DNS Reflection attack
In today's interconnected world, cyber threats continue to evolve, posing significant risks to individuals, organizations, and even nations. One such threat, the DNS Reflection Attack, has gained notoriety for its potential to disrupt online services and cause significant damage. In this blog post, we will delve into the intricacies of this attack, exploring its mechanics, impact, and how organizations can protect themselves from its devastating consequences.
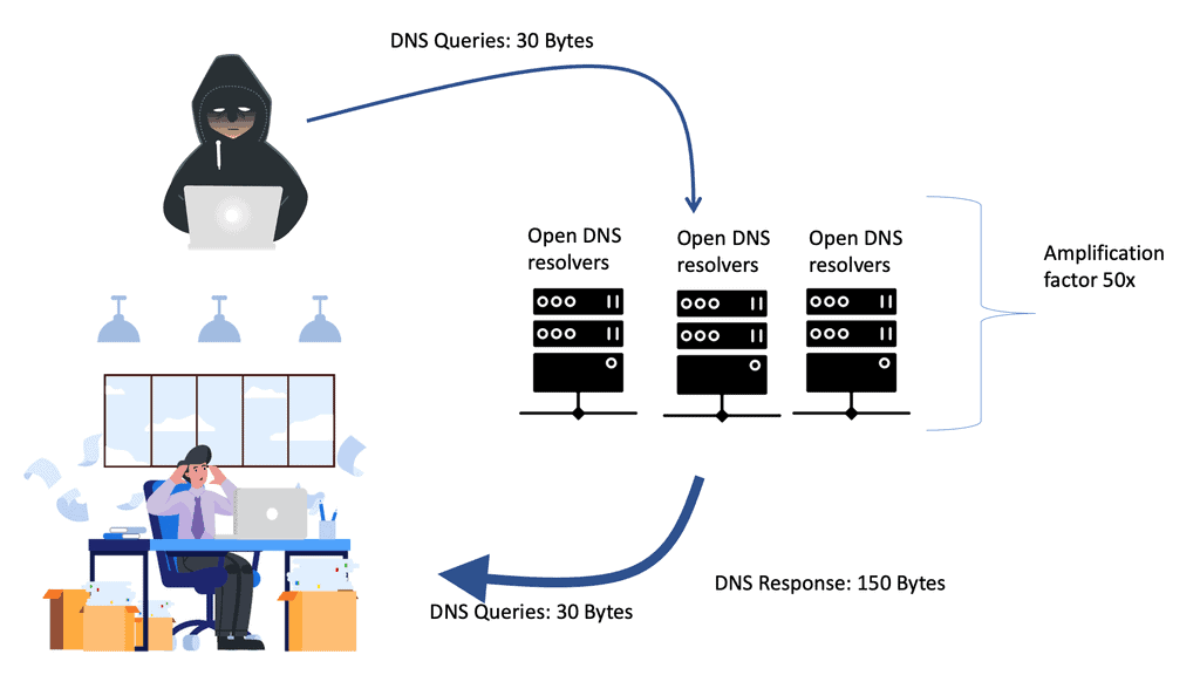
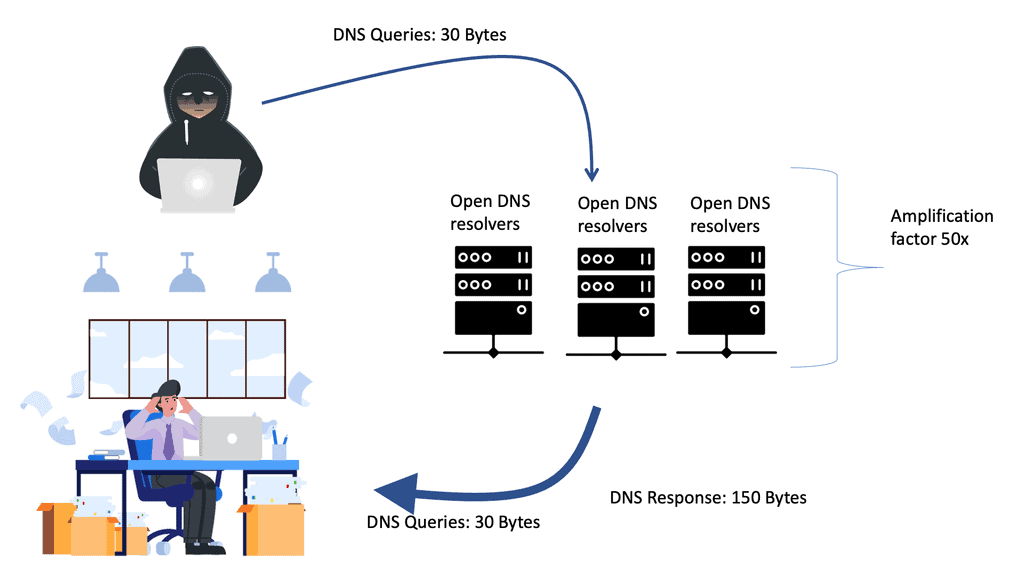
A DNS Reflection Attack, or a DNS amplification attack, is a type of Distributed Denial of Service (DDoS) attack. It exploits the inherent design of the Domain Name System (DNS) to overwhelm a target's network infrastructure. The attacker spoofs the victim's IP address and sends multiple DNS queries to open DNS resolvers, requesting significant DNS responses. The amplification factor of these responses can be several times larger than the original request, leading to a massive influx of traffic directed at the victim's network.
DNS reflection attacks exploit the inherent design of the Domain Name System (DNS) to amplify the impact of an attack. By sending a DNS query with a forged source IP address, the attacker tricks the DNS server into sending a larger response to the targeted victim.
One of the primary dangers of DNS reflection attacks lies in the amplification factor they possess. With the ability to multiply the size of the response by a significant factor, attackers can overwhelm the victim's network infrastructure, leading to service disruption, downtime, and potential data breaches.
DNS reflection attacks can target various sectors, including but not limited to e-commerce platforms, financial institutions, online gaming servers, and government organizations. The vulnerability lies in misconfigured DNS servers or those that haven't implemented necessary security measures.
To mitigate the risk of DNS reflection attacks, organizations must implement a multi-layered security approach. This includes regularly patching and updating DNS servers, implementing ingress and egress filtering to prevent IP address spoofing, and implementing rate-limiting or response rate limiting (RRL) techniques to minimize amplification.
Addressing the DNS reflection attack threat requires collaboration among industry stakeholders. Organizations should actively participate in industry forums, share threat intelligence, and adhere to recommended security standards such as the BCP38 Best Current Practice for preventing IP spoofing.
DNS reflection attacks pose a significant threat to the stability and security of network infrastructures. By understanding the nature of these attacks and implementing preventive measures, organizations can fortify their defenses and minimize the risk of falling victim to such malicious activities.
Matt Conran
Highlights: DNS Reflection attack
Understanding DNS Reflection
1: -) The Domain Name System (DNS) serves as the backbone of the internet, translating human-readable domain names into IP addresses. However, cybercriminals have found a way to exploit this system by leveraging reflection attacks. DNS reflection attacks involve the perpetrator sending a DNS query to a vulnerable server, with the source IP address spoofed to appear as the victim’s IP address. The server then responds with a much larger response, overwhelming the victim’s network and causing disruption and loss of service.
**Distributed Attacks**
2: -) Attackers often use botnets to distribute the attack traffic across multiple sources to execute a DNS reflection attack, making it harder to trace back to the source. This is known as distributed attacks. By exploiting open DNS resolvers, which respond to queries from any IP address, attackers can amplify the data sent to the victim. This amplification factor significantly magnifies the attack’s impact as the victim’s network becomes flooded with incoming data.
**Attacking the Design of DNS**
3: -) DNS reflection attacks leverage the inherent design of the DNS protocol, capitalizing on the ability to send DNS queries with spoofed source IP addresses. This allows attackers to amplify the volume of traffic directed towards unsuspecting victims, overwhelming their network resources. By exploiting open DNS resolvers, attackers can create massive botnets and launch devastating distributed denial-of-service (DDoS) attacks.
**The Amplification Factor**
4: -) One of the most alarming aspects of DNS reflection attacks is the amplification factor they possess. Through carefully crafted queries, attackers can achieve amplification ratios of several hundred times, magnifying the impact of their assault. This means that even with a relatively low amount of bandwidth at their disposal, attackers can generate an overwhelming flood of traffic, rendering targeted systems and networks inaccessible.
Consequences of DNS reflection attack
– DNS reflection attacks can have severe consequences for both individuals and organizations. The vast amount of traffic generated by these attacks can saturate network bandwidth, leading to service disruptions, website downtime, and unavailability of critical resources.
– Moreover, these attacks can be used as a smokescreen to divert attention from other malicious activities, such as data breaches or unauthorized access attempts.
– While DNS reflection attacks can be challenging to prevent entirely, several measures organizations can take to mitigate their impact can help. Implementing network ingress filtering and rate-limiting DNS responses can help prevent IP spoofing and reduce the effectiveness of amplification techniques.
– Furthermore, regularly patching and updating DNS server software and monitoring DNS traffic for suspicious patterns can aid in detecting and mitigating potential attacks.
Google Cloud DNS
**Understanding the Core Features of Google Cloud DNS**
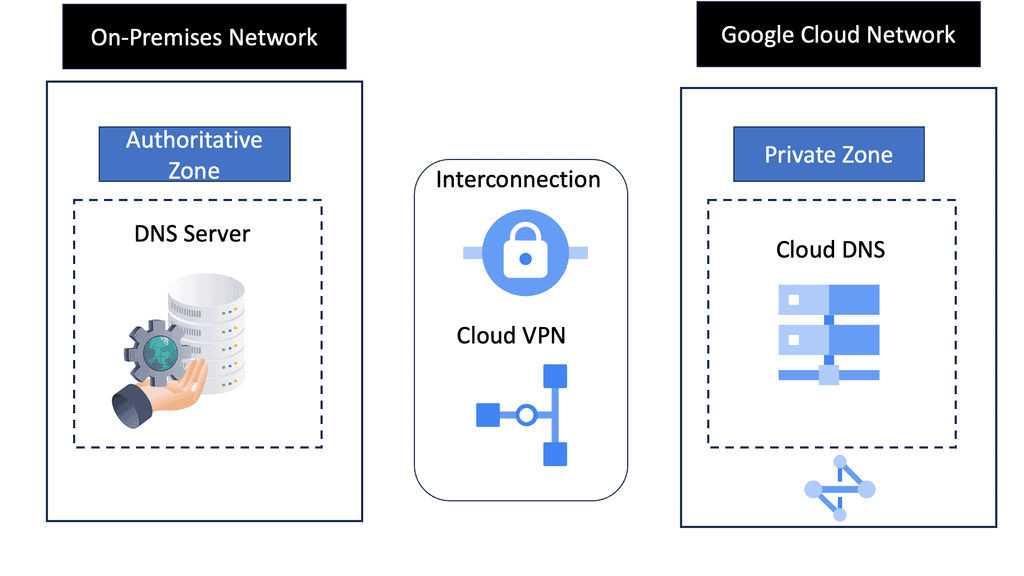
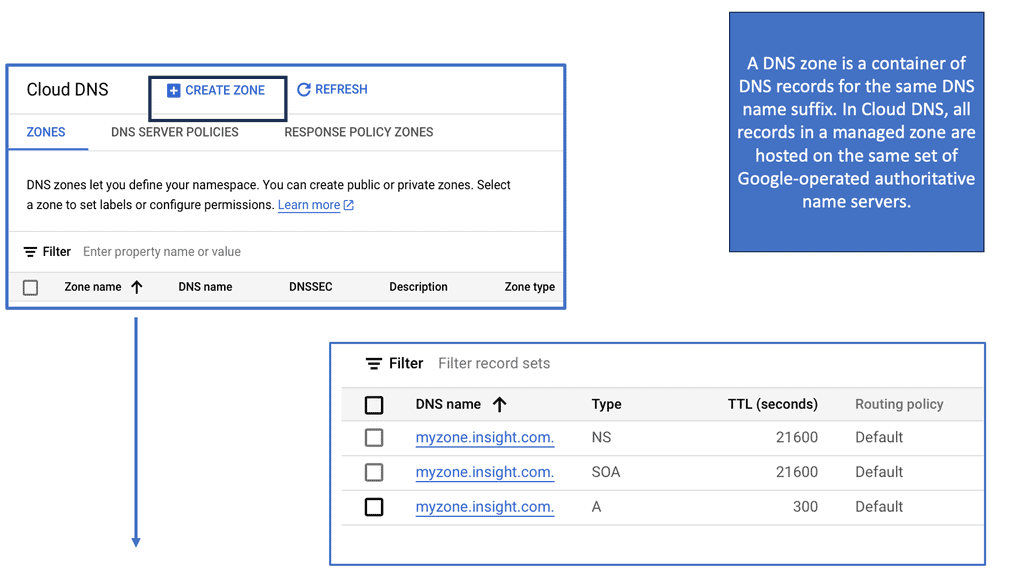
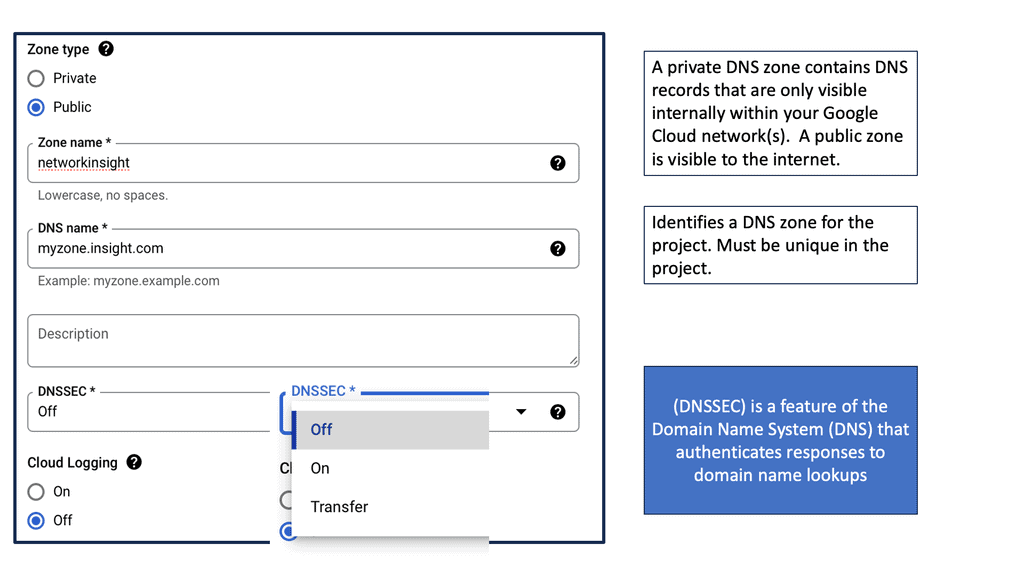
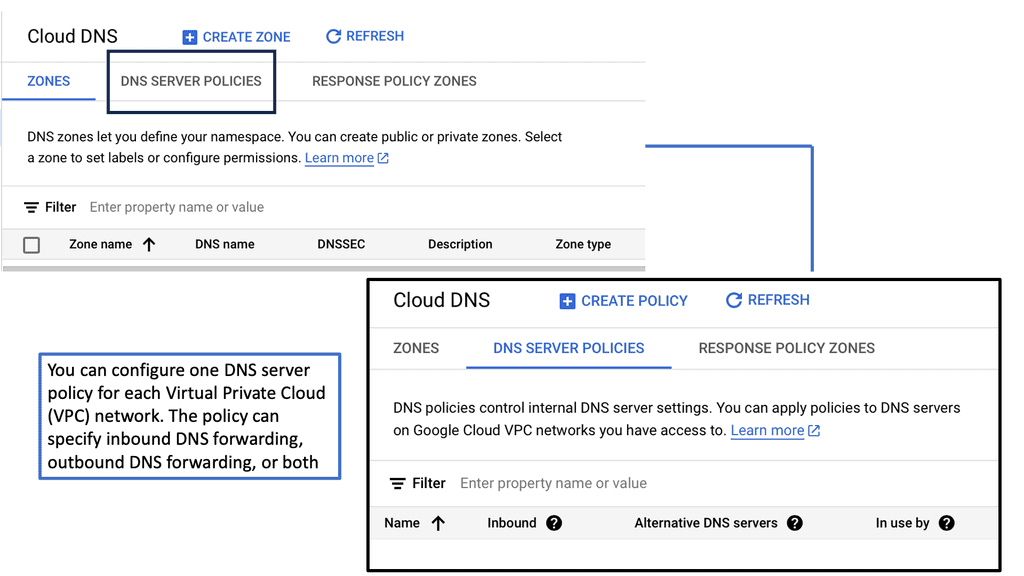
Google Cloud DNS is a high-performance, resilient DNS service powered by Google’s infrastructure. Some of its core features include high availability, low latency, and automatic scaling. It supports both public and private DNS zones, allowing you to manage your internal and external domain resources seamlessly. Additionally, Google Cloud DNS offers advanced features such as DNSSEC for enhanced security, ensuring that your DNS data is protected from attacks.
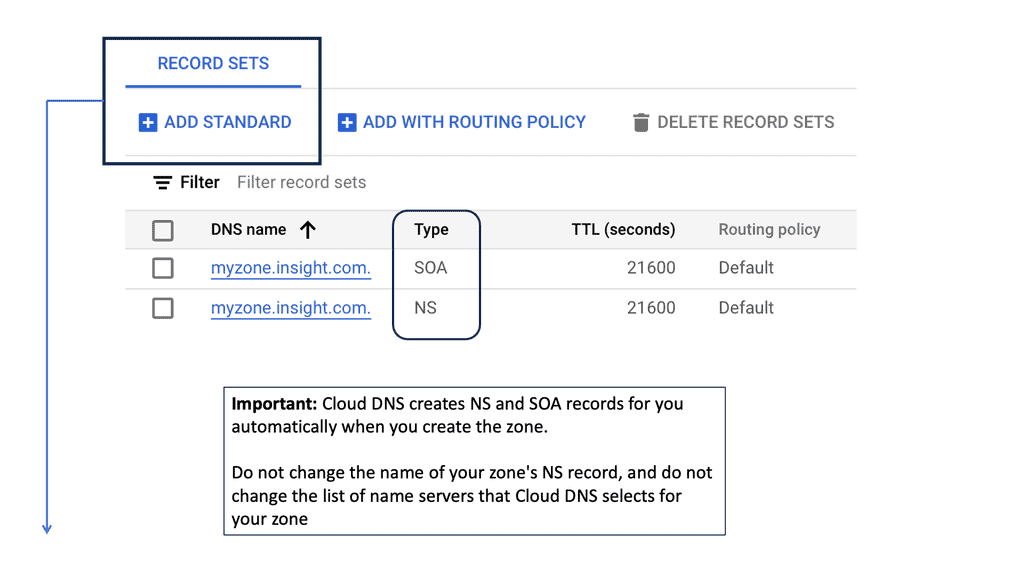
**Setting Up Your Google Cloud DNS**
Getting started with Google Cloud DNS is straightforward. First, you’ll need to create a DNS zone, which acts as a container for your DNS records. This can be done through the Google Cloud Console or using the Cloud SDK. Once your zone is set up, you can start adding DNS records such as A, CNAME, MX, and TXT records, depending on your needs. Google Cloud DNS also provides an easy-to-use interface to manage these records, making updates and changes a breeze.
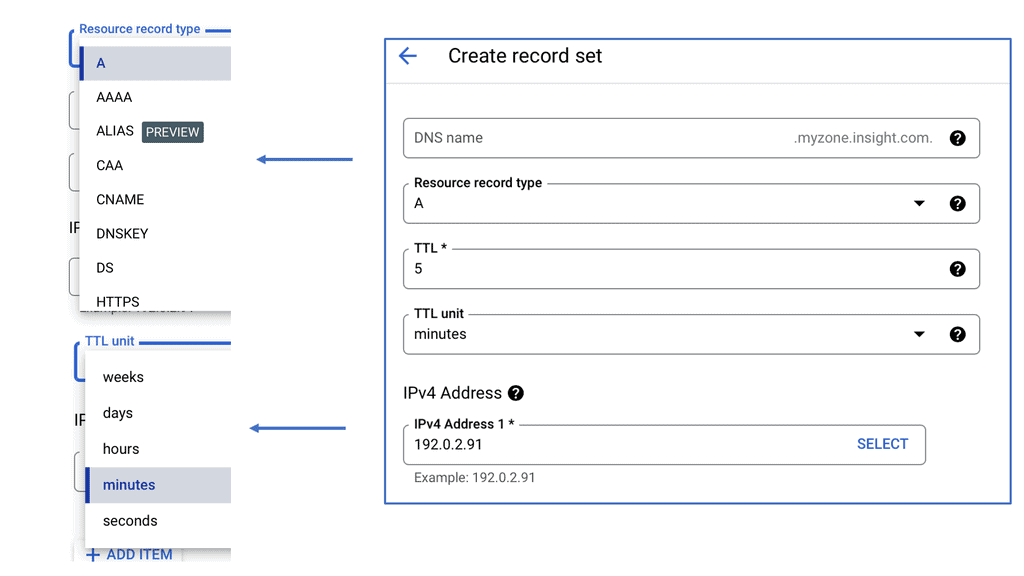
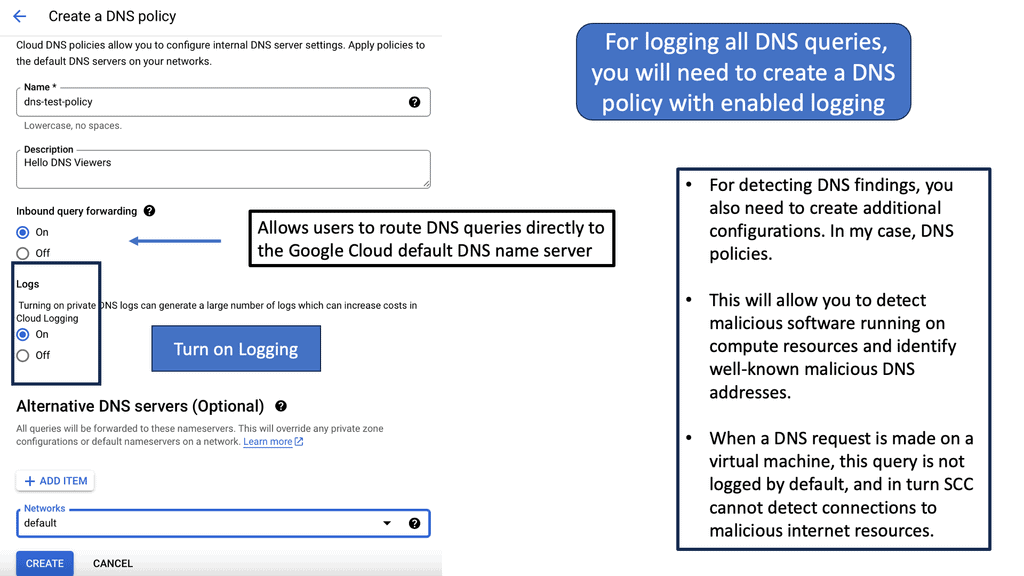
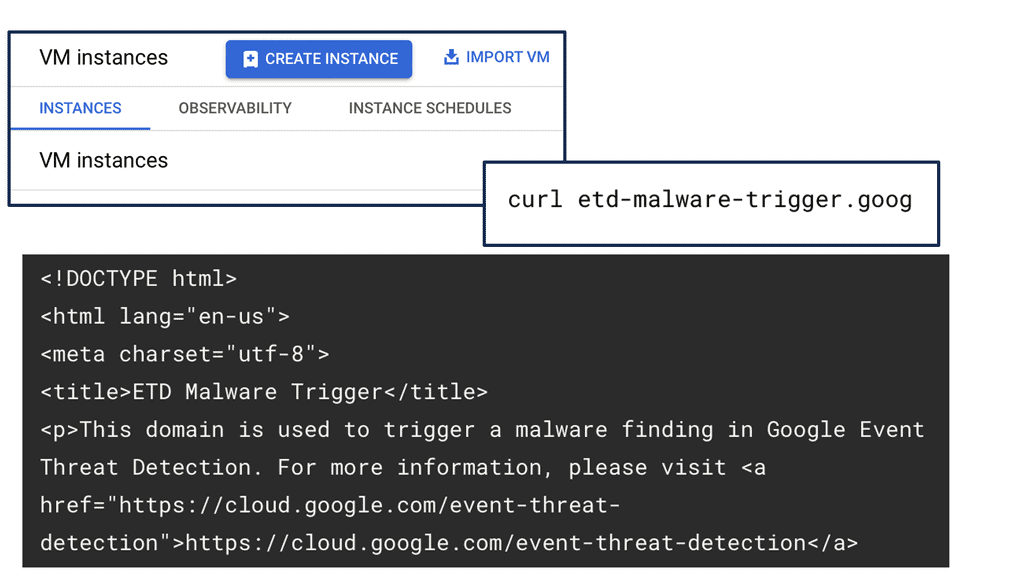
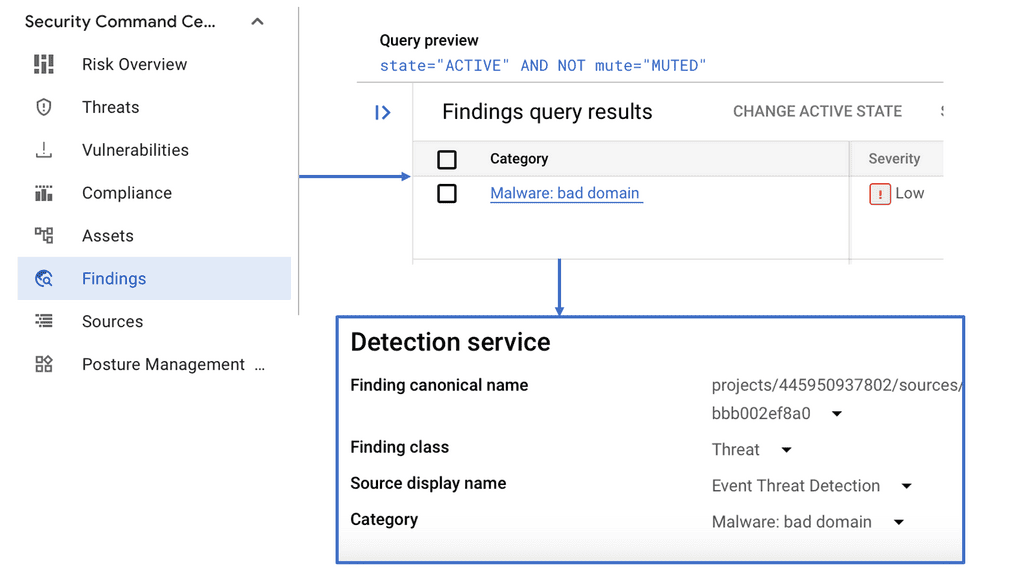
Google Cloud Security Command Center
**Understanding Security Command Center**
Security Command Center is Google’s unified security and risk management platform for Google Cloud. It provides centralized visibility and control over your cloud assets, allowing you to identify and mitigate potential vulnerabilities. SCC offers a suite of tools that help detect threats, manage security configurations, and ensure compliance with industry standards. By leveraging SCC, organizations can maintain a proactive security posture, minimizing the risk of data breaches and other cyber threats.
**The Anatomy of a DNS Reflection Attack**
One of the many threats that SCC can help mitigate is a DNS reflection attack. This type of attack involves exploiting publicly accessible DNS servers to flood a target with traffic, overwhelming its resources and disrupting services. Attackers send forged requests to DNS servers, which then send large responses to the victim’s IP address. Understanding the nature of DNS reflection attacks is crucial for implementing effective security measures. SCC’s threat detection capabilities can help identify unusual patterns and alert administrators to potential attacks.
**Leveraging SCC for Enhanced Security**
Utilizing Security Command Center involves more than just monitoring; it requires strategically configuring its features to suit your organization’s needs. SCC provides comprehensive threat detection, asset inventory, and security health analytics. By setting up custom alerts, organizations can receive real-time notifications about suspicious activities. Additionally, SCC’s integration with other Google Cloud services ensures a seamless security management experience. Regularly updating security policies and conducting audits through SCC can significantly enhance your cloud security strategy.
**Best Practices for Using Security Command Center**
To maximize the benefits of SCC, organizations should follow best practices tailored to their specific environments. Regularly review asset inventories to ensure all resources are accounted for and properly configured. Implement automated response strategies to quickly address threats as they arise. Keep abreast of new features and updates from Google to leverage the latest advancements in cloud security. Training your team to effectively utilize SCC’s tools is also critical in maintaining a secure cloud infrastructure.
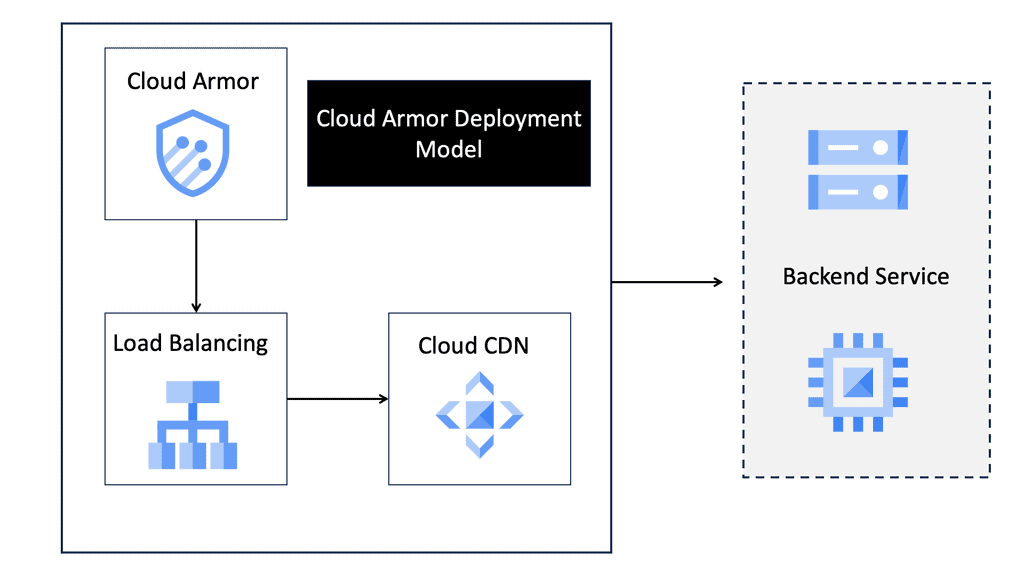
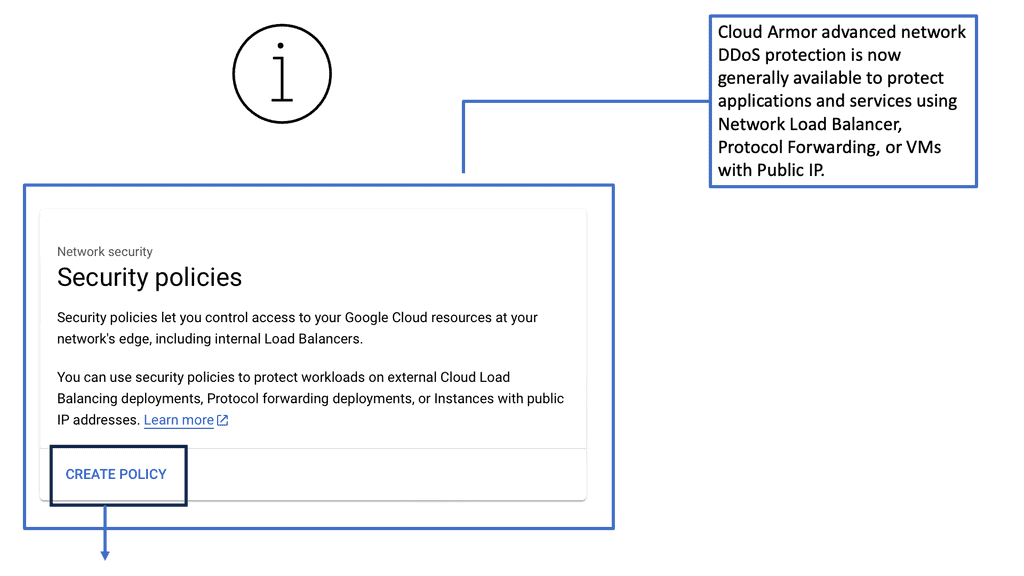
Cloud Armor – Enabling DDoS Protection
*Cloud Armor: The Ultimate Defender**
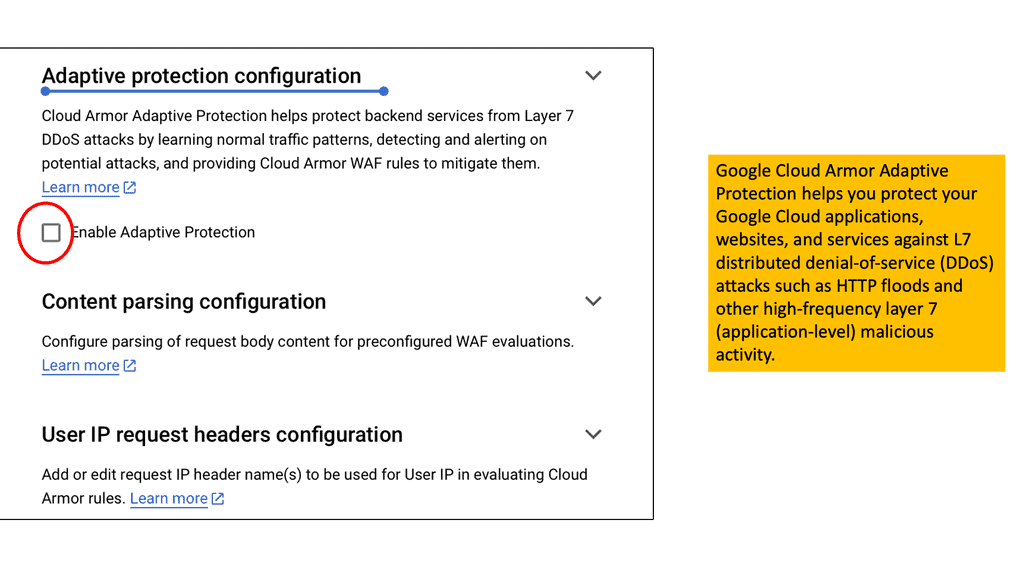
Enter Cloud Armor, a powerful line of defense in the realm of DDoS protection. Cloud Armor is designed to safeguard applications and websites from the barrage of malicious traffic, ensuring uninterrupted service availability. At its core, Cloud Armor leverages Google’s global infrastructure to absorb and mitigate attack traffic at the edge of the network. This not only prevents traffic from reaching and compromising your systems but also ensures that legitimate users experience no disruption.
**How Cloud Armor Mitigates DNS Reflection Attacks**
DNS reflection attacks, a common DDoS attack vector, capitalize on the amplification effect of DNS servers. Cloud Armor, however, is adept at countering this threat. By analyzing traffic patterns and employing advanced filtering techniques, Cloud Armor can distinguish between legitimate and malicious requests. Its adaptive algorithms learn from each attack attempt, continuously improving its ability to thwart DNS-based threats without impacting the performance for genuine users.
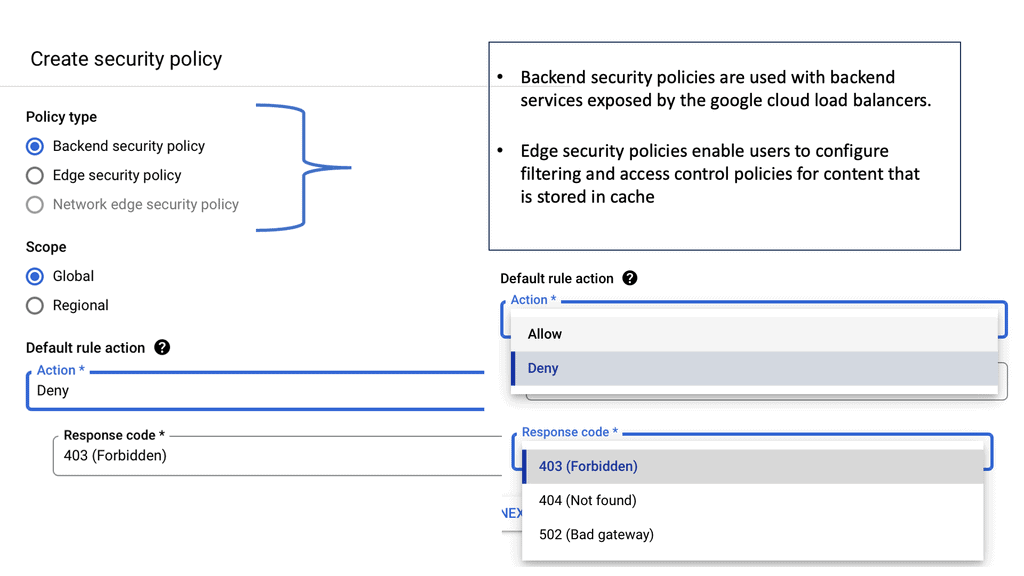
**Implementing Cloud Armor: A Step-by-Step Guide**
Deploying Cloud Armor to protect your digital assets is a strategic decision that involves several key steps:
1. **Assessment**: Begin by evaluating your current infrastructure to identify vulnerabilities and potential entry points for DDoS attacks.
2. **Configuration**: Set up Cloud Armor policies tailored to your specific needs, focusing on rules that address known attack vectors like DNS reflection.
3. **Monitoring**: Utilize Cloud Armor’s monitoring tools to keep an eye on traffic patterns and detect anomalies in real time.
4. **Optimization**: Regularly update your Cloud Armor configurations to adapt to emerging threats and ensure optimal protection.
Example DDoS Technology: BGP FlowSpec:
Understanding BGP Flowspec
BGP Flowspec, or Border Gateway Protocol Flowspec, is an extension to BGP that allows for distributing traffic flow specification rules across network routers. It enables network administrators to define granular traffic filtering policies based on various criteria such as source/destination IP addresses, transport protocols, ports, packet length, DSCP markings, etc. By leveraging BGP Flowspec, network administrators can have fine-grained control over traffic filtering and mitigation of DDoS attacks.
Enhanced Network Security: One of the primary advantages of BGP Flowspec is its ability to improve network security. Organizations can effectively block malicious traffic or mitigate the impact of DDoS attacks in real-time by defining specific traffic filtering rules. This proactive approach to network security helps safeguard critical resources and minimize downtime
DDoS Mitigation: BGP Flowspec plays a crucial role in mitigating DDoS attacks. Organizations can quickly identify and drop malicious traffic at the network’s edge to prevent attacks from overwhelming their network resources. BGP Flowspec allows rapidly deploying traffic filtering policies, providing immediate protection against DDoS threats.
**Combating DNS Reflection Attacks with BGP FlowSpec**
Several measures can be implemented to protect networks from BGP Flowspec and DNS reflection attacks. First, network administrators should ensure that BGP Flowspec is enabled and properly configured on their network devices. This allows for granular traffic filtering and the ability to drop or rate-limit specific traffic patterns associated with attacks.
In addition, implementing robust ingress and egress filtering mechanisms at the network edge is crucial. Organizations can significantly reduce the risk of DNS reflection attacks by filtering out spoofed or illegitimate traffic. Deploying DNS reflection attack mitigation techniques, such as rate limiting or deploying DNSSEC (Domain Name System Security Extensions), can also enhance network security.
Understanding DNS Amplification
Domain names are stored and mapped into IP addresses in the Domain Name System (DNS). As part of a two-step distributed denial-of-service attack (DDoS), DNS reflection/amplification is used to manipulate open DNS servers. Cybercriminals use a spoofed IP address to send massive requests to DNS servers.
Therefore, the DNS server responds to the request and attacks the target victim. Many traffic is sent to the victim server since these attacks are more significant than the spoofed request. An attack can render data entirely inaccessible to a company or organization.
Even though DNS reflection/amplification DDoS attacks are common, they pose a severe threat to an organization’s servers. Massive amounts of traffic pushed into the victim server consume company resources, slowing and paralyzing systems to prevent real traffic from accessing the DNS server.
Combat DNS Reflection/Amplification
1: – DNS Reflectors:
Despite the difficulty of mitigating these attacks, network operators can implement several strategies to combat them. DNS servers should be hosted locally and internally within the organization to reduce the possibility of their own DNS servers being used as reflectors. Additionally, this allows organisations to separate internal DNS traffic from external DNS traffic. Therefore segregating DNS traffic. Therefore allowing them to block unwanted DNS traffic.
2: – Block Unsolicited DNS Replies:
Organizations should block unsolicited DNS replies, allowing only responses requested by internal clients, to protect themselves against DNS reflection/amplification attacks. When DDoS attacks are reflected in DNS Reply sections, detection tools can detect and remove unwanted DNS replies.
Strengthening Your Network Defenses
Several proactive measures can be implemented to protect your network against DNS reflection attacks.
3: – Implement DNS Response Rate Limiting (DNS RRL): DNS RRL is an effective technique that limits the number of responses sent to a specific source IP address, mitigating the amplification effect of DNS reflection attacks.
4: – Employing Access Control Lists (ACLs): By configuring ACLs on your network devices, you can restrict access to open DNS resolvers, allowing only authorized clients to make DNS queries and reducing the potential for abuse by attackers.
5: – Enabling DNSSEC (Domain Name System Security Extensions): DNSSEC adds an extra layer of security to the DNS infrastructure by digitally signing DNS records. Implementing DNSSEC ensures the authenticity and integrity of DNS responses, making it harder for attackers to manipulate the system.
Additionally, deploying firewalls, intrusion prevention systems (IPS), and DDoS mitigation solutions can provide an added layer of defense.
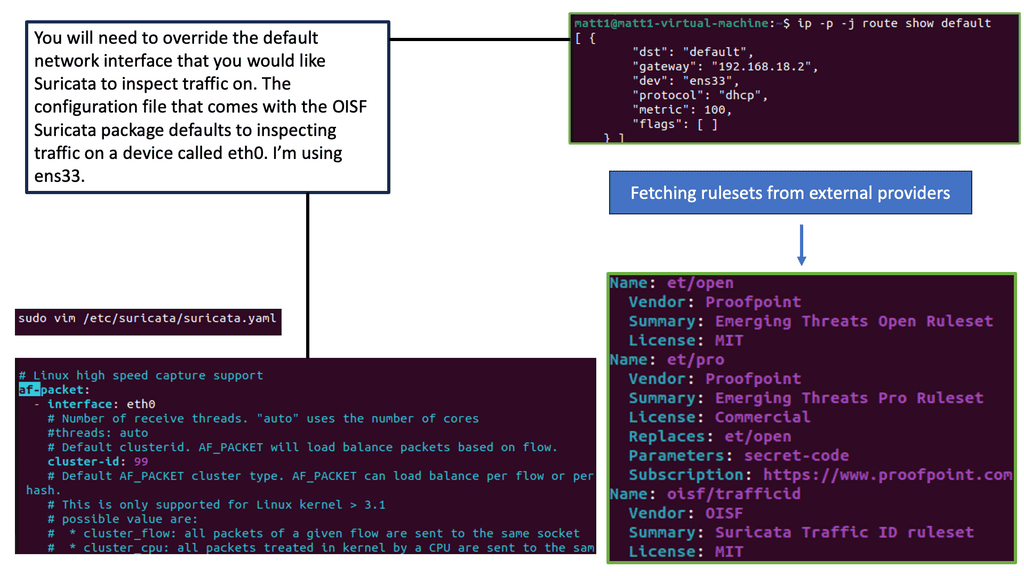
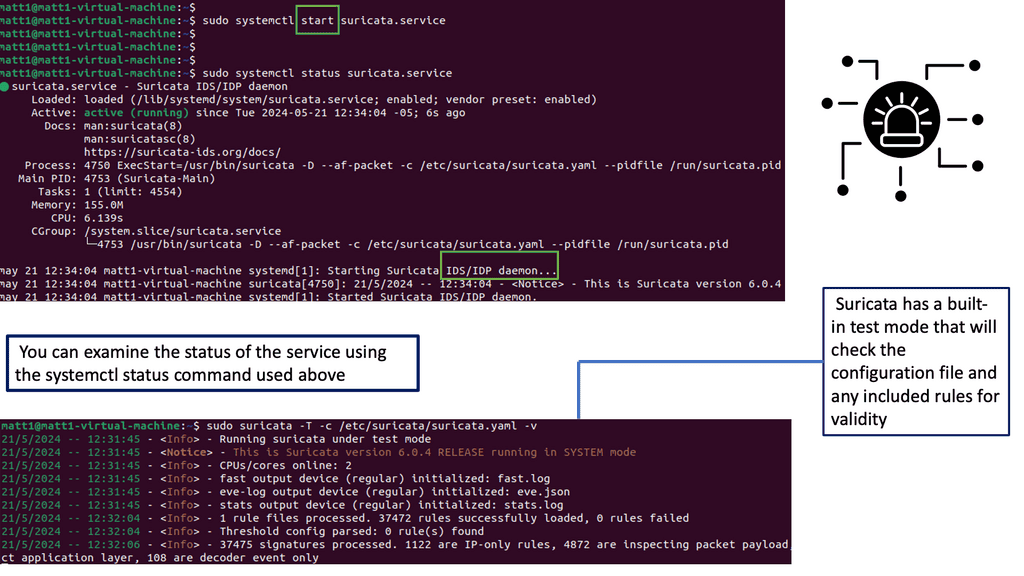
Example IDS Technology: Suricata
### Understanding Suricata IPS
In the rapidly evolving world of cybersecurity, intrusion detection and prevention systems (IDPS) are crucial for safeguarding networks against threats. Suricata, an open-source engine, stands out as a versatile tool for network security. Developed by the Open Information Security Foundation (OISF), Suricata offers robust intrusion prevention system (IPS) capabilities that help organizations detect and block malicious activities effectively. Unlike traditional systems, Suricata provides multi-threaded architecture, enabling it to handle high throughput and complex network environments with ease.
### Key Features of Suricata IPS
Suricata boasts a range of features that make it a powerful ally in network security. One of its standout capabilities is deep packet inspection, which allows it to scrutinize data packets for any suspicious content. Additionally, Suricata supports a wide array of protocols, making it adaptable to various network architectures. Its rule-based language, compatible with Snort rules, provides flexibility in defining security policies tailored to specific organizational needs. Moreover, Suricata’s ability to generate alerts and logs in multiple formats ensures seamless integration with existing security information and event management (SIEM) systems.
### Implementing Suricata in Your Network
Deploying Suricata IPS in your network involves several key steps. First, assess your network infrastructure to determine the optimal placement of the Suricata engine for maximum effectiveness. Typically, it is positioned at strategic points within the network to monitor traffic flow comprehensively. Next, configure Suricata with appropriate rulesets, either by utilizing available community rules or customizing them to address specific threats pertinent to your organization. Regular updates and fine-tuning of these rules are essential to maintain the system’s efficacy in detecting emerging threats.
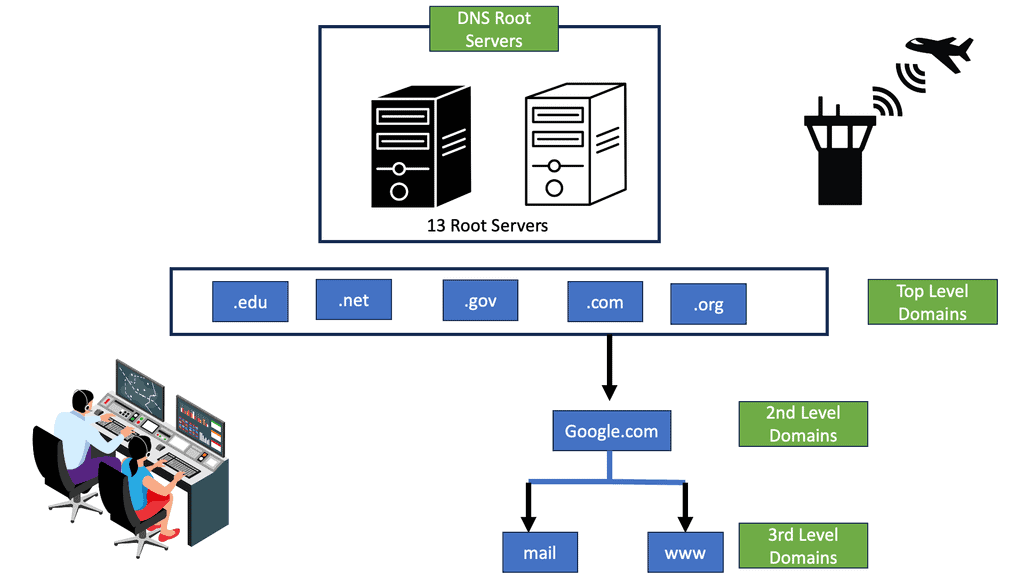
The Role of DNS
Firstly, the basics. DNS (Domain Name System) is a host-distributed database that converts domain names to IP addresses. Most clients rely on DNS for communicating services such as Telnet, file transfer, and HTTP web browsing. It goes through a chain of events, usually only taking milliseconds for the client to receive a reply. Quick does not often mean secure. First, let us examine the DNS structure and DNS operations.
The DNS Process
The clients send a DNS query to a local DNS server (LDNS), a Resolver. Then, the LDNS relays the request to a Root server with the required information to service the request. Root servers are a critical part of Internet architecture.
They are authoritative name servers that serve the DNS root zone by directly answering requests or returning a list of authoritative nameservers for the appropriate top-level domain (TLD). Unfortunately, this chain of events is the base of DNS-based DDoS attacks such as the DNS Recursion attack.
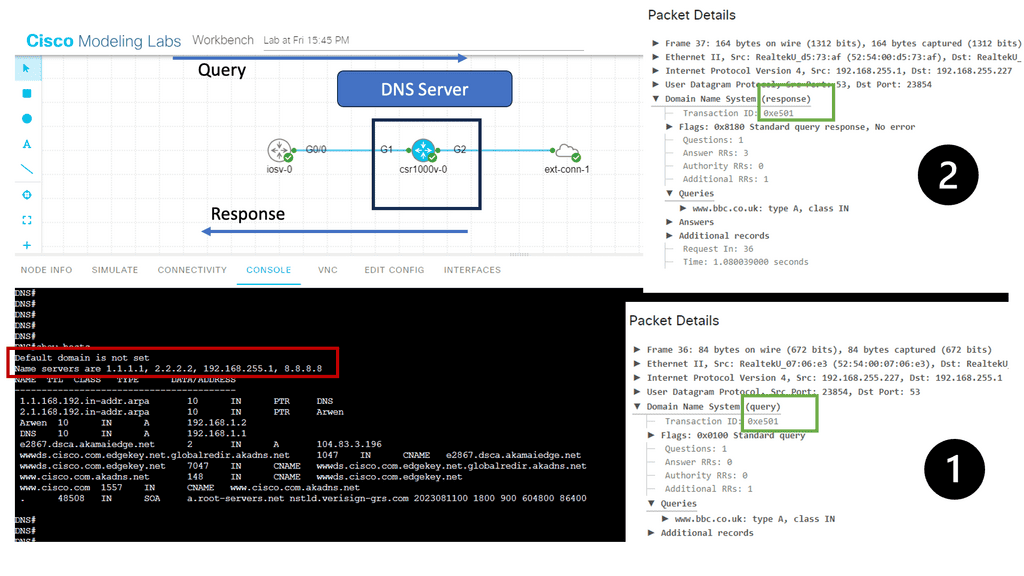
Guide on the DNS Process.
The DNS resolution process begins when a user enters a domain name in their browser. It involves several steps to translate the domain name into an IP address. In the example below, I have a CSR1000v configured as a DNS server and several name servers. I also have an external connector configured with NAT for external connectivity outside of Cisco Modelling Labs.
- Notice the DNS Query and the DNS Response from the Packet Capture. Keep in mind this is UDP and, by default, insecure.
Before you proceed, you may find the following posts useful for pre-information:
The Domain Namespace
So, we have domain names that index DNS’s distributed database. Each domain name is a path in a large inverted tree called the domain namespace. So, when you think about the tree’s hierarchical structure, it is similar to the design of the Unix filesystem.
The tree has a single root at the top. So, the Unix filesystem represents the root directory by a slash (/). So, we have DNS that calls and refers to it as “the root.” But it’s a similar structure that, too, has limits. The DNS’s tree can branch any number of ways at each intersection point or node. However, the depth of the tree is limited to 127 levels, which you are not likely to reach.
DNS and its use of UDP
DNS uses User Datagram Protocol (UDP) as the transport protocol. UDP is a lot faster than TCP due to its stateless operation. Stateless means no connection state is maintained between UDP peers. It has no connection information, just a query/response process.
**Size of unfragmented UDP packets
One problem with using UDP as the transport protocol is that the size of unfragmented UDP packets has limited the number of root server addresses to 13. To alleviate this problem, root server IP addressing is based on Anycast, permitting the number of root servers to be larger than 500. Anycast permits the same IP address to be advertised from multiple locations.
Understanding DNS Reflection Attack
The attacker identifies vulnerable DNS resolvers that can be abused to amplify the attack. These resolvers respond to DNS queries from any source without proper source IP address validation. By sending a small DNS request with the victim’s IP address as the source, the attacker tricks the resolver into sending a much larger response to the victim’s network. This amplification effect allows attackers to generate a significant traffic volume, overwhelming the victim’s infrastructure and rendering it inaccessible.
DNS Reflection Attacks can have severe consequences, both for individuals and organizations. Some of the critical impacts include:
- Disruption of Online Services:
The attack can destroy websites, online services, and other critical infrastructure by flooding the victim’s network with massive amplified traffic. This can result in financial losses, reputational damage, and significant user inconvenience.
- Collateral Damage:
In many cases, DNS Reflection Attacks can have collateral damage, affecting the intended target and other systems sharing the same network infrastructure. This can lead to a ripple effect, causing cascading failures and disrupting multiple online services simultaneously.
- Loss of Confidentiality:
During a DNS Reflection Attack, attackers exploit chaos and confusion to gain unauthorized access to sensitive data. This can include stealing user credentials, financial information, or other valuable data, further exacerbating the damage caused by the attack.
To mitigate the risk of DNS Reflection Attacks, organizations should consider implementing the following measures:
- Source IP Address Validation:
DNS resolvers should be configured to only respond to queries from authorized sources, preventing the use of open resolvers for amplification attacks.
- Rate Limiting:
By implementing rate-limiting mechanisms, organizations can restrict the number of DNS responses sent to a particular IP address within a given time frame. This can help mitigate the impact of DNS Reflection Attacks.
- Network Monitoring and Traffic Analysis:
Organizations should regularly monitor their network traffic to identify suspicious patterns or abnormal spikes in DNS traffic. Advanced traffic analysis tools can help detect and mitigate DNS Reflection Attacks in real-time.
- DDoS Mitigation Services:
Engaging with reputable DDoS mitigation service providers can offer additional protection against DNS Reflection Attacks. These services employ sophisticated techniques to identify and filter malicious traffic, ensuring the availability and integrity of online services.
Exploiting DNS-Based DDoS Attacks
Attacking UDP
Mainly, denial of service (DoS) mechanisms disrupt activity and prevent upper-layer communication between hosts. Attacking UDP is often harder to detect than general DoS resource saturation attacks. Attacking UDP is not as complex as attacking TCP because UDP has no authentication and is connectionless.
This makes it easier to attack than some application protocols, which usually require authentication and integrity checks before accepting data. The potential threat against DNS is that it relies on UDP and is subject to UDP control plane threats. Launching an attack on a UDP session can be achieved without application awareness.
1: **DNS query attack**
One DNS-based DDoS attack method is carrying out a DNS query attack. The attacker uses a tap client and sends a query to a remote DNS server to overload it with numerous clients, sending queries to the same DNS server. The capacity of a standard DNS server is about 150,000 queries. If the remote server does not have the capacity, it will drop and ignore the legitimate request and be unable to send responses. The DNS server cannot tell which query is good or bad. A query attack is a relatively simple attack.
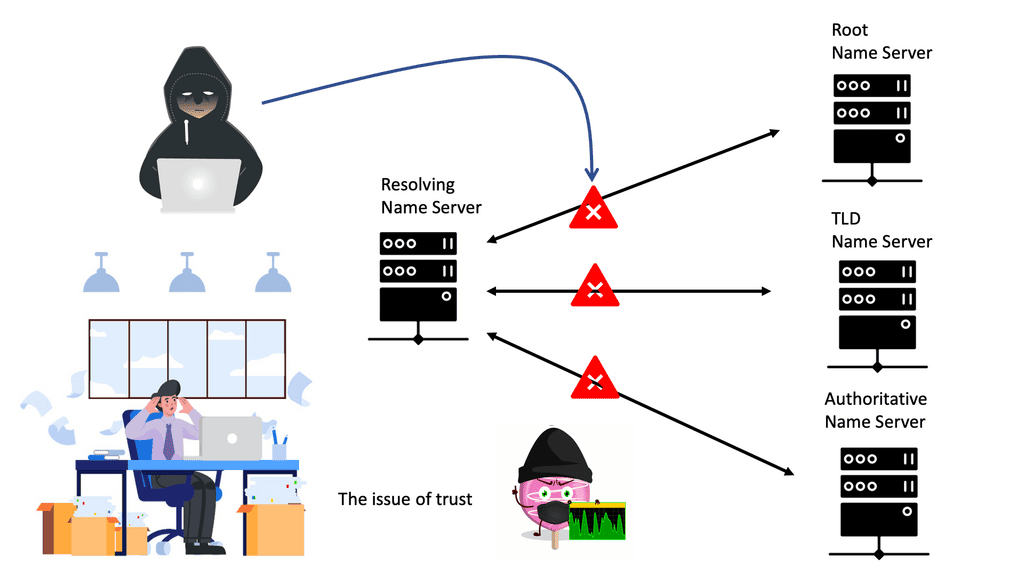
2: **DNS Recursion attack**
The recursive nature of DNS servers enables them to query one another to locate a DNS server with the correct IP address or to find an authoritative DNS server that holds the canonical mapping of the domain name to its IP address. The very nature of this operation opens up DNS to a DNS Recursion Attack.
A DNS Recursion Attack is also known as a DNS cache poisoning attack. DNS attacks occur when a recursive DNS server requests an IP address from another; an attacker intercepts the request and gives a fake response, often the IP address for a malicious website.
3: **DNS reflection attack**
A more advanced form of DNS-based DDoS attacks is a technique called a DNS reflection attack. The attackers take advantage of the underlying vulnerability in the DNS protocol. The return address (source IP address in the query) is tricked into being someone else. This is known as DNS Spoofing or DNS cache poisoning.
The attackers send out a DNS request and set the IP address as their target for the source IP. The natural source gets overwhelmed with return traffic, and the source IP address is known to be spoofed.
The main reason for carrying out reflection attacks is an amplification. The advertisement of spoofed DNS name records enables the attacker to carry out many other attacks. As discussed, they can redirect flows to a destination of choice, which opens up other sophisticated attacks that facilitate eavesdropping, MiTM attacks, the injection of false data, and the distribution of Malware and Trojans.
DNS and unequal sizes
IPv4 & IPv6 Amplification Attacks
The nature of the DNS system is that it has unequal sizes. The query messages are tiny, and the response is typically double the query size. However, there are certain record types that you can ask for that are much more significant. Attackers may concentrate their attack using DNS security extension (DNSSEC) cryptographic or EDNS0 extensions. If you add DNSsec, it combines a lot of keys and makes the packet much larger.
These requests can increase packet size from around 40 bytes to above the maximum Ethernet packet size of 4000. They potentially require fragmentation, further targeting network resources. This is the essence of any IPv4 and IPv6 attack amplification: a small query with a significant response. Many load balancing products have built-in DoS protection, enabling you to set limits for packets per second on specific DNS queries.
Amplified with DNS Open Resolvers
The attack can be amplified even more with DNS Open Resolvers, enabling the least number of Bots with maximum damage. A Bot is a type of Malware that allows the attacker to control it. Generally, a security mechanism should be in place so resolvers only answer requests from a list of clients. These are called locked or secured DNS resolvers.
Unfortunately, many resolvers lack best-practice security mechanisms. Unfortunately, Open Resolvers amplify the amplification attack surface even further. DNS amplification is a variation of an old-school attack called an SMURF attack.
At a fundamental level, ensure you have an automated list to accept only known clients. Set up ingress filtering to ensure you don’t have an illegal address leaving your network. Ingress filtering prevents any spoofing-style attacks. This will weed it down and thin it out a bit.
Next, test your network and make sure you don’t have any Open Resolvers. NMAP (Network Mapper) is a tool with a script to test recursion. This will test whether your local DNS servers are open to recursion attacks.
Example DDOS Protection: GTM Load Balancer
At a more expensive level, F5 offers a product called DNS Express. It allows you to withstand DoS attacks by adding an F5 GTM Load Balancer to your DNS servers. DNS Express handles the request on behalf of the DNS server. It works from high-speed RAM and, on average, handles about 2 million requests per second.
This is about 12 times more than a regular DNS server, which should be enough to withstand a sophisticated DNS DoS attack. Later posts deal with mitigation techniques, including stateful firewalls and other devices.
Closing Points on DNS Reflection Attack
A DNS Reflection Attack is a type of Distributed Denial of Service (DDoS) attack that leverages the Domain Name System (DNS) to overwhelm a target with traffic. The attacker sends a small query to a DNS server, spoofing the IP address of the victim. The server, in turn, responds with a much larger packet, sending it to the victim’s address. By exploiting numerous DNS servers, an attacker can amplify the volume of data directed at the target, effectively crippling their services.
The mechanics of a DNS Reflection Attack are both clever and destructive. At its core, the attack relies on two primary components: spoofing and amplification. Here’s a step-by-step breakdown of the process:
1. **Spoofing**: The attacker sends DNS requests to multiple open DNS resolvers, using the victim’s IP address as the source address.
2. **Amplification**: These DNS requests are crafted to trigger large responses. A small request can generate a response that is several times larger, due to the nature of DNS queries and responses.
3. **Reflection**: The DNS servers send the amplified responses to the victim’s IP address, inundating their network with data and leading to service disruption.
The consequences of a successful DNS Reflection Attack can be severe, affecting not only the direct victim but also the broader network infrastructure. Some of the notable impacts include:
– **Service Downtime**: The primary goal of a DNS Reflection Attack is to render services unavailable. This can lead to significant financial losses and damage to reputation for businesses.
– **Network Congestion**: The flood of traffic can cause congestion on the network, affecting legitimate users and potentially leading to further delays and outages.
– **Collateral Damage**: Open DNS resolvers used in the attack can also face repercussions, as they become unwitting participants in the attack, consuming resources and bandwidth.
Protecting against DNS Reflection Attacks requires a multi-layered approach, combining best practices and technological solutions. Here are some effective strategies:
– **Implement Rate Limiting**: Configure DNS servers to limit the number of responses sent to a single IP address within a specific timeframe, reducing the potential for amplification.
– **Use DNSSEC**: DNS Security Extensions (DNSSEC) add a layer of authentication to DNS responses, making it more difficult for attackers to spoof source IP addresses.
– **Deploy Firewalls and Intrusion Detection Systems (IDS)**: These tools can help identify and filter out malicious traffic, preventing it from reaching the intended target.
– **Close Open Resolvers**: Ensure that DNS servers are not open to the public, limiting their use to authorized users only.
Summary: DNS Reflection attack
In the vast realm of the internet, a fascinating phenomenon known as DNS reflection exists. This intriguing occurrence has captured the curiosity of tech enthusiasts and cybersecurity experts alike. In this blog post, we embarked on a journey to unravel the mysteries of DNS reflection and shed light on its inner workings.
Understanding DNS
Before diving into the intricacies of DNS reflection, it is essential to grasp the basics of DNS (Domain Name System). DNS serves as the backbone of the internet, translating human-readable domain names into IP addresses that computers can understand. It acts as a directory, facilitating seamless communication between devices across the web.
The Concept of Reflection
Reflection, in the context of DNS, refers to the bouncing back of packets between different systems. It occurs when a DNS server receives a query and responds by sending a more significant response to an unintended target. This amplification effect can lead to potentially devastating consequences if exploited by malicious actors.
Amplification Attacks
One of the most significant threats associated with DNS reflection is the potential for amplification attacks. Cybercriminals can leverage this vulnerability to launch large-scale distributed denial of service (DDoS) attacks. By spoofing the source IP address and sending a small query to multiple DNS servers, they can provoke a deluge of amplified responses to the targeted victim, overwhelming their network infrastructure.
Mitigation Strategies
Given the potential havoc that DNS reflection can wreak, it is crucial to implement robust mitigation strategies. Network administrators and cybersecurity professionals can take several proactive steps to protect their networks. These include implementing source IP verification, deploying rate-limiting measures, and utilizing specialized DDoS protection services.
Conclusion
In conclusion, DNS reflection poses a significant challenge in cybersecurity. By understanding its intricacies and implementing appropriate mitigation strategies, we can fortify our networks against potential threats. As technology evolves, staying vigilant and proactive is paramount in safeguarding our digital ecosystems.