloud service providers (CSPs). Virtual firewalls can determine if requests are allowed based on their content by examining applications and not just port numbers. This feature can prevent DDoS attacks, HTTP floods, SQL injections, cross-site scripting attacks, parameter tampering attacks, and Slowloris attacks.
**Network Security Components**
This post discusses the network security components of virtual firewalls and the virtual firewall appliance that enables a zero-trust network design. In the Secure Access Service Edge (SASE ) world, virtual firewalling or any virtual device brings many advantages, such as having a stateful inspection firewall closer to the user sessions. Depending on the firewall design, the inspection and filtering are closer to the user’s sessions or workloads. Firstly, Let us start with the basics of IP networks and their operations.
**Virtual SDN Data Centers**
In a virtual data center design, IP networks deliver various services to consumers and businesses. As a result, they heavily rely on network availability for business continuity and productivity. As the reliance on IP networks grows, so does the threat and exposure to network-based attacks. New technologies and mechanisms address new requirements but also come with the risk of new threats. It’s a constant cat-and-mouse game. It’s your job as network admins to ensure the IP network and related services remain available.
For additional pre-information, you may find the following post helpful:
Virtual Firewalls
The term “firewall” refers to a device or service that allows some traffic but denies other traffic. Positioning a firewall at a network gateway point in the network infrastructure is an aspect of secure design. A firewall so set at strategic points in the network intercepts and verifies all traffic crossing that gateway point. Some other places that firewalls are often deployed include in front of (i.e., on the public Internet side), behind (inside the data center), or in load-balancing systems.
Traffic Types and Virtual Firewalls
Firstly, a thorough understanding of the traffic types that enter and leave the network is critical. Network devices process some packets differently from others, resulting in different security implications. Transit IP packets, receive-adjacency IP packets, exception, and non-IP packets are all handled differently.
You also need to keep track of the plethora of security attacks, such as resource exhaustion attacks (direct attacks, transit attacks, reflection attacks), spoofing attacks, transport protocol attacks (UDP & TCP), and routing protocol/control plane attacks.
Various attacks target Layer 2, including MAC spoofing, STP, and CAM table overflow. Overlay virtual networking introduces two control planes, both of which require protection.
The introduction of cloud and workload mobility is changing the network landscape and security paradigm. Workload fluidity and the movement of network states are putting pressure on traditional physical security devices. It isn’t easy to move physical appliances around the network. Physical devices cannot follow workloads, which drives the world of virtual firewalls with distributed firewalls, NIC-based Firewalls, Microsegmentation, and Firewall VM-based appliances.
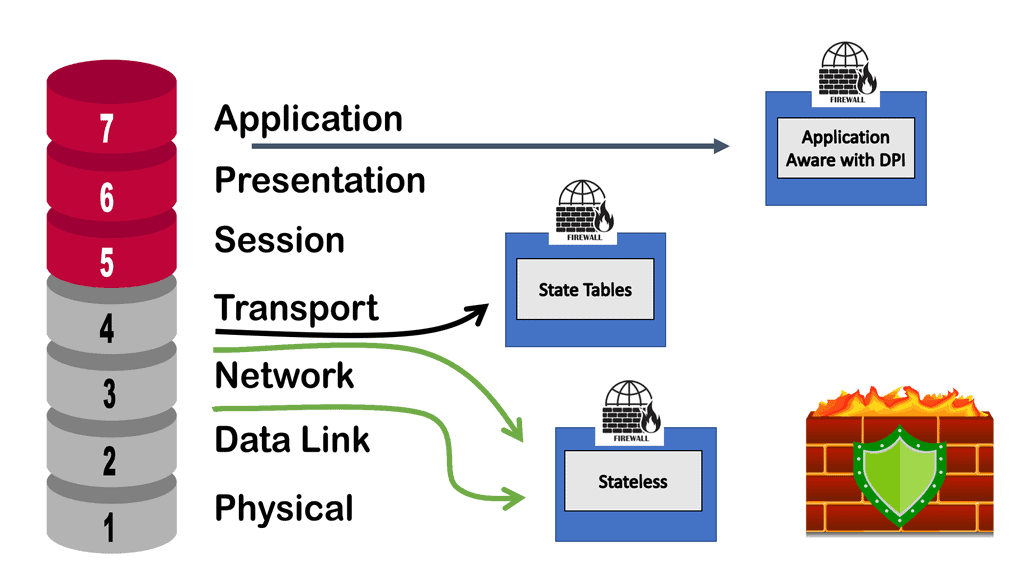
**Session state**
Simple packet filters match on Layer 2 to 4 headers – MAC, IP, TCP, and UDP port numbers. If they don’t match the TCP SYN flags, it’s impossible to identify established sessions. Tracking the state of the TCP SYN tells you if this is the first packet of a session or a subsequent packet of an existing session. Matching on TCP flags allows you to differentiate between TCP SYN, SYN-ACK, and ACK.
Matching established TCP sessions would match on packets with the ACK/RST/FIN bit set. All packets without a SYN flag will not start a new session, and all packets with ACK/RST/FIN can appear anywhere in the established session.
Checking these three flags indicates if the session is established or not. In any adequately implemented TCP stack, the packet filtering engine will not open a new session unless it receives a TCP packet with the SYN flag. In the past, we used a trick. If a packet arrives with a destination port over 1024, it must be a packet from an established session, as no services were running on a high number of ports.
The term firewall originally referred to a wall to confine a potential fire. Regarding networking, a firewalling device is a barrier between a trusted and untrusted network. It can be classed into several generations. First-generation firewalls are simple packet filters, the second-generation refers to stateful devices, and the third-generation refers to application-based firewalls. A stateful firewall doesn’t mean it can examine the application layer and determine users’ actions.
A- The starting points of packet filters
Firewalls initially started with packet filters at each end and an application proxy in the middle. The application proxy would inspect the application level, and the packet filters would perform essential scrubbing. All sessions terminate on the application proxy where new sessions are initiated. Second-generation devices came into play, and we started tracking the sessions’ state.
Now, we have a single device that can do the same job as the packet filter combined with the application proxy. But it wasn’t inspected at the application level. The devices were stateful and could track the session’s state but could not go deeper into the application. For example, examine the HTTP content and inspect what users are doing. Generation 2 was a step back in terms of security.
We then moved into generation 3, which marketing people call next-generation firewalls. They offer Layer 7 inspection with packet filtering. Finally, niche devices called Application-Level firewalls, also known as web application Firewalls (WAF), are usually only concerned with HTTP traffic. They have similar functionality to reverse web proxy, terminating the HTTP session.
B- The rise of virtual firewalls and virtual firewall appliances
Almost all physical firewalls offer virtual contexts. Virtual contexts divide the firewall and solve many multi-tenancy issues. They provide separate management plans, but all the contexts share the same code. They also run over the same interfaces competing for the same bandwidth, so if one tenant gets DoS attacked, the others might be affected. However, virtual contexts constitute a significant drawback because they are tied to the physical device, so unlike VM-based firewalls, you lose all the benefits of virtualization.
A firewall in a VM can run on any transport provided by the hypervisor. The VM thinks it has an ethernet interface, enabling you to put a VM-based firewall on top of any virtualization technology. The physical firewall must be integrated with the network virtualization solution, and many vendors have limited support for overlay networking solutions.
The physical interface supports VXLAN, but that doesn’t mean it can help the control plane in which the overlay network solution runs. For example, the network overlay solution might use IP multicast, OVSDB, or EVPN over VXLAN. Deploying Virtual firewalling offers underlay transport independence. It is flexible and easy to deploy and manage.
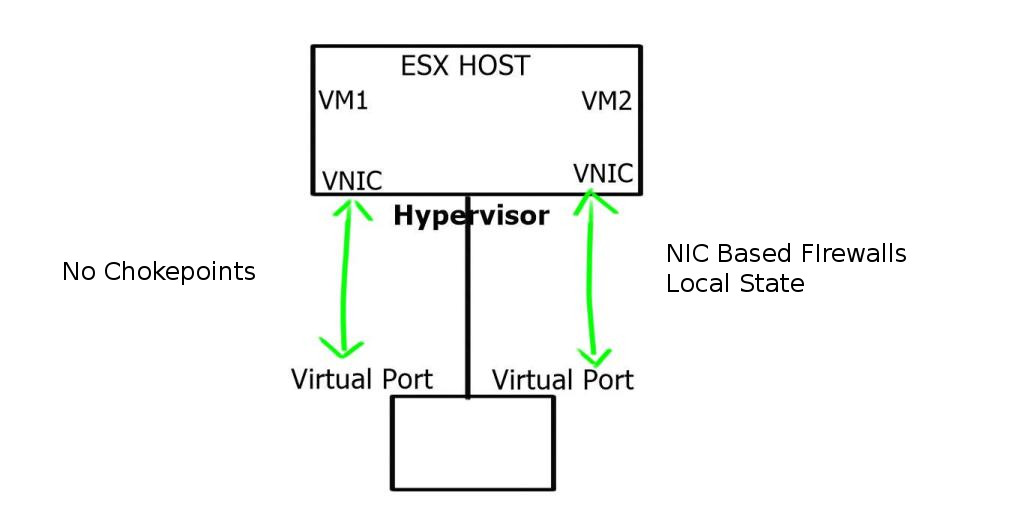
C- Virtual firewall appliance: VM and NIC-based firewalls
Traditionally, we used VLANs and IP subnets as security zones. This introduced problems with stretched VLANs, so they came with VXLAN and NVGRE. However, we are still using IP as the isolation mechanism. Generally, firewalls are implemented between subnets so all the traffic goes through the firewall, which can result in traffic trombones and network chokepoints.
The new world is all about VM and NIC-based firewalls. NIC-based firewalls are mostly packet filters or, at the very most, reflective ACLs. Vmware NSX distributed firewall does slightly more with some application-level functionality for SIP and FTP traffic.
NIC-based firewalls force you to redesign your security policy. Now, all the firewall rules are directly in front of the virtual NIC, offering optimal access to any traffic between VMs, as traffic does not need to go through a central firewall device. The session state is kept local and only specific to that VM. This makes them very scalable. It allows you to eliminate IP subnets as security zones and provides isolation between VMs in the same subnet.
This protects individual VMs by design, so all others are protected even if an attacker breaks into one VM. VMware calls this micro-segmentation in NSX. You can never fully replace physical firewalls with virtual firewalls. Performance and security audits come to mind. However, they can be used to augment each other. NIC is based on the east-to-west traffic and physical firewalls at the perimeter to filter north-to-south traffic.
Closing Points on Virtual Firewalls
Virtual firewalls, unlike their hardware counterparts, are software-based solutions that provide network security for virtualized environments. They operate within the cloud or on virtual machines, offering the flexibility to protect dynamic environments where traditional firewalls might fall short. With the rise of cloud computing, virtual firewalls have become indispensable, allowing organizations to enforce security policies consistently across their virtual infrastructures.
The advantages of virtual firewalls are numerous. Firstly, they offer scalability. As your business grows, so does your network, and virtual firewalls can expand seamlessly to accommodate this growth. Secondly, they are cost-effective. Without the need for physical hardware, virtual firewalls reduce both upfront costs and ongoing maintenance expenses. Additionally, they provide agility, enabling rapid deployment and configuration changes to adapt to evolving security needs. Finally, virtual firewalls enhance security by integrating with other security tools to provide a comprehensive defense strategy.
Deploying a virtual firewall requires careful planning to ensure it aligns with your organization’s specific needs. One common strategy is to implement them in a public cloud environment, where they can protect against threats targeting cloud-based applications and data. Another approach is using them within private cloud infrastructures to secure internal communications and sensitive data. Hybrid environments, which combine on-premises and cloud resources, can also benefit from virtual firewalls, allowing for a unified security policy across diverse platforms.
Effective management of virtual firewalls involves regular monitoring and updates. Keeping firewall software up-to-date ensures protection against the latest threats and vulnerabilities. Additionally, conducting regular security audits helps identify potential weaknesses in your network. Implementing a centralized management system can also streamline configuration and monitoring processes, making it easier to maintain a strong security posture. Educating your IT team about the latest trends and threats in cybersecurity further strengthens your defense strategy.
Summary: Virtual Firewalls
The need for robust network security has never been greater in today’s interconnected world. With the rise of cyber threats, organizations constantly seek advanced solutions to protect their sensitive data. One such powerful tool that has gained significant prominence is the virtual firewall. In this blog post, we will delve into virtual firewalls, exploring their definition, functionality, benefits, and role in fortifying network security.
Understanding Virtual Firewalls
Virtual firewalls, also known as software firewalls, are security applications that provide network protection by monitoring and controlling incoming and outgoing network traffic. Unlike physical firewalls, which are hardware-based, virtual firewalls operate within virtualized environments, offering a flexible and scalable approach to network security.
How Virtual Firewalls Work
Virtual firewalls examine network packets and determine whether to allow or block traffic based on predefined rule sets. They analyze factors such as source and destination IP addresses, ports, and protocols to make informed decisions. With their deep packet inspection capabilities, virtual firewalls can identify and mitigate potential threats, including malware, hacking attempts, and unauthorized access.
Benefits of Virtual Firewalls
Enhanced Security: Virtual firewalls provide an additional layer of security, safeguarding the network from external and internal threats. By actively monitoring and filtering network traffic, they help prevent unauthorized access and mitigate potential vulnerabilities.
Cost-Effectiveness: As software-based solutions, virtual firewalls eliminate the need for physical appliances, thereby reducing hardware costs. They can be easily deployed and managed within virtualized environments, streamlining network security operations.
Scalability: Virtual firewalls offer scalability, allowing organizations to adapt their security infrastructure to meet evolving demands. By allowing organizations to add or remove virtual instances as needed, they provide flexibility in managing expanding networks and changing business requirements.
Best Practices for Implementing Virtual Firewalls
Define Clear Security Policies: Comprehensive security policies are crucial for effective virtual firewall implementation. Clearly define access rules, traffic filtering criteria, and acceptable use policies to ensure optimal protection.
Regular Updates and Patching: Stay updated with your virtual firewall’s latest security patches and firmware updates. Regularly monitoring and maintaining the firewall’s software ensures it is equipped with the latest threat intelligence and safeguards against emerging risks.
Monitoring and Log Analysis: Implement robust monitoring and log analysis tools to gain insights into network traffic patterns and potential security incidents. Proactive monitoring allows for prompt detection and response to any suspicious activity.
Conclusion
In conclusion, virtual firewalls have become indispensable tools in the arsenal of network security measures. Their ability to protect virtualized environments, provide scalability, and enhance overall security posture makes them a top choice for organizations seeking holistic network protection. By harnessing the power of virtual firewalls, businesses can fortify their networks, safeguard critical data, and stay one step ahead of cyber threats.
- DMVPN - May 20, 2023
- Computer Networking: Building a Strong Foundation for Success - April 7, 2023
- eBOOK – SASE Capabilities - April 6, 2023